DetoxCrypto ransomware is raising suspicions that a new ransomware-as-a-service (RaaS) affiliate program might be in the works.
First detected by MalwareHunterTeam, the ransomware comes with a single executable that loads other executables and files. Those include Microsoft.exe, which performs the encryption process; a wallpaper background; an audio file; and another executable whose name varies based upon the variant.
Computer security expert Lawrence Abrams of Bleeping Computer explains, for instance, that the Calipso variant of DetoxCrypto comes with Calipso.exe. The executable locks the screen, plays the audio file, and displays a ransom message that asks the victim to email the attackers at for payment instructions.
That’s not all this variant can do, either. As Abrams observes:
“When this ransomware is executed, it will also take a screenshot of the active screen and upload it to the developer.
“It is possible that based on what is contained in the screenshot, the ransomware developer may try to increase the price of the ransom if the image contains blackmail worthy content.”
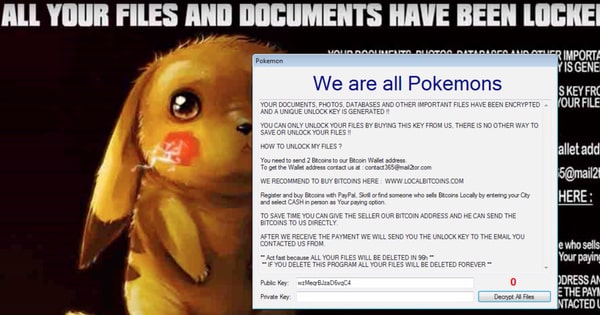
In the meantime, a second variant of DetoxCrypto takes a page from another recent ransomware discovery and adopts a Pokémon theme.
Its executable Pokemongo.exe is responsible for locking the screen, playing the audio file, and displaying the ransom message, which directs victims to contact for the attackers’ Bitcoin wallet.
These two variants of DetoxCrypto have Abrams thinking a new RaaS program might be in the works:
“This ransomware appears to be either part of an affiliate system or being sold on darkweb sites as we are seeing different variants, with different themes, email addresses, and features.”
Admittedly, it’s still hard to tell just what’s going on. MalwareHunterTeam told Softpedia the ransomware is still under development and has not launched a large distribution campaign yet. But it could very well do so soon, a move which might offer insight into its true intentions.
Users can protect themselves against both variants of DetoxCrypto by exercising caution around suspicious links and email attachments, keeping their systems up-to-date, maintaining secure backups, and installing an anti-virus solution onto their computers.


