Online extortion can take various forms.
Sometimes the attackers will launch a DDoS attack against your website, and demand that you pay up if you want them to stop. (Of course, it’s a mistake to pay)
Othertimes businesses and end users find that their systems have been hit by ransomware and, in the absence of a secure backup, find themselves having to pay off the internet low-lives who attacked them for the safe return of the encrypted data.
And then there are the hacking gangs who are breaking into businesses, stealing corporate data and email archives, and then threatening to share it with security journalists who will write juicy stories about the information that has been stolen.
The idea, I suppose, is that the sheer fact that a company has been hacked does damage to the company’s brand. Partners and customers may be concerned, it might be bad for business. Malicious hackers, therefore, try to leverage the threat of releasing details of a hack in order to extort hush money.
I don’t have a problem writing about companies that have been hacked. But I feel considerably less comfortable when I feel like I’m an accessory to blackmail.
TheDarkOverlord is one hacking group that has been engaged in this practice lately, attacking an investment bank.
And most recently they hacked Gorilla Glue.
So when TheDarkOverlord hacking group contacted me a few days ago, sharing private links to email archives they had stolen from Gorilla Glue, I had some thinking to do.
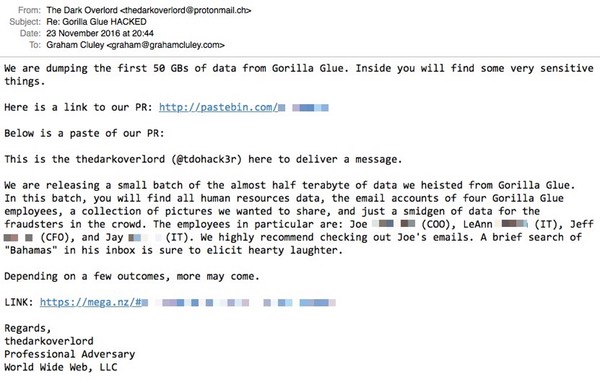
TheDarkOverlord wanted me to download the stolen data and write about the private conversations and business plans. But no, I wasn’t prepared to play ball.
There are, no doubt, other sites who will be all too happy to get some cheap clicks at the expense of a company that has suffered a criminal attack.
But this isn’t one of them.



Legally speaking Graham you can't be treated as an accessory in these circumstances, see s8 Accessories and Abettors Act 1861.
"Whosoever shall aid, abet, counsel, or procure the commission of any indictable offence, whether the same be at common law or by virtue of any Act passed or to be passed, shall be liable to be tried, indicted, and punished as a principal offender."
Each of those terms (aiding, abetting, counselling or procuring) have very specific meanings and the type of behaviour you refer to in your video is not a criminal offence on your part.
I agree with your moral stance not to publish but this doesn't make your behaviour criminal.
Thanks Bob.
As you've probably guessed (and I'm happy to clarify), my reluctance is not driven so much by the legality but the morality. :)
We shouldn't be helping online criminals blackmail their victims.
Sticky situation.
Hmmm… interesting screencap… I think protonmail doesn't want to be associated with Cybercrooks.
Theresa May doesn't mind reading all our private communications… so doesn't that make it all alright for the rest of us…
I guess I'm missing something here, Graham. What made these DarkOverlord losers even think you would be a conduit for the information plundered from Gorilla Glue? I would have thought your own well-known sense of ethics would eliminate you as a candidate for aiding and abetting such a crime.
Frankly, I'm surprised that you even published as much as you did. Even with the last names redacted, it is now possible to identify the four individuals named in the letter. Why not replace the names and departments entirely with "[name redacted]"?
As far as the legalities are concerned, by all means — it is wise to not become an accessory to a crime. But you are quite right; legality does not supersede moral principle, nor does it define moral standards. Refusal to aid thieves has always been a moral stance, regardless of whatever the political laws might say.
Cyber Criminals and blackmailers will contact anybody in the media (normally by means of a mass-mailing) with a view to receiving the desired publicity and thereby increasing their chances of success in extorting the money.
I am sure the DarkOverlord, whoever (s)he/they is/are, has NOT just contacted our Graham; multiple organisations will have been approached in respect of this.
It's already news elsewhere Nigel so Graham hasn't really published anything not easily discoverable through Google. Unlike other media outlets Graham hasn't published any of the spoils (the illicit source material).
The legal aspect is clear-cut in this case – even if Graham chose to publish the material there would be no criminal offence committed in English law.
Morally, he's done the right think IMO. He's published a story, which is newsworthy, and has included just the right amount of information to achieve his objective of producing a security blog post.