 A new remote access trojan (RAT) called ‘KilerRat’ has built upon the capabilities of njrat to become a feature-rich, sophisticated spying tool.
A new remote access trojan (RAT) called ‘KilerRat’ has built upon the capabilities of njrat to become a feature-rich, sophisticated spying tool.
According to a post published on AlienVault’s blog, the RAT does share some commonalities with njrat:
“Like njrat, the infected victims of KilerRat when connecting to the C&C will send information about the victim system, malware version, open windows, etc.,” writes AlienVault researcher Peter Ewane. “This information check-in is extremely similar to that of many of the njrat variants.”
Where KilerRat distinguishes itself, however, is its variety of abilities, a multi-functionality which is quickly gaining the tool popularity within the Middle Eastern hacking world.
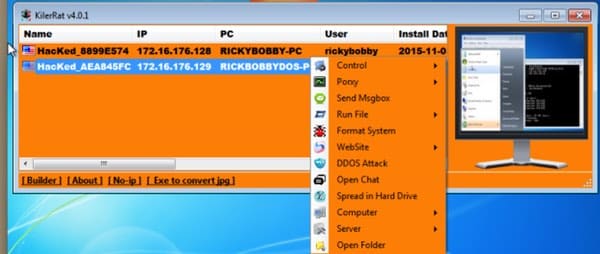
Under the Command and Control (C&C) server, for example, an operator can initiate the following commands, among others:
- File Manger – Allows the attacker to edit, create, delete, copy, or download new files/folders.
- Remote Desktop – Allows the attacker to begin a Remote Desktop session.
- Get Passwords – Allows the attacker to save passwords that have been stored in several browsers.
- Send Msgbox From Link – Allows the attacker to provide a link to a file and execute it on the infected machine
- Format System: Open/Block Website – Allows an attacker to open or block a website of their choosing.
- DDoS Attack – Allows the attacker to perform a DDoS attack according to specifications of their choosing.
Though it is based upon njrat, many anti-virus companies appear – at the time of writing – to be doing a poor job of identifying the malware.
Ewane does point out, however, that using YARA rules for njrat as well as a signature-based IDS tool could reveal a KilerRat infection more consistently.
As noted by Softpedia, one of the most interesting features of this RAT is not anything malicious but instead the fact that the malware’s author provides a link in the tool’s “About” section to a Facebook profile.

The Facebook profile gives the author’s name as “Ahmed Ibrahim”.

Most of the comments on Ibrahim’s Facebook posts thank the hacker for producing KilerRat or ask that additional features be included.
A closer look of his posts reveals that Ibrahim released KillerRat version 4.0.1 (the latest detected) on October 30, version 3.1.6 on October 23, and version 2.9.6 on October 18. It is also apparent that Ibrahim might be working on a new tool called the Wedges Worm.
When it comes to new tools and exploits, bravado is never hard to find in the hacking world. Perhaps Ibrahim’s decision to post his Facebook profile will come back to bite him in the end.
In the meantime, please install a security solution and never click on suspicious links.



I think it's kinda funny that you scanned it on refud.me when you could scan it on VirusTotal and get it distributed for a higher detection rate.
That's a screenshot Alienvault took of detection rates, not something myself or David Bisson produced.
I see when checking the MD5 on VirusTotal that it has been uploaded there too:
https://www.virustotal.com/latest-scan/51409b4216065C530a94cd7a5687c0d6
Judging by that VirusTotal report, products are catching up…
The link shows the results for v3.16 with most dates showing November 16, 2015 (4 days ago, so very recent). Any news on v4.01?
'Perhaps Ibrahim's decision to post his Facebook profile will come back to bite him in the end.'
Most probably the case. Whether it will mean much in practise is another matter entirely. Once the cat is out of the bag (or is that 'rat out of the field' ?) the damage is done. More people will also take his place but meanwhile the software is already published – and depending on its openness it would be easy to extend (not to say closed source can't easily enough be extended but it isn't as easy if it is open source). At the same time, it has a user base…