Apple has quietly pushed out a security update to iOS, the operating system used by its flagship iPhone and iPad products.
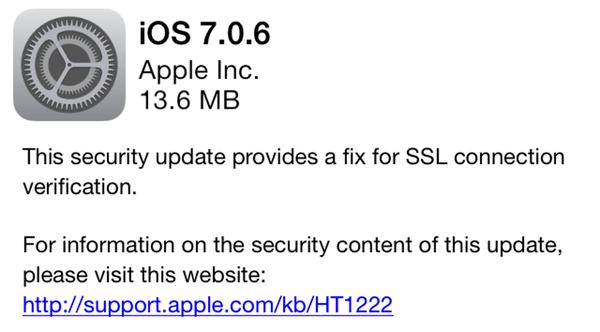
This security update provides a fix for SSL connection verification.
To the average person in the street that reads like gobbledygook. Apple might as well have said “This security update provides arfle barfle gloop chihuahua hatstand”.
But it’s actually really important that you update your iPhones and iPads as quickly as possible.
 Because what Apple says it has fixed is actually a critical vulnerability that could allow hackers to intercept what should have been secure communications between your iPhone and SSL-protected websites. That means, potentially, online attackers could grab your userid or passwords as you attempted to log into popular websites.
Because what Apple says it has fixed is actually a critical vulnerability that could allow hackers to intercept what should have been secure communications between your iPhone and SSL-protected websites. That means, potentially, online attackers could grab your userid or passwords as you attempted to log into popular websites.
Security researchers at CrowdStrike have published a blog post where they not only describe how the attack can be exploited by hackers, but also warn that the flaw also exists in Mac OS X:
To pull off the attack an adversary has to be able to Man-in-The-Middle (MitM) network connections, which can be done if they are present on the same wired or wireless network as the victim. Due to a flaw in authentication logic on iOS and OS X platforms, an attacker can bypass SSL/TLS verification routines upon the initial connection handshake. This enables an adversary to masquerade as coming from a trusted remote endpoint, such as your favorite webmail provider and perform full interception of encrypted traffic between you and the destination server, as well as give them a capability to modify the data in flight (such as deliver exploits to take control of your system).
It’s easy to imagine attackers exploiting the vulnerability to intercept victim’s web sessions as they connect with their webmail, or indeed any other SSL-protected site.
For the curious, Google engineer Adam Langley has described how the bug occurred in some detail on his blog.
Here is the offending section of Apple’s source code:

Did you spot the two “goto fail” lines in the code? One immediately after the other?
The first one is in the right place, but the second definitely shouldn’t be there. That duplicate line of code messes up the code’s execution, meaning that a critical authentication check doesn’t occur.
A computer programmer’s fumble at the keyboard has put the privacy of millions of iPhone and iPad users at risk. Whoever made that mistake must be feeling pretty bad right now.
 Fortunately, Apple has now spotted the problem and fixed it (all you need to do is install the update on your iPhone or iPad by visiting Settings / General / Software Update).
Fortunately, Apple has now spotted the problem and fixed it (all you need to do is install the update on your iPhone or iPad by visiting Settings / General / Software Update).
Owners of older iDevices should update to iOS 6.1.6, and there has also reportedly been a software update pushed out for Apple TV too.
But iOS’s cousin, Mac OS X, is also vulnerable to the same shocking privacy flaw. And there is no fix for those affected desktop and laptop computers yet.
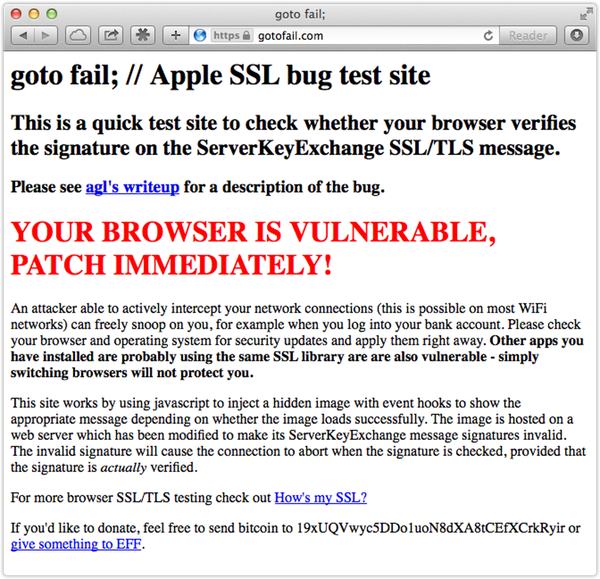
Websites like gotofail.com have already sprung up, making it easy for users to test whether their computers and devices are at risk, and whether online criminals could theoretically be spying upon them.
Here’s what happened when I visited gotofail.com on a computer running Apple’s Safari browser on Mac OS X Mavericks:
Let’s hope that Apple pushes out a fix soon for Mac OS X users, and that their testing will be more extensive in future to avoid such serious bugs shipping in future.



Strange… I don't get the "YOUR BROWSER IS VULNERABLE" message when I visit https://gotofail.org with Safari 5.1.10 on Mac OS X v10.6.8 Snow Leopard (which is supposedly vulnerable). Anyone else able to replicate this?
My mistake. In OS X, it seems this bug was introduced in Mavericks 10.9.0 (released October 2013).
Meanwhile, the first affected iOS version was 6.0 (released September 2012).
Mountain Lion 10.8 (released July 2012) was initially released prior to when the flawed code was added to iOS 6.0, and so based on what I've read, it apparently skipped ever being introduced into Mountain Lion.
So if you're running Snow Leopard 10.6.8, Lion 10.7.5, or Mountain Lion 10.8.5, you shouldn't be affected by this particular bug… but you're also missing out on critical security fixes in 10.9.0 and 10.9.1 that still haven't made their way into older versions of Mac OS X — see https://support.apple.com/kb/HT1222
It seems fine for Chrome. I do not use Safari anyways,
Kent, it seems you may have missed the point. This affects the entire operating system and most apps that run within it. The only reason Chrome "seems fine" is that the OS X version of Chrome does its own SSL validation, independent of the operating system.
See also this tweet which Graham retweeted a few hours ago:
—
Gavin Millard @gmillard
Looks like the OS X software update application relies on the flawed SSL library we are eagerly awaiting the patch for. #Securitycatch22
7:43am Pacific · 24 Feb 2014
https://twitter.com/gmillard/status/437976168474873856
—
The update packages themselves are signed, but still… it gives one pause to realize how much can be affected by one simple duplicated line of code.