Updated With concern about the Covid-19 Coronavirus reaching fever pitch in many countries, many people may be keen to find information online about whether there is an outbreak in their country, and how it compares to the rest of the world.
Well, be careful about which websites you trust.
Not only because there may well be misinformation out there, but also because there might also be malware.
Security researchers at Malwarebytes say that they have found malicious code hiding behind a website that claimed to show an up-to-date global heatmap of Coronavirus reports.
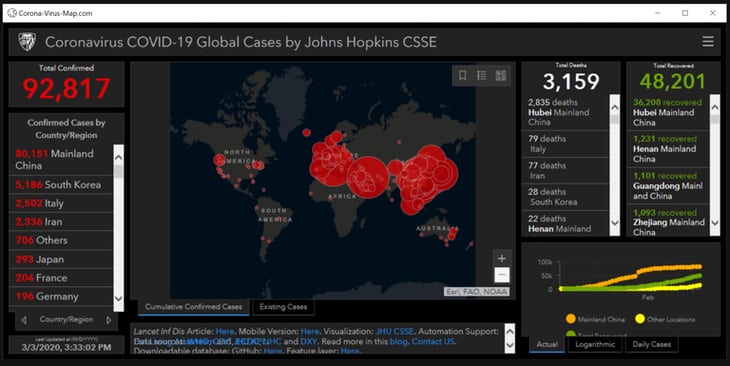
Malwarebytes is identifying the malicious code, which skims for passwords and payment card details, as a variant of the AzorUlt spyware. The malicious site appears to have copied the look-and-feel of a legitimate Coronavirus map from Johns Hopkins University.
So far the researchers have not seen any indication that the website containing the malicious code has been promoted through an email campaign, suggesting that perhaps those behind it were hoping users would stumble upon it while scouring the web for information.
The World Health Organisation (WHO) is publishing information on its website about the Covid-19 Coronavirus outbreak.
Update 10 March 2019: Researchers at PC Risk have shared some more details about the threat which expand upon the original Malwarebytes blog:
Contrary to its name, Corona-Virus-Map.com is not an address of a website, it is the name of a malicious program. It is classified as a trojan, or more specifically a “backdoor” trojan. This type of malware is designed to cause chain infections, in other words – to stealthily download/install additional malicious programs. Corona-Virus-Map.com is presented as a piece of software allowing users to view the progress/spread of the Corona virus epidemic in real time. Instead, this trojan proliferates the AZORult malware.
Be careful what programs you install and run on your computers folks… or you might be putting yourself at risk of a nasty infection.


Incomplete. Are you saying this is not a website from Johns Hopkins or that Johns Hopkins is distributing malware intentionally. Many articles are promoting this site as a legit COVID dashboard.
From the look of the screenshot, the website that Malwarebytes is warning about is at corona-virus-map [dot] com. That domain was registered at the beginning of February 2020 via GoDaddy, and is set up to use nameservers based in Russia.
The Johns Hopkins map can be viewed online at https://www.arcgis.com/apps/opsdashboard/index.html#/bda7594740fd40299423467b48e9ecf6
My assumption is that the dodgy site is scraping information from the Johns Hopkins map.
Wow it's almost like whoever wrote this article should have included that information.
It's almost like the information was summarized in the screenshot and paragraph following it… :D
The article outright states that it appears to be copying the look and feel of John Hopkins hoping people would find it and think it legit.
Buuuuuutttt it doesn't state the URL until someone mentioned it ……
There's some misconception of what's happening here.
The malware is not itself a website. It's a console app installed via an executable. It does two things:
A. Launches a webbrowser control that points to the (legitimate) Johns Hopkins Corona Virus Dashboard
B. Then, using the Dashboard as a decoy, it installs malware and reports back to a C&C server.
//Don't run executables from untrusted sources
Thank you for the additional information. I've updated the article accordingly.
Sadly I visited that site on my mobile – do we know if it works on android phones?
Is https://www.arcgis.com/apps/opsdashboard/index.html#/bda7594740fd40299423467b48e9ecf6 the BAD URL???
Not sure how this is a hard concept to grasp… stop playing the guessing game with random links and just go directly to the Johns Hopkins University website (https://www.jhu.edu/). There you will find multiple banners and links directing you to the real "map".
You're ignoring something critical here. Actually three things.
(1) Humans are irrational at the best of times.
(2) People are panicking and fear – just like hate, anger and love – make the brain stop working properly.
(3) Desperation might as well also be added to that list of things. When desperate people do not reason things through as much as they might otherwise.
Make that four things.
Many people are not very good in emergencies and this is EXACTLY the psychology behind this campaign. It's not surprising at all. What is surprising is there isn't more of it. What would be even more surprising is if there was none of this. This is classical and very basic psychology at play.
So in short it's not nearly as simple as you make it. Unfortunately.