
A malvertising attack campaign is targeting visitors to two TV stations affiliated with the American CBS TV network.
Jérôme Segura, a senior security researcher for Malwarebytes, explains in a blog post that the attack campaign is affecting KMOV, a TV station in St. Louis, and WBTV, another CBS-affiliated broadcast station based in Charlotte, North Carolina:
“This malvertising attack leveraged a familiar technique of hijacking GoDaddy accounts to create various subdomains pointing to malicious servers. These are used to host the ad content (JavaScript, image, etc.) but also to hide malicious code and alternate between clean and infected adverts depending on multiple factors (time of day, user agent, IP blacklist, etc).”
The rogue advertiser subverted the self-service Taggify advertising platform, after hijacking poorly-protected GoDaddy accounts to create subdomains hosting malicious code. The result? Malicious ad banners were displayed to those who visited the websites belonging to the two CBS-affiliated stations.
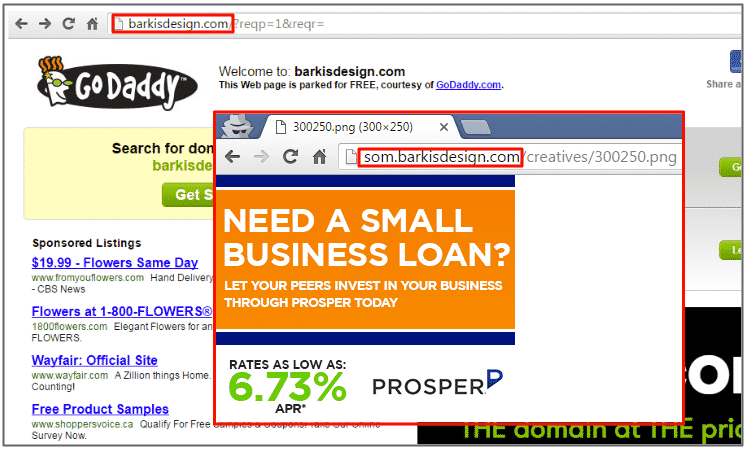
The advertiser shows a “normal” ad banner to web scanners and crawlers, making the attack more difficult to detect.
When legitimate users visit the TV stations, however, they are served up an iframe that redirects them to the Angler exploit kit.

The Angler exploit kit needs no introduction to regular readers. It has been involved in countless malvertising campaigns, including those leveraging fake social button plugins, browser extensions, and even Skype.
Angler has been used in the past to drop a number of malicious programs onto a victim’s computer, including Bedep and the CryptXXX ransomware.

Users can protect themselves against malvertising such as that used in this particular campaign by implementing software patches and security updates as soon as possible.
It’s important to note, however, that site owners also have a part to play in the fight against malvertising.
As Segura recently told TeckWeekEurope, these individuals’ role partially boils down to strong password security:
“GoDaddy is one of the world’s largest registrars and, as such, it will experience many attacks against its platform across the globe. However, the weakness comes from website owners who have chosen poor passwords or have had their machines compromised. Trojans will harvest passwords stored in FTP clients or other software used to administer a site. Without the owner’s knowledge, attackers now possess the credentials to alter a site’s settings allowing them to make DNS changes, add subdomains, and so on.”
If you are a website owner, don’t contribute to the scourge of malvertising. Choose a strong, unique password to help protect your site from hijacking attacks, and ensure that you have a layered defense in place.



Another reason to run an ad blocker and a javascript blocker.