
Upgrades made to CryptXXX ransomware over the past couple of weeks have rendered a previously available decryption tool useless.
First detected by Proofpoint’s security researchers back in mid-April, CryptXXX is one of the newest ransomware variants to prey upon unsuspecting users.
The crypto-malware is currently being shipped as a Dynamic-Link Library (DLL) that is dropped by Bedep malware and the Angler exploit kit.
Once the infection cycle is complete, CryptXXX encrypts a number of different file types and appends the .CRYPT extension to each encrypted file. It then displays a ransom message that demands US $500 and warns the ransom fee will double in value if payment has not been received within a few days.
The ransomware has been observed in a number of attack campaigns since its initial discovery. Those include a malvertising infection affecting two TV stations, and an exploit kit attack campaign involving a popular toy maker’s website.

CryptXXX wasn’t perfect.
In just a few weeks, researchers at Kaspersky Lab had successfully discovered a bug in the ransomware’s encryption process, which they were able to exploit in their RannohDecryptor utility, allowing CryptXXX victims to decrypt their files for free.
For a time, it seemed that CryptXXX was dead in water.
But that was celebration was clearly premature.
According to researchers at Proofpoint, the ransomware is alive and well… and it’s being updated:
“CryptXXX is being actively maintained: we have seen it evolve multiple times since our initial discovery, but the changes did not appear significant enough to be mentioned. As expected, the number of actors spreading it has increased, making it one of the most commonly seen ransomware families. Globally, we have observed several primary threat actors transitioning from Teslacrypt/Locky to CryptXXX/Cerber in the driveby landscape in recent weeks. CryptXXX is most frequently dropped by Bedep after Angler infection, but we have seen it dropped directly by Angler as well.”
Now CryptXXX version 2.006 is circulating in the wild, and it’s sporting a number of upgrades.
The first is the use of a lock screen to make the infected computer unusable:
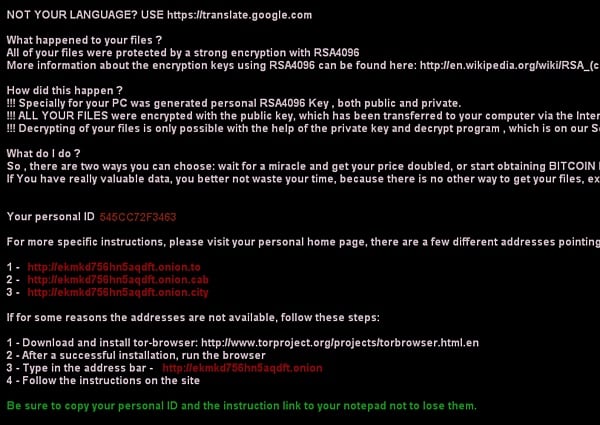
As a result, victims of this newest iteration of the crypto-malware must now use another computer to purchase Bitcoins and ultimately submit their ransom payment.
Infuriating, to be sure, but it pales in comparison to the second upgrade discovered by Proofpoint:
“We first thought that the new lock screen was a quick and dirty way to make it more difficult for the victim to use the Kaspersky decryption tool. But upon further inspection, we found that the authors discovered a way to bypass the latest version of the decryption tool.”
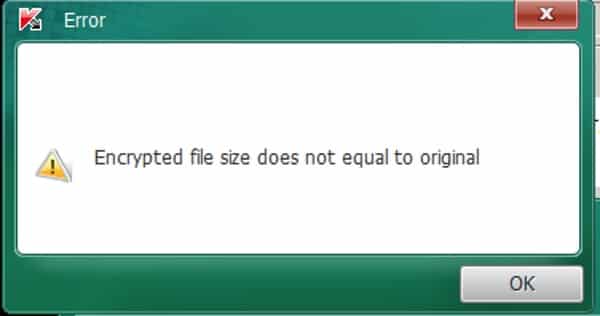
With no way for victims to unlock their files for free, CryptXXX has reclaimed its status as an undecryptable form of ransomware.
Users should therefore implement software and security patches as soon as they become available, maintain a regularly updated anti-malware solution on their machines, back up all critical data securely, and avoid clicking on suspicious links/email attachments.
In the meantime, researchers will without a doubt explore the possibilities for another decryption tool.



There's something I can't grapple with Crypto Locker and it's derivatives.
The malicious author publishes resources for the victim to access and make payments too.
Why can't these been used as avenues to track and shutdown the operations of these crooks?
In any case, it drives the point about being vigilant and that mitigations and contingencies are crucial, no matter who you are and what you administer/use.
Does this make backups useless?
No I thought not.
Restore from backup is still the most sensible option. Renders other solutions obsolete on many counts, least of all restoring to a known good point where the malware wasn't present. Unless we're talking firmware infections, then use the universal smartphone tool(http://www.northerntool.com/images/product/400×400/257/2570708_400x400.jpg) to sanitise the hardware.
For "tracking payments" it depends on the payment systems. In the case of the 'tard that took amazon gift voucher this is easy to track, for things like bitcoin, less so. Although there are flaws in bitcoin that allow it to be transaction tracable thorugh the entire history of the coin, it'd take some epic stupidity like cashing it up via an exchange setup with an account in your name. Then you have to consider the global nature. A system in Canada infected with ransomware by a Nigerian actor is unlikely to meet with viable recompense. The Nigerian authorities are unlikely to put much effort into finding them, unless they achieve a significant scale. They have bigger problems to worry about on a day→day basis.
What I have difficulty in grappling with the ransomware concept is:
A) How people manage to get themselves infected
B) Why they would entertain paying.
If this is data you value, there's backups. If you don't back it up, you don't value it, point blank. Therefore there's no excuse to pay out in any situation. No backups? you didn't want to keep it anyway, isn't worth paying for. Else restore from backup. How it's possibly a viable commercial operation astounds me.
In the cases like "professional" institutions that have become infected , say law enforcement and medical services, I have great difficulty in believing these do not have backups.
Then there's the infection vector. When it's some sherrif in tennessee having themselves a crafty thomas tank whilst on night shift, it's pretty funny when the pr0n site he'd clicked on was laden with malware – but if this system is supposed to be used for law enforcement, then it's a *known* unsuitable use for the system. Irresponsible – criminally so – on the officers part. If that stored "evidence" then it's no rights being interwebs accessible. Just makes it easier to edit. In the case of hostpitals then there's real concern about how this gets in there. Medical records shouldn't be stored on systems publically accessible to interwebs. Makes them easier to steal. If they systems are sensibly isolated, then someone's been doing something they shouldn't – and this is kinda why they shouldn't. In the case of home users, as I seem to regularly repeat: Why was the browser allowed to execute that code? executing random third party code as default is insanity. There's also a valuable lesson in trust applicable with regards to the websites mentioned above. Specifically you should be questioning how much trust you should place in these companies. If that's there intetnionally or if they can't even be bothered to keep their servers secured – either IMHO is enough excuse for them to lose access to the server. They can't be trusted, proven. Certainly enough to lose your custom.
Further, just because it was safe last time you used it doesn't mean it's safe now. Things change. Even if the site is known good, those with nefarious intent can insert it. For example the way the GCHQ(The real one, not the newsletter) trivially and en-mass inject calls to malware and various scripts into the body of mobile browsing traffic on the fly. (at least they can only do that to HTTPS traffic they hold the master CA for. Use HTTPS wherever possible and keep an eye out for things from 1.2.3.0/24)