Many of us have done it.
Rather than emailing a long list of people using the Bcc field, we’ve used Cc instead.
The result? Everyone who receives the email sees the email address of everyone else who has been sent the email.

And that may not be that big a deal if you’re sending an internal email to staff inside your company, but it’s a problem if the people you are emailing are external, and didn’t want their email address to be made public or their relationship with you to be shared with others.
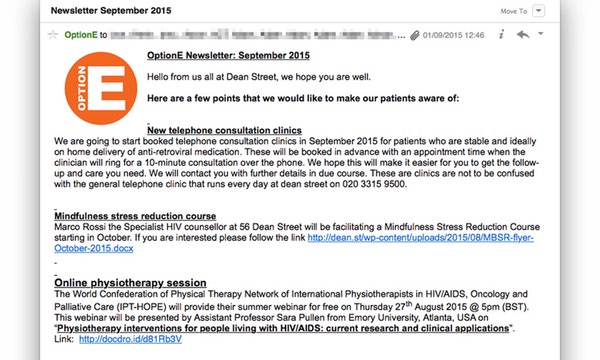
Like, for instance, if the people who made the email blunder were an HIV clinic sending out its newsletter to 780 people.
As The Guardian reports, an inquiry has been ordered into how the 56 Dean Street sexual health clinic in Soho, London – which set a World Record for the most HIV tests performed in one location on World Aids Day in 2011 – managed to disclose the names and email addresses of approximately 780 people.
Health Secretary Jeremy Hunt told delegates at an NHS conference in Manchester that he was ordering an inquiry into the “completely unacceptable” breach:
“Nothing matters more to us than our own health, but we must also understand that for NHS patients nothing matters more to them than confidence that the NHS will look after their own personal medical data with the highest standards of security.
“The truth is the NHS have not won the public’s trust in our ability to do this as today’s completely unacceptable data breach at the Dean Street surgery demonstrates.”
Of course, aside from the privacy breach – these types of email goofs can also potentially assist spammers in targeting individuals with their unwanted marketing messages.
 I’m not sure they need much of an inquiry to work this one out. Someone screwed up and pasted the email addresses into the wrong field.
I’m not sure they need much of an inquiry to work this one out. Someone screwed up and pasted the email addresses into the wrong field.
This wouldn’t have happened if they had used properly configured mailshot software for sending out their newsletters, or if their email client had warned that they had a ridiculously large number of people in the CC field and asked for confirmation that the email really should be sent?
How hard would it be for email systems to make that check? Or even to spot that a large number of people at different domains have been cc’d and perhaps that might indicate a human goof, and a suitable warning message should be displayed?
I also hope the investigation will explore whether the newsletter’s email database was being stored securely or not.
I have no doubt that the classic Cc/Bcc error will continue to be made. Just make sure that you’re always careful when you’re emailing people that you’re not unwittingly breaking their trust.
Read more in the article in The Guardian.



fyi: You've got a typo in the title tag (/identites/identities/).
Thanks Joris – now fixed. :)
Ahhh! the power of decent email services over manual methods!
It boggles me why companies like Dean Street don't use software like MailChimp as they're typically free / low cost and bring a raft of benefits besides addressing the bcc issue: automated unsubscription functionality; more assurance of content accessibility and analytics over your communications.
I always cringe when I see companies send mails with wording like “click here to (un)subscribe”, which generates a mailto: link that informs someone somewhere to update a distribution list. These are typically backed up with “please give 4 weeks for your removal request to take effect”. You know someone somewhere is manually editing a text copy of a distribution list. Which brings its own security implications…
It's an easy mistake to make for an individual but here we're talking about a business and one that provides a particularly sensitive service. It is unacceptable for an organisation like this to not have an email DLP service in place. The two major players: Office 365 and Google Apps BOTH provide DLP functionality. Even if you're using the Outlook desktop application you can get add-ins which complement a DLP service – they'll pop-up to notify you that you're sending to multiple addresses via CC instead of BCC.
The ICO need to fine this business punitively – mainly for the deterrent effect.
"How hard would it be for email systems to make that check?"
As for mail servers, incredibly easy, seeing as how at least some have the functionality built in. The problem is that – and this goes for spam filtering too – the larger the user base, the harder it is to find the right balance; if the mail server is for internal use, for smaller projects (and/or only used by people you know well), then it is a lot easier to be strict. But try it with Gmail, for example, and it becomes much more complicated. As it is, look at the issue you had earlier this year – that's the other thing: false positives are a big problem. Unfortunate as it is, spam filtering will never be perfect (just like malware scanning) and this goes for other types of restrictions/filtering/etc.
But yes, it is an easy mistake to make if you're not really careful. The only time I've done something like this is when something screwy with Thunderbird happened (still don't know what caused it) that messed up my small (only manually added addresses) contact list. Because I was used to typing their name (which is normally safe because I add addresses manually and I add very few), and because I know more than one person by the same name, and because I was (trying) to wake up (early morning), and because I hadn't realised the change before, I sent an email to the wrong person (only one person at least, and someone who I've known for a long time too). I didn't notice it until they responded (and I recognised the response by the message itself as not the one I thought I sent to, and looking at sender it was indeed true). These types of errors are unfortunately really easy to make even if you're really careful (I usually check recipient/subject/body several times before sending) and once you hit send, if you're not quick enough (which is the case if you don't yet realise your error), your mail will be sent to the wrong recipient and/or with the wrong message. Unfortunately there is a lot of stigma in this world, and HIV patients are a victim of more than just the virus – they are a victim of being stigmatised (and potentially afraid of the stigma – not to mention AIDS).
Bottom line is humans aren't perfect and you can only take responsibility and address it (the problem, not the recipient) as best you can (although you could just disregard it if you're afraid to admit you made a mistake or you don't see it as a mistake).
You make a good point about "mailshot software" being an option for avoiding this problem, but in fact it should be the only choice. Using BCC on a standard email client has never guaranteed that all those recipients are hidden from each other – only that they are hidden from the main recipients (TO and CC). The relevant standards (currently rfc 5322) have always warned that whether BCC recipients can see each other is "implementation dependent" – so sometimes it might work the way required here but not always.