Researchers have reported an increase in activity for a Facebook-hijacking threat known as Faceliker.
Also known as “HTML/Rce.Gen,” “JS:Exploit.BlackHole.PR,” and “JS/FBJack.I!tr,” Faceliker has been in operation since at least 2013.
It’s a type of trojan that’s known for manipulating users’ Facebook accounts in an effort to generate artificial “likes” for specific content. McAfee Labs sheds additional light on the malware’s functionality:
“Faceliker infects users’ browsers when they visit malicious or compromised websites. It then hijacks their Facebook account clicks in such a way that users think they are liking one thing, but the malware is redirecting the click. It acts on their behalf to click another ‘like’ button without their knowledge or consent, essentially making each user an accomplice in the click fraud scheme.”
Such activity steams back to Faceliker’s handlers, who sell their “services” to content creators for the purpose of raising the profile of their product.
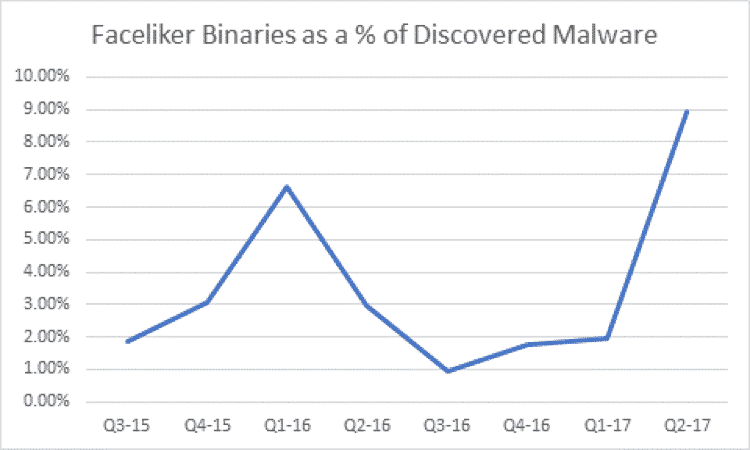
It appears there’s a growing number of less-than-ethical content producers out there today. Indeed, between the first and second quarters of 2017, McAfee detected a growth in Faceliker activity from two percent of the total number of malware binaries detected to 8.9%.
Faceliker’s growth is troubling enough. But given the opportunity to generate profit, McAfee Labs Vice President Vincent Weafer thinks the threat won’t be going away anytime soon:
“Faceliker leverages and manipulates the social media and app-based communications we increasingly use today. By making apps or news articles appear more popular, accepted, and legitimate among friends, unknown actors can covertly influence the way we perceive value and even truth.”
To protect against threats such as Faceliker, users should exercise caution around what sites they visit online and from what resources they download files that are hosted on the web. They should also make sure to protect their Facebook accounts and other social media profiles with two-step verification (2SV) as a means of deterring malware that’s capable of stealing their passwords.


