Authorities have brought down an international group of computer criminals following a series of malware-based attacks that compromised ATMs all across Europe.
Composed of eight Romanian and Moldovan nationals, the group was taken into custody for a “jackpotting” campaign that allowed the attackers to literally empty cash machines located in several different European countries.
The Romanian National Police and the Directorate for Investigating Organized Crimes and Terrorism (DIICOT) explains in a press release that the group carried out its attacks on weekends, presumably with the intention of avoiding attracting foot traffic.
Each hit consisted of a member of the group gaining access to an ATM machine’s CD-ROM drive and inserting a disc containing Tyupkin malware.
First discovered by Kaspersky Lab researchers back in the fall of 2014, Tyupkin is a form of malware specifically designed to target ATMs.
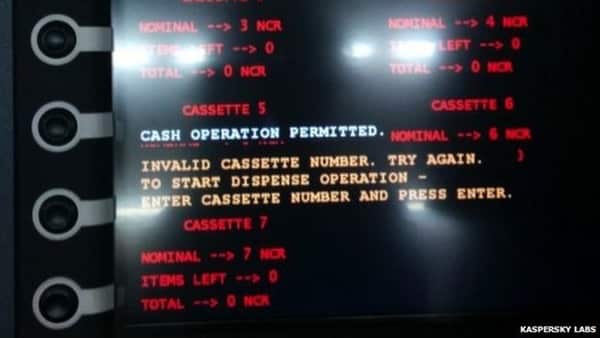
The malware avoids detection, Kaspersky’s researchers explain, by activating only at a certain time of night and by using a key generated from a random seed for each session. If the key is entered correctly, an attacker can use the malware to see how much money is stored on each cassette and subsequently withdraw 40 banknotes from a targeted cassette.
A video of Tyupkin in action can be viewed in the following YouTube video:
In each separate attack, the group allegedly cut the internet connection to the target ATM and secured the cash dispenser’s alarm with adhesive tape before making off with approximately €900.
This level of caution was evident in much of their early hits, which targeted machines located primarily in Romania.
But then the group got cocky. Not only did they expand their malware attacks to other European countries, writes Andrada Fiscutean of ZDNet, but the gang also allegedly began discussing their campaign on Facebook Messenger and Skype, thereby creating an electronic trail which ultimately led Romanian and Moldovan authorities right to their doorsteps.
It is these types of operations (not to mention stupid mistakes on the parts of criminals) that prove just how crucial it is for law enforcement authorities to cooperate together in the face of computer crime. says Wil van Gemert, Europol’s deputy director of Operations, in a statement:
“Over the last few years we have seen a major increase in ATM attacks using malicious software. The sophisticated cybercrime aspect of these cases illustrates how offenders are constantly identifying new ways to evolve their methodologies to commit crimes. To match these new technologically savvy criminals, it is essential, as it was done in this case, that law enforcement agencies cooperate with their counterparts via Europol to share information and collaborate on transnational investigations”.

This type of collaboration will no doubt serve authorities well in their fight against other types of ATM malware, including GreenDispenser, which was discovered by researchers last fall. Hopefully in those cases, too, the attackers will make similarly stupid mistakes and find themselves behind bars before they know what hit them.


… One down…many more (presumably also some future groups) to go, I'm sure …
Yet it's a good thing that at least one was shut down.