What’s happened?
It’s a bit complicated.
Okay, start from the beginning
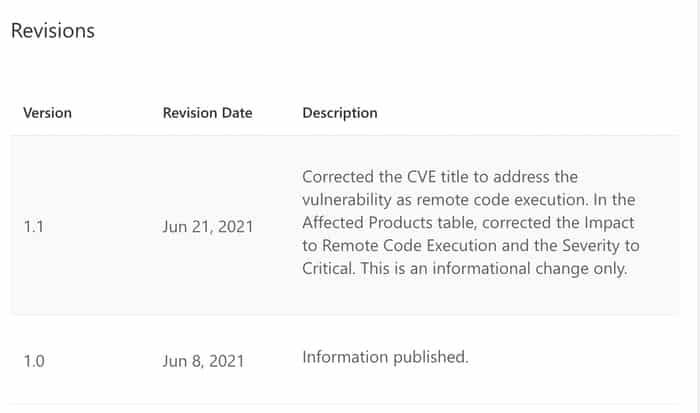
Back in June, as part of its regular Patch Tuesday process, Microsoft issued a patch (known as CVE-2021-1675) for what they classified as a “low severity” privilege-escalation vulnerability in Windows Print Spooler.
Some days later, on June 21, Microsoft reclassified the security hole as “critical”, describing it as a more serious “remote code execution” vulnerability.
Okay, but at least Microsoft had patched it, correct? So long as we’ve patched our Windows systems we’re alright…
Well, it then gets a bit more complicated.
You see, when some security researchers spotted that Microsoft had reclassified the vulnerability as “critical” it piqued their interest. And they released some proof-of-concept code that exploited a remote code execution security hole in Windows Print Spooler.
Why did they do that?
Presumably they thought Microsoft had fixed the vulnerability by issuing the patch. They were planning to present at the upcoming Black Hat conference all about their research into Windows Print Spooler bugs, and they thought – well, if Microsoft has already patched the bug then we might as well talk about it now and show off how clever we are…
Fair enough I guess, so long as people had patched their computers…
Ahh well. Here’s where the problem is.
You see, the bug that the researchers exploited in their proof-of-concept code was not actually the same security hole that Microsoft patched against last month.
So the researchers released a zero-day exploit for which no patch is available?
Correct.
Oh dear. But surely all they have to do is take down their code?
And to their credit, the researchers realised their mistake and have done exactly that.
We deleted the POC of PrintNightmare. To mitigate this vulnerability, please update Windows to the latest version, or disable the Spooler service. For more RCE and LPE in Spooler, stay tuned and wait our Blackhat talk. https://t.co/heHeiTCsbQ
— zhiniang peng (@edwardzpeng) June 29, 2021
But they didn’t act quite quickly enough. Pandora’s box was opened – and the code is now out in the wild.
And that’s why it’s probably right to call this PrintNightmare?
Yup.
So what should I do?
Make sure you are running the latest Windows security updates. They may not defend your systems against a PrintNightmare attack, but they’re still helpful.
In addition, some are suggesting that you disable the Print Spooler service on vulnerable PCs, and limit network access to servers where you feel you need to keep the Print Spooler running. If Print Spooler is running on any devices that don’t actually need it, disable it as that will help reduce the attack surface.
And wait for a security update from Microsoft.
Where can I read more about this?
- “Zero day for every supported Windows OS version in the wild — PrintNightmare” – Kevin Beaumont.
- “Leaked print spooler exploit lets Windows users remotely execute code as system on your domain controller” – The Register.
- “Critical Vulnerability: PrintNightmare Exposes Windows Servers to Remote Code Execution” – Huntress.



Does this affect Microsoft "Print to PDF'?
or "Print Extensions'?
or something called "Print Workflow 11_e67832'?