 It seems to me that there is almost always a website making the news headlines, attempting to explain to innocent users that hackers breached its security, and stole the email addresses and passwords of innocent users.
It seems to me that there is almost always a website making the news headlines, attempting to explain to innocent users that hackers breached its security, and stole the email addresses and passwords of innocent users.
And it’s not always just the online criminals who hacked their way into the poorly-secured systems who have the opportunity to explore the exposed information. Sometimes the databases are also uploaded to the net, for anyone with an interenet conntection to mull over.
That, for instance, is one of the ways in which security researchers have managed to determine the most commonly used passwords (stand up now if you use “1234567” or something similar pitiful, you should be ashamed of yourself). And it has also helped password crackers build huge databases that help them break into accounts.
So, the first thing you want to know when there is a big database breach is if you are impacted.
That’s not always easy to determine. After all, the internet has a long memory and it’s possible that you – say – created an Adobe account years ago to download a product, and have long forgotten about it.
Enter sites like “Have i been pwned?”, created by Troy Hunt.
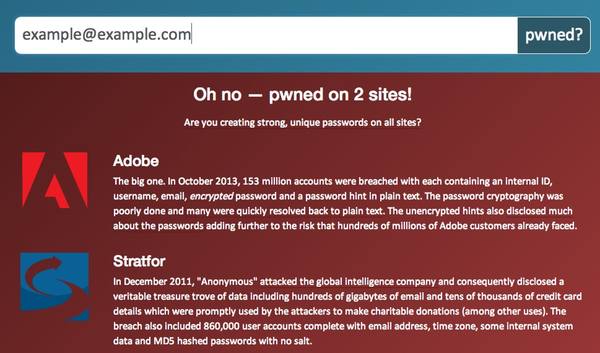
Have I Been Pwned makes it easy for you to search for your email address amongst the hundreds of millions of accounts exposed, following breaches at Adobe, Gawker, Yahoo and others.

It’s important to realise that Have I Been Pwned *doesn’t* have a database of your passwords. Troy isn’t interested in your passwords (or the hassle of securing them). He just wants to make it easier for folks to tell if they were one of those who were affected, and where they might have accounts which are at risk.
With that information in your hands, you can review whether you might need to take steps to better protect your online accounts, and ask yourself if you might be using the same passwords in multiple places (which is always a bad idea – seriously, start using password management software like Bitwarden, 1Password, or KeePass).
Right now, Troy’s project is limited to scanning the exposed databases of Adobe, Stratfor, Gawker, Yahoo and Sony to see if a particular email address is contained within. Clearly, the more that list grows the more useful his service will be.
But as more stolen user databases are publicly disclosed and made known to him, Troy says he plans to add to the list. I can certainly imagine this becoming a useful free service for people who may have fallen victim through no fault of their own.
For the last words, over to Troy himself:
Clearly we haven’t seen the last of the data breaches, of that there can be no doubt. Now that I have a platform on which to build I’ll be able to rapidly integrate future breaches and make them quickly searchable by people who may have been impacted. It’s a bit of an unfair game at the moment – attackers and others wishing to use data breaches for malicious purposes can very quickly obtain and analyse the data but your average consumer has no feasible way of pulling gigabytes of gzipped accounts from a torrent and discovering whether they’ve been compromised or not.
Of course the other thing is that I’ve only got five data breaches here and there are many more out there which I’m yet to integrate. Some of them aren’t suitable (LinkedIn only contained passwords and not email addresses), but if there are others you’re aware of that are now public, please let me know. No, don’t go and breach a system in order to contribute to this project!
Further reading: Introducing “Have I been pwned?” – aggregating accounts across website breaches and check out “Have I Been Pwned?” for yourself.



Thanks for the article Graham, I am Pwned…and yes I had a
very strong password.
Excellent, thanks for the link Graham. Hopefully further resources will be added if/when they get compromised. Had hoped that the UBUNTU forums would be on there too.
Technically speaking, simply because your email and
encrypted password has been made public does not automatically mean
you've been "pwned".
Technically yes, but if my email has been made public then I do feel pnwned (big chance). I think companies like Adobe must invest heavily in their security, this kind of breaches shouldn't have happen.
I hope big companies will learn a lesson from this year to provide a better security for their users in 2014.
Yay, no pwnage. I use keepass anyway so probably not a huge deal anyway if I did get pwned.
I am wondering the same; have I been pwned? Do you check for me or how does this work?? Thanks for attempting to think ahead of the scum bag who uses my email?