
Malvertising chains and compromised websites are targeting US users with tech support scams hosted on numeric domain names.
The goal of this scheme is to redirect users to domains consisting entirely of numeric digits like “6473819564947657419[dot]win” and “7598437654236982[dot]win.” Yes, the domains look strange. But in reality they behave like other websites.
At this time, it’s unclear who registered the domains. They all have free WhoisGuard privacy protection to hide their owner’s identity. It is known, however, that whoever is behind them created the domains in late-March and early-April.

So how does this tech support scam (TSS) get users to these domains?
The plot leverages two means of distribution. First, it relies on numerous malvertising chains. One of the most notable pathways is through AdsTerra, an ad network which has been involved in other malvertising campaigns.

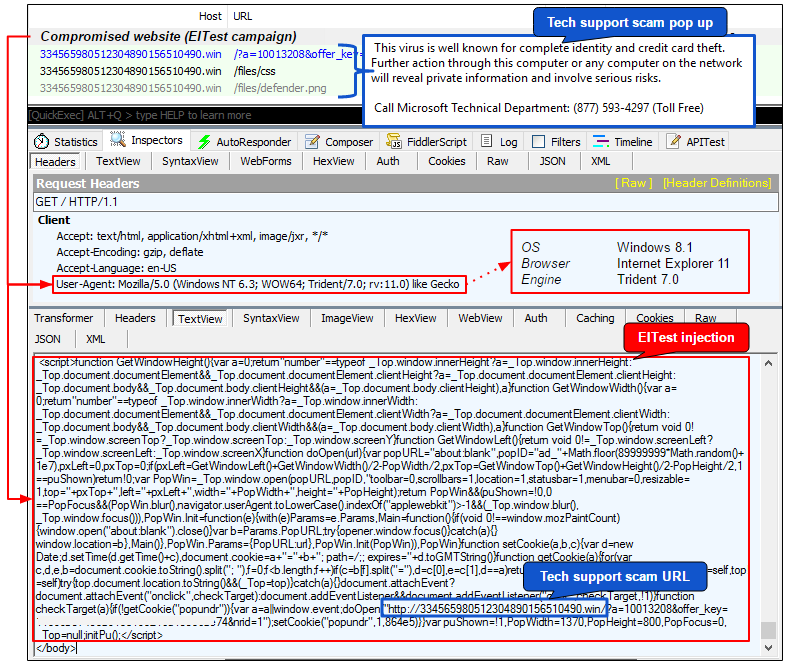
The other means of distribution involves websites compromised by EITest, an attack campaign which injects malicious script into websites that usually redirects to a landing page for an exploit kit like RIG.
Jérôme Segura, a malware analyst at Malwarebytes, has more details on this attack vector:
“A large blurb is injected into compromised sites right before the </body> tag with a URL to the numeric TSS page. What is quite noteworthy is that the URL could have been for an ad network or even one of the gates we mentioned earlier. But instead, EITest generates the right URL directly, suggesting some kind of access to the same API used in the malvertising campaigns.”
Whether via malvertising or hacked websites, users who end up on the scammy numeric domains ultimately make contact with a browser locker. These fake alerts prevent most web users from closing the page unless they kill the offending process using the Task Manager.
For instance, the popup continues to reappear in Internet Explorer whenever the user mouses over a certain part of the web page, whereas the scam abuses a vulnerability identified in 2016 that disrupts Google Chrome. Only Microsoft Edge allows users to close the page without the Task Manager.
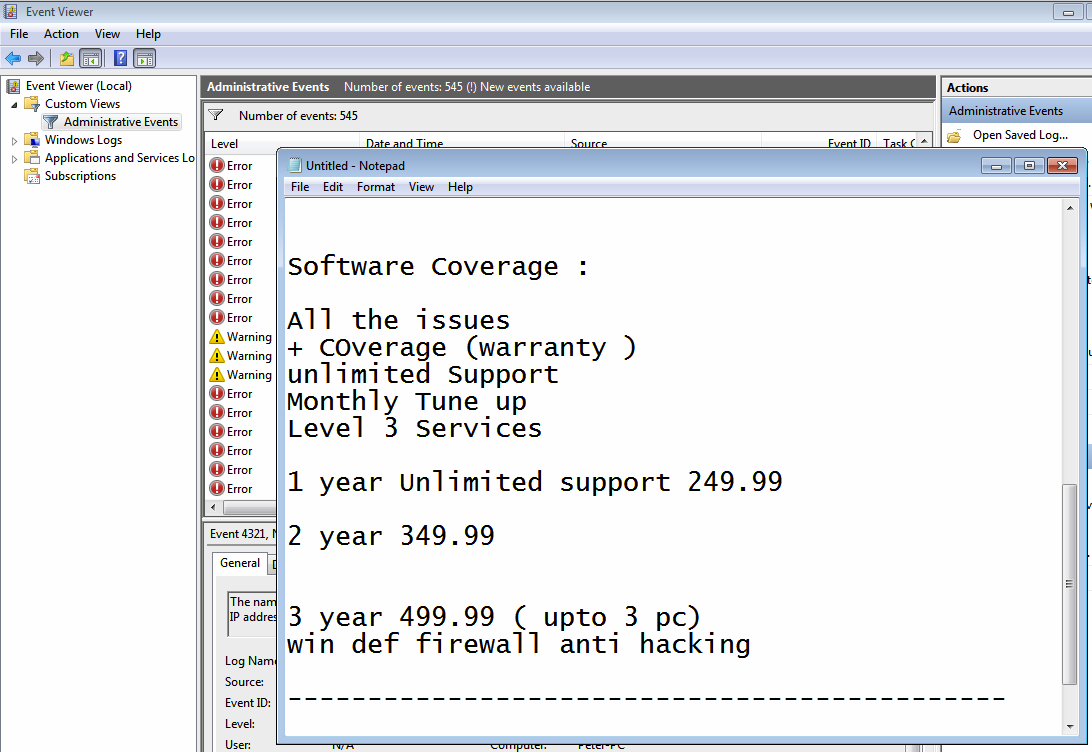
All the popups use geolocation to generate phone numbers to various India call centers. Some of these call centers try to “diagnose” the problem, whereas others go for broke and directly target users’ wallets.
To help protect against tech support scams, users should install an ad-blocker, update their software on a regular basis, and configure their browsers to disallow automatic redirects to other websites.
Should you come across a tech support scam pop, you should NEVER call the support number or give out your financial details to these fake technicians. Instead shut down any alerts using Task Manager.



My only question is, since it is known problem/site, why ICANN is not shutting it down?
Law enforcement closed a couple of big call centers in India less than a year ago. Hopefully, they can track these new ones, and close them too. International cooperation has been getting better at catching these crooks and prosecuting them.