The cybercrime gang behind the PYSA ransomware (it stands for “Protect Your System Amigo”, and is also known as Mespinoza) has released files which they claim to have stolen from the London borough council of Hackney during an attack some months ago.
As previously reported, Hackney Council acknowledged that it had been hit by a “serious cyber attack” in early October 2020, which left it unable to make housing benefit payments to the needy, and caused house purchases to fall through.
At the time of writing, months after the initial attack, Hackney Council continues to advise that it is unable to provide all of its normal services.
Hackney Council has been notably tight-lipped about the precise nature of the “serious cyber attack”.
Last October, I speculated that ransomware was at the heart of the attack, and sensitive data could have been exfiltrated by criminals:
“And if it is ransomware, is it one of the more unpleasant strains of ransomware attack where malicious hackers don’t just lock up your files and demand a ransom, but have also exfiltrated data from the network and are threatening to release it to the wider world if a sizeable ransom is not paid.”
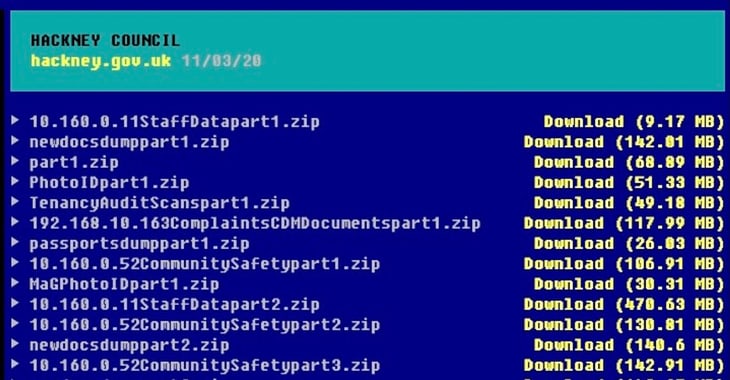
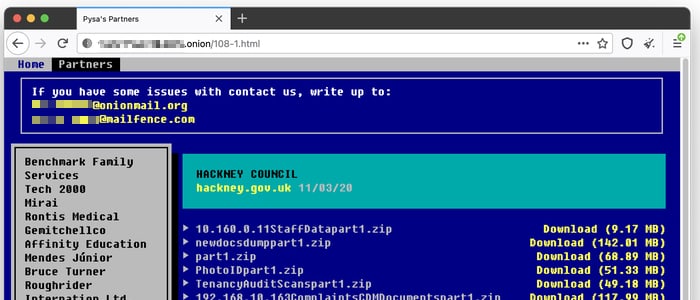
Well, what do you know… look what has been published on PYSA’s site on the dark web, where it lists its victims – gigabytes of data files purporting to have been exfiltrated from Hackney Council’s computer systems:
You can’t help but conclude that the PYSA ransomware gang has concluded that it’s not going to manage to crowbar any money out of Hackney Council, and so it might as well release the data it has stolen to the world.
Philip Glanville, the major of Hackney, released the following statement in response to the development:
It is utterly deplorable that organised criminals chose last year to deliberately attack Hackney, damaging services and stealing from our borough, our staff, and our residents in this way, and all while we were in the middle of responding to a global pandemic.
Now four months on, at the start of a new year and as we are all responding to the second wave, they have decided to compound that attack and now release stolen data. Working with our partners we will do everything we can to help bring them to justice.
I fully understand and share the concern of residents and staff about any risk to their personal data, and we are working as quickly as possible with our partners to assess the data and take action, including informing people who are affected.
While we believe this publication will not directly affect the vast majority of Hackney’s residents and businesses, that can feel like cold comfort, and we are sorry for the worry and upset this will cause them.
We are already working closely with the police and other partners to assess any immediate actions we need to take, and will share further information about the additional action we will be taking as soon as we can.
Past victims of the PYSA/Mespinoza ransomware include Australian money management firm MyBudget and kitchen product manufacturer Teka Group.



Would it be true to state that Cybersecurity at Hackney council has been increased although one could wonder why it hadn't been seen to before.