Details have emerged about how the Syrian Electronic Army (SEA) managed to hack into content recommendation service Outbrain, and – in the process – send visitors to popular websites like CNN, The Washington Post and Time magazine on an unexpected journey to the SEA’s site instead.
Details have emerged about how the Syrian Electronic Army (SEA) managed to hack into content recommendation service Outbrain, and – in the process – send visitors to popular websites like CNN, The Washington Post and Time magazine on an unexpected journey to the SEA’s site instead.
And, from the looks of things, it wasn’t a hard stunt for the notorious SEA hacking group to pull off at all.
To their credit, Outbrain has published details of how they were hacked – and shown, once again, that a hack doesn’t need to be sophisticated or ground-breaking to be successful.
As I recently discussed using the example of KPMG, it’s child’s play to find out the names and email addresses of people who work at a company and forge an email address from the chief executive.
All a hacker needs is for one unsuspecting worker to click on a link, believing it to be from one of his bosses or colleagues, and be duped into entering their username and password and… BINGO! The hackers may now have access to your internal systems.
The security issue is obviously compounded if your users are in the habit of using the same password in multiple places – as being phished in one place may have a domino effect.
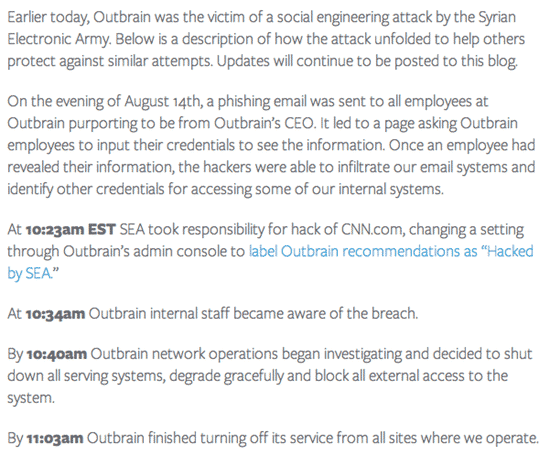
In Outbrain’s case, an email purported to be from the CEO was able to trick at least one employee into entering their password and gave the hackers access to Outbrain’s internal email system. From there they were able to steal more credentials that gave them access to admin panels.
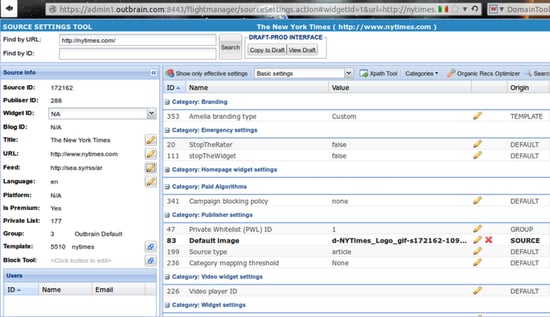
And, it seems, the damage could have been much worse if Outbrain hadn’t shut down its systems so quickly. According to the Syrian Electronic Army (who published screenshots of the Outbrain systems they were able to access), they had almost managed to meddle with the New York Times as well.
Just a few minutes more and it seems clear that the New York Times would have also been hit – which would have had some irony seeing as there were numerous (erroneous) reports the day before that the newspaper had been hacked when it suffered a period of unexpected downtime.
Clearly there are lessons to be learnt from the stream of successful phishing attacks that the Syrian Electronic Army are launching.
All companies need to do a better job of securing their email – using two-factor authentication to supplement the username/password combination would be an excellent start, and make life harder for the account crackers.
Furthermore, users need to be trained to be on the lookout for suspicious emails, even if – at first glance – they appear to have come from colleagues or other respected organisations.
Passwords need to be unique and hard-to-crack, and if good password management software is in place that may help warn users that they’re not on the site that they think they are – and prevent them from entering a password that should remain secret.
With no end in sight of the Syrian Electronic Army’s antics, everyone should be on their guard, and make sure that they are not going to be the weak link in the chain that exposes their company and causes their firm to be the subject of embarrassing headlines.