You may not be able to visit your local branch of Robert Dyas to pick up some equipment for the DIY project you have undertaken during lockdown, but there are plenty of people who might be ordering goods via its website instead.
And that’s a problem, because the UK DIY, electricals, and houseware chain has revealed in an email to customers that, between 7-30 March 2020, malicious code on Robert Dyas’s payment page was secretly skimming the credit card details of customers and sending them to hackers.
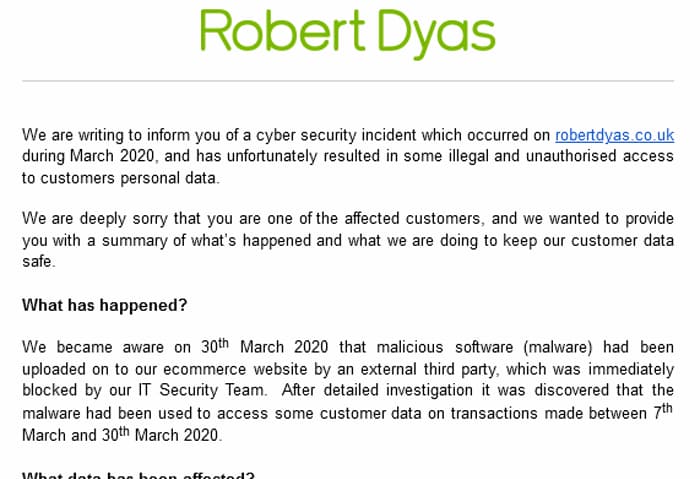
Chances are that the JavaScript code on Robert Dyas’s website was planted there by hackers, either by compromising the company’s website infrastructure or by planting the malicious code in a third-party script used by the site.
Whatever the means, the result is the same – malicious script runs in the user’s browser while visiting a business’s website, and as their personal data and payment card information is entered into an online form it is silently harvested by an unauthorised party.
Robert Dyas says that it has now fixed the vulnerability on its website and “are confident that the incident has been resolved.”
That’s not much comfort for people who purchased goods on the Robert Dyas website during the period of infection, of course. Such customers would be wise to keep a close eye on their financial statements in case there are any unusual transactions.
An FAQ about the security breach has been published on Robert Dyas’s website, although disappointingly they have chosen not to link to it from their homepage where it might have been seen by more customers.
The Information Commissioner’s Office (ICO), the UK’s data regulator, has been informed of the incident, and no doubt they will investigate whether punitive action will need to be taken against the firm for any security failings.
Data swiped by the criminals include details of credit and debit cards, and the names and addresses of customers. According to Robert Dyas, passwords details have not been accessed by the hackers.


