 I guess you could consider it a badge of honour.
I guess you could consider it a badge of honour.
I mean, you know you’ve really made it as an anti-virus company when intelligence agencies like the NSA and the United Kingdom’s GCHQ are looking for vulnerabilities in your software, and interested in spying on the emails that your customers send you about new malware.
And that, it appears, is what has been happening.
The latest article in The Intercept reveals documents leaked by NSA whistleblower Edward Snowden, which appear to indicate that the intelligence agencies are interested in spying on a host of anti-virus and security firms, with the intention of learning how to avoid their own attacks being detected by the software.
Take, for example, this part of a warrant renewal request from GCHQ to the British Foreign Secretary, dated June 2008.

“Personal security products such as the Russian anti-virus software Kaspersky continue to pose a challenge to GCHQ’s CNE [Computer Network Exploitation] capability and SRE [software reverse-engineering] is essential in order to be able to exploit such software and to prevent detection of our activities.”
In a nutshell, the likes of GCHQ and the NSA want to write malware that will get past the defences of the anti-virus software. And ideally they would like the green light of legal immunity in order to proceed.
A slide from an NSA “Project CAMBERDADA” presentation lists over 20 anti-virus and security firms that the spies considered targets.

Amongst those vendors listed are Bitdefender, ESET, Avast, AVG, and F-Secure. Notably US-based vendors McAfee and Symantec and Britain’s own Sophos are nowhere to be seen.
Which, if you think about it, is a little odd from the security point of view.
 After all, the security products of Sophos, Symantec and McAfee are sold all around the world, and chances are that there are systems protected by these products that the likes of the NSA and GCHQ would like to subvert and spy upon.
After all, the security products of Sophos, Symantec and McAfee are sold all around the world, and chances are that there are systems protected by these products that the likes of the NSA and GCHQ would like to subvert and spy upon.
It would be easy to assume that those products didn’t make the slide because they are are based in the United States and United Kingdom.
Trend Micro is also notably missing – which causes me to raise a wry smile as that particular firm can never seem to decide whether it’s Taiwanese, Japanese or American. Perhaps the NSA aren’t sure, either?
The lack of Chinese anti-virus vendors listed also raises some question marks about the NSA’s ambition in an area that one would consider important to them.
But pity those other security vendors who weren’t considered important enough to even make the NSA’s list of future targets.
How must they be feeling at this moment to have not made the grade? Yes, there are probably some security vendor CEOs demanding that his techies confirm that their systems haven’t been compromised right now, but there must also be some giving their marketing team a hard time for not making the NSA’s radar.
Of course, if attackers (whether intelligence agencies or common cybercriminals) were able to find vulnerabilities in anti-virus software then that could be immensely valuable to them. Anti-virus software typically runs with high privileges on computers, making them an attractive platform for exploitation.
In the same report, The Intercept reveals that the NSA were able to gather information about Kaspersky customers by monitoring communications between the anti-virus product and the company’s servers. In addition, the “Project CAMBERDADA” presentation, includes examples of intercepted emails sent to anti-virus companies about new malware samples found at customer sites.
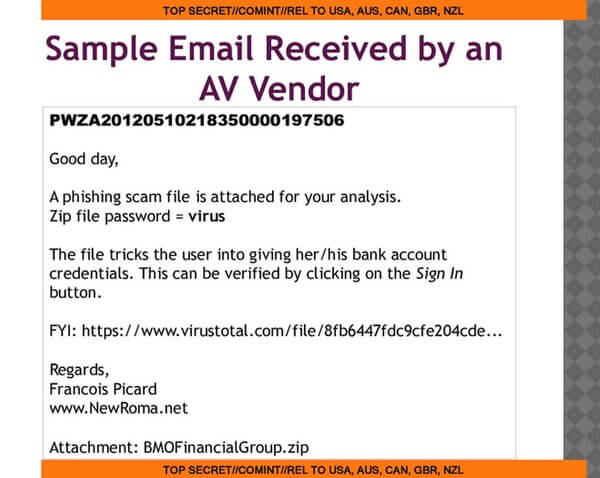
François Picard, the person who sent that particular email, says that he regularly notifies anti-virus vendors of new malware – and that he never sends such notifications to government agencies.
“It is strange the NSA would show an email like mine in a presentation,” he told The Intercept.
Well, it certainly is a strange world we live in.
In the last few months, for instance, we have seen Kaspersky go public with details of sophisticated malware it found on its own network and its founder Eugene Kaspersky hit by a hatchet job in the US media claiming he hangs out at the sauna with Russian spies.



Chances are pretty good that NSA/GCHQ/etc. are able to track Eset customers as well, Eset Nod32 sends a unique username and password in the clear every time it checks for updates.
Eset's response when I brought this up: We're working on changing this in a future version, but don't worry it's "not a personal identifiable item."
Do you have a link for this, Jeff?
https://imgur.com/a/X4vPF
Thanks.
"It would be easy to assume that those products [Sophos, …] didn't make the slide because they are are based in the United States and United Kingdom."
From which I draw the inference that, for example, Sophos didn't make the slide because it already cooperates with GCHQ in making its software compliant with GCHQ's requirements. Is that what you meant? Or is it that you couldn’t possibly comment?
I'm not aware of any requirements made to Sophos by GCHQ during my time working there.
From personal experience, McAfee and Norton are terrible AV products, both at detecting malicious things and their usage of system resources. Perhaps GCHQ and NSA didn't include them on their list because they're so poorly written they didn't feel the need.
Agree on the first part (well, part 1.1 and 1.2 as both are equally valid, especially resource utilisation and more so in relation to the quality of the detection system). But the second part might be that they have no problem getting beyond them in the first place. Of course, it could also be what you would expect of espionage – the list could be fabricated (in general misdirection/misleading/etc.). One never knows with the two organisations though and as such who knows the reasons for the products they list (and/or how legit their statements aren't).
That does seem to be the obvious answer – that those omitted from the list of "more targets", the big boys, have already been targeted for a while and, presumably, already sufficiently cracked for GCHQ's needs.
I would rule out the idea of them cooperating – for a security firm to ignore something it can see is doing naughty stuff would be too much of a risk, in case it fell into the wrong hands (as software invariably does).
Indeed true. I wasn't even thinking of cooperating with the government but I will say it isn't as easy as that; yes it would be a risk to them. Unfortunately, depending on bullying (something 'leaders' are great at) and loopholes in laws (something that every law has in some form) or even laws designed to force bad things upon others (something lawyers also enjoy) some corporations have no choice. This goes for telephone companies as well as others. Of course, some like Google and Facebook both call out the issues but with those two there is a certain amount of hypocrisy.
So yes, either they already compromised these vendors or they're attempting to deceive (something that they obviously do try and something they succeed with many people). But I wouldn't rule out companies cooperating, either; they might resent it but that doesn't mean they have a choice.
The lack of Chinese vendors may simply be because they "borrow" other scan engines and just re-skin it.
Definitely a badge of honour for Kaspersky. Their Internet Security Suite is always rated the best by independent comparative assessors and they have successively won the annual award of 'Best Internet Security' by ComputerActive magazine. It's easy to configure but gives you plenty of 'under the hood' options to play with – including the option to ONLY run whitelisted programs.
So it seems that the advice would be: trust your Internet Security to the Russians (Kaspersky), trust your encryption to open source developers (DiskCryptor, VeraCrypt, AxCrypt etc.) and trust your Operating System to the Americans (Microsoft).
Unless there's a hell of a lot of co-operation between the above actors it'll make hacking attempts substantially more difficult as I'd bet my bottom dollar that Kaspersky, Open Source and Microsoft won't play nicely with each other.
You can't be actually serious. Trust your OS to Microsoft? The company that was revealed (and denied) adding back doors into it's product for the NSA? The company that intentionally crippled it's disk encryption (which may be fixed now)? The company that's known to have given access to the gov't of it's online email and other cloud services? Wow, I just can't…
Kirbini, for most users Windows is the operating system of choice. Ultimately you've got to trust somebody.
The majority of users are flummoxed when their icons are moved about the desktop or their Wi-Fi signal drops. We can't expect them to use other operating systems like Linux. And even if we could, their founder: Linus Torvalds, has himself said that he's not surprised users prefer Windows.
Linux is simply too difficult for your average users and I've met plenty of people who use it but do so insecurely because they've compiled the kernel incorrectly, not set-up firewall rules correctly, they don't have a deep enough knowledge of cryptography to use LUKS securely etc.
Even though Linux is open source their are plenty of bugs that aren't fixed, many annoyances and even gaping security problems that aren't getting repaired because the developers are busy messing around with their own forks. Look at the OpenSSL vulnerabilities – they remained around for years whilst they were (presumably) being ruthlessly exploited. There aren't enough developers who have the skills, time, tools, motivation or inclination to examine each and every distro and the umpteenth changes that accompany each release. This makes it less secure than Windows which is regularly maintained, used by industry and has a massive user base.
Taking this in mind what do you suggest?
Only to respond to certain portions of your post:
'Ultimately you've got to trust somebody.'
Trust is the wrong word. But I get your point; you have to use something if you want to use a computer. For most it is Windows because it is so easy to use (or in theory it is – many would probably disagree and while they might not understand why, one important fact is when Windows is dumbed down more [hard to believe maybe, but still happens] and more, the less users have to think which means things can become more difficult for them over time). In the end you can complain about OS 1 or OS 2 but to state one vendor is X when it is the only vendor with software you can use, you're being rather silly (if you want to use a computer, that is!).
'Look at the OpenSSL vulnerabilities – they remained around for years whilst they were (presumably) being ruthlessly exploited.'
It isn't Linux specific. But that being said, yes, too many are ignorant of Linux (generally) and Linux has an easier learning curve than some of the other Unices. I'll refrain from remarking further on that point because I know I would personally name some examples and that is going too far (and serves no good).
'to use LUKS securely etc.'
Just going to remind you what corporation is part of LUKS… subtly, that is.
'Even though Linux is open source their are plenty of bugs that aren't fixed, many annoyances'
True for all software except that more people with the source means more can keep track of tampering (git does a great job here although there will obviously still be bugs). Indeed there are a lot of problems (and more and more will happen because bugs are a frequent part of programming and I know this from personal experience), and in recent years some things have changed, things that defy what was (and is) known to be common wisdom in its design… all because certain corporations that think they know best for everyone and are relentless with this (see below). Won't name any examples for same reason as above (Linus himself has gone about some of these changes, as have I, but unfortunately the corporations in question don't actually care what others think).
'Taking this in mind what do you suggest?'
I used to be relentless with this and it is something that I slowly realised was flawed at the core. Flawed and arrogant of me. I have since then said to everyone, and this is how it should be (and is what you're trying to say, I think): you should use what works for you; trying to use something that doesn't work for you, when there are alternatives that DO work for you, is nonproductive and rather silly.
And that is the bottom line: everyone should use what works for them and stop bickering at each other. Bickering with/insulting/attacking others over what is best is stupid. Best is subjective and fighting over it won't change views for the good.
Microsoft has had its issues in the past with security, but I think it is fairly easy to say that as of Windows 8.1 and certainly the upcoming Windows 10, Microsoft has far surpassed any OS on the market in terms of security. Code flow guard, Patch Guard, DEP, Protected Processes, ASLR, Device Guard, Trusted Boot, etc. etc. I think its obvious that Microsoft has made security a priority as of late. I cannot think of what I would trust more.
As to Kaspersky, it phones home a lot, and having former KGB cyber folks making my anti-virus does not give me a warm fuzzy. I think Kaspersky is unarguably one of, if not *the*, best AV products on the market, but not in my domain thank you.
It's worth pointing out that Kaspersky is used by the UK and US governments.
You talk about it 'phoning home' but I've never noticed this. All it does is routinely check for updates and, if you've got 'Cloud Protection' activated, it will check software for zero-day threats.
I've looked at outbound router logs (which the software cannot modify) and I can't see anything untoward. What am I missing?