Computer security veteran Philip Le Riche shares his thoughts on the possibility of cyberwarfare.
 There has been much hype in the media in recent months regarding cyberwarfare, indeed ever since the purpose of the Stuxnet worm became apparent.
There has been much hype in the media in recent months regarding cyberwarfare, indeed ever since the purpose of the Stuxnet worm became apparent.
This is not least because journalists have realised that scandalous data breaches and anything with the “cyber-” prefix makes good copy.
But it has also been suggested that the hype is generated by security consultancies for their own ends.
Yet national security agencies such as the NSA in the US and GCHQ here in the UK are sufficiently concerned by the level of hostile state sponsored activity to spend large sums on countermeasures.
The Mandiant report brought the scale of the threat into the open, but these agencies had almost certainly come to the same conclusions and more, many months if not years ago.
So how worried should we be?
Prophets of doom have pointed to glaring vulnerabilities in SCADA industrial control systems used to manage major plant and critical national infrastructure including power and utilities, transport, distribution, and chemical, industrial and nuclear facilities.
What is more, many such systems appear to be inadvisedly connected to the internet, sometimes with poor security, in order to let the operators have a weekend off or go on holiday once in a while and still be on call to deal with an emergency.
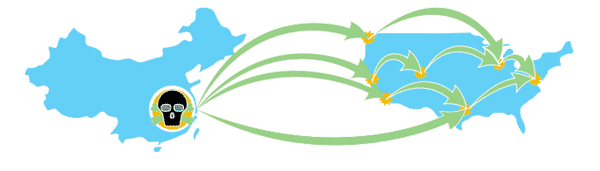
It would seem that if a threat actor wanted to poke around with his cyber-chopsticks (let’s not be political – not very, anyway) and switch off the lights in London, he probably could.
Whilst this is doubtless true or not far off and is certainly a real potential threat, for my part, I don’t believe it’s more.
But no one can be sure, so of course there will be heavy investment in both defensive and doubtless offensive capability because the impact of getting it wrong could be very high.
The same syndrome was apparent during the Cold War when the military invested in parapsychology, not (I presume) because they seriously believed in its potential, but had it turned out to be real and the other side had mastered it first, it could easily have been a game-changer.
Besides, worms and viruses have a habit of escaping into the wild before their creator intended, in other words, a cyber-weapon may effectively press its own launch button.
And so there will certainly be accidents. The far from surgical levels of cyber-hygiene that allowed Mandiant to build up a comprehensive picture of the so-called APT1 group is yet more evidence.
But the threat of a major cyber-war is something else, which for my part, I don’t believe is real. For the present, at least.
And the reason is simple: all the major national economies are so tightly interconnected that you can’t hurt your adversary without hurting yourself.
Thomas L. Friedman, prize-winning journalist with The New York Times, famously postulated that there’s never been a war between two nations both having a McDonalds in their capitals.
Whilst probably not quite true, it illustrates the point.
 China needs to continue to sell us all those iThingys and digital what-nots they manufacture just as much as we’re addicted to buying them, and so it’s foolish to suggest that they might turn the lights out in London.
China needs to continue to sell us all those iThingys and digital what-nots they manufacture just as much as we’re addicted to buying them, and so it’s foolish to suggest that they might turn the lights out in London.
To do so would hurt their own interests as well as ours, quite apart from the complete uncertainty as to what reaction it might solicit.
But what about a lesser objective?
Suppose we were to offend them and they wanted to fire a warning shot? How about turning the lights off in London for just an hour or so?
The trouble is, whereas turning the lights off might be relatively easy, turning them back on again would require a huge amount of coordination between many different control centres in order to do so without repeatedly crashing the national grid.
It’s like smashing an egg: easy, but you can never put it back together again. As with chemical and biological weapons, once a cyber-attack is launched, it’s out of control. It’s fire and forget – forget about any chance of de-escalation.
In the longer term though, I’m somewhat less relaxed.
Rogue states such as North Korea and Iran are not tightly bound into the world economy and have little to lose, particularly given that undeniable attribution is so hard.
 Already, we have seen 30,000 PCs rendered unbootable in an attack in 2012 on Aramco in Saudi Arabia, possibly by an Iranian backed anti-American group.
Already, we have seen 30,000 PCs rendered unbootable in an attack in 2012 on Aramco in Saudi Arabia, possibly by an Iranian backed anti-American group.
Serious though this was for Aramco, in global terms it was a pinprick, and my guess is that for the present the capability of such groups is more than matched by Western national security agencies.
But building up a cutting edge cyber-offensive capability has got to be much cheaper and less time consuming than developing a nuclear capability and delivery system.
An attack on the whole internet, perhaps leveraging weaknesses in the underlying routing protocols such as BGP, or using the huge numbers of potentially vulnerable devices such as ADSL routers or webcams (and next year, doubtless Windows XP systems!), could perhaps have an effect comparable to the banking crisis of 2008.
As with rebooting the national grid, rebuilding the internet whilst large numbers of compromised devices remained active could be tricky.
Business continuity is now a routine activity in any enterprise following best practice, but whilst fire, flood, bombs and pandemic frequently appear on the agenda, I suspect that loss of a substantial part of the internet generally goes in the “too hard” tray if it’s considered at all.
Less relaxed in the longer term? So what do I mean by the longer term? I was afraid you were going to ask that!
What’s your opinion? Do you agree with Philip Le Riche? Leave a comment below to let us know what you think.



In response to Philip's statement "Already, we have seen 30,000 PCs rendered unbootable in an attack in 2012 on Aramco in Saudi Arabia, possibly by an Iranian backed anti-American group.
Serious though this was for Aramco, in global terms it was a pinprick, and my guess is that for the present the capability of such groups is more than matched by Western national security agencies."
Philip, there's no way that any Western intelligence agency could stop a malicious insider from plugging a USB stick into a server at a multi-national company and load a wiper virus directly into the network. That's what happened at Saudi Armaco at one of their EU offices.
Of course you're right, Jeffrey. I wasn't suggesting that Western intelligence agencies could have thwarted that particular attack (or a similar one), but simply comparing the levels of sophistication of the two sides. That said, there are simple technical solutions for USB port blocking, though defending against spear-phishing is challenging.