For the third time in a month, Google has gone public about a security vulnerability in Microsoft’s code – and not been prepared to wait for the software giant to publish a patch.
The security hole, which exists in Microsoft Windows 7 and 8.1 is expected to be patched in Microsoft’s regular monthly security update on Tuesday February 10th.
But that isn’t good enough for Google’s bug-hunting engineers, who not only went public about the flaw last week, but also published proof-of-concept code to demonstrate how to exploit the vulnerability.
The concern is that the details published by Google, and the proof-of-concept code released by Google’s bug hunters, is effectively a blueprint for online criminals to launch attacks against Windows users, and allow them to gain access to a user’s data in unencrypted form.
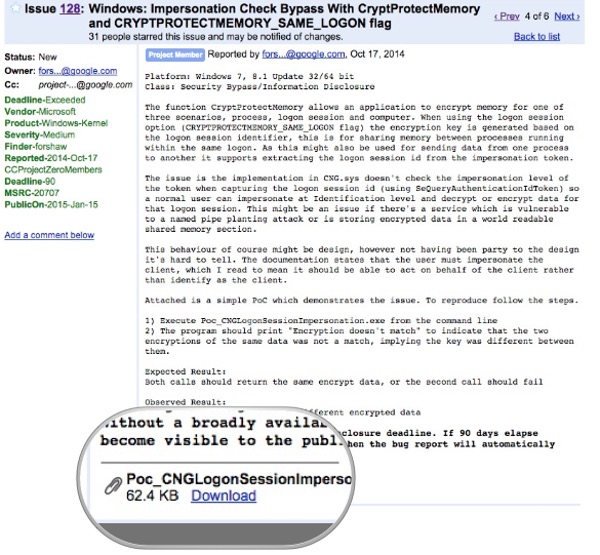
Google’s disclosure of the vulnerability – with working exploit code – is highly controversial. Google’s security engineers say that they privately informed Microsoft of the vulnerability in October last year, and started a 90-day countdown ticking before the eventually declassification.
Microsoft told Google that it had planned to roll out to customers a fix for issue in its January patches, but because of “compatibility issues” it got pushed back to February.
But Google couldn’t care less that Microsoft was attempting to ensure that its patch would actually *work*, and went public with details of the flaw anyway – with no patch still available.

So, for the third time in a month (the previous instances were both Windows Elevation of Privilege vulnerabilities) Microsoft users are left exposed to a security hole made public by arch-rival Google.
Of course, in an ideal world, Microsoft shouldn’t have had the security bugs in the first place. But I find it difficult to see how its response hasn’t been appropriate.
Microsoft clearly wants to fix bugs, but it wants to make sure that the fixes work.
Google, meanwhile, appears to have adopted behaviour which I would find more common in a schoolyard.
Isn’t it about time they grew up, and acted responsibly for the safety of internet users?
After all, it’s not as though their own Android backyard doesn’t have some dreadful unpatched security risks of its own.
This article originally appeared on the Optimal Security blog.