 Don’t freak out too much, but your favourite iOS or Android app might be putting your personal details and finances at risk.
Don’t freak out too much, but your favourite iOS or Android app might be putting your personal details and finances at risk.
Many of the headlines surrounding the recently-discovered HTTPS-busting FREAK attack has focused on web browsers, but the truth is that smartphone apps also need to do a better job of protecting your privacy.
New research from FireEye has revealed that thousands of the most popular Android and iOS apps are impacted, and could open the door for hackers to steal passwords and personal information.
According to FireEye, some iOS and Android apps have been fixed against the flaw, but many still remain vulnerable.
After scanning 10,985 popular Google Play Android apps with more than 1 million downloads each, we found 1228 (11.2%) of them are vulnerable to a FREAK attack because they use a vulnerable OpenSSL library to connect to vulnerable HTTPS servers. These 1228 apps have been downloaded over 6.3 billion times. Of these 1228 Android apps, 664 use Android’s bundled OpenSSL library and 564 have their own compiled OpenSSL library. All these OpenSSL versions are vulnerable to FREAK.
On the iOS side, 771 out of 14,079 (5.5%) popular iOS apps connect to vulnerable HTTPS servers. These apps are vulnerable to FREAK attacks on iOS versions lower than 8.2. Seven these 771 apps have their own vulnerable versions of OpenSSL and they remain vulnerable on iOS 8.2.
In short, even if you have updated your iPhone or iPad to iOS 8.2 (which includes Apple’s FREAK fix, amongst other important patches) or have visited freakattack.com to see if the browser you use on Android is vulnerable, you could still be putting your data at risk.
That’s because the flaw may not just reside in your operating system – the vulnerability may also be deep inside some of your apps that have embedded a vulnerable version of the OpenSSL library.
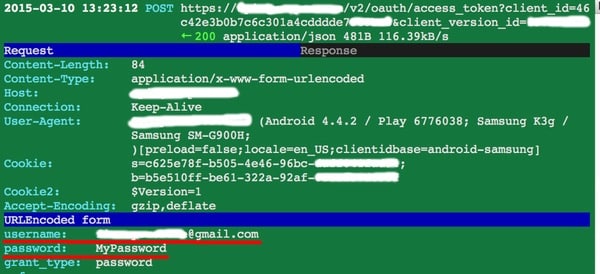
FireEye gave the example of the FREAK man-in-the-middle attack being used against a “popular shopping app”, successfully decrypting a user’s password and credit card information:

Further reading:
The researchers at FireEye have not identified which apps they believe are vulnerable to the FREAK attack, which leaves users in something of a quandary as to what to do.
Presumably it won’t take long before some of the higher profile vulnerable apps might become public knowledge, but in the meantime your best course of action may be to contact app developers and ask them if they have properly addressed the flaw.


