
You’ve heard of vulnerable cars and washing machines. Now hackers can exploit security flaws affecting popular car wash rigs to damage customers’ vehicles and “physically attack” people.
Back in 2015, Whitescope founder Billy Rios and Jonathan Butts, committee chair for the IFIP Working Group on Critical Infrastructure Protection, conducted a security analysis of car washing machinery developed by PDQ of Wisconsin, USA. The duo looked at PDQ’s LaserWash 360 series, in particular.
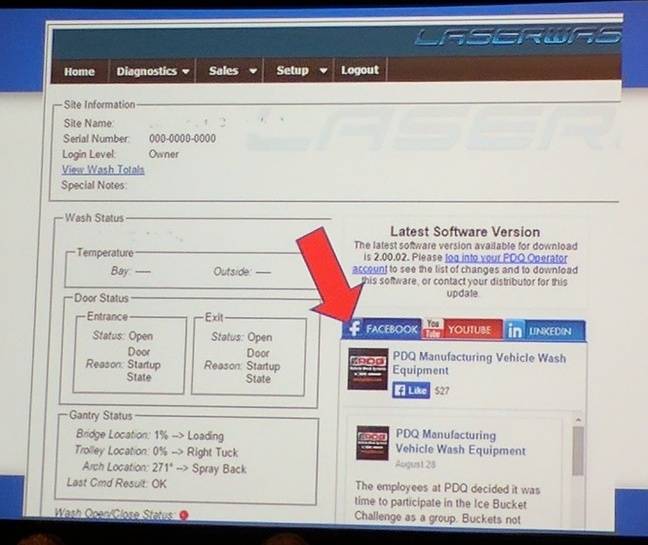
Equipped with Smart 360™ Technology that lets it “think for itself,” LaserWash enables its owners to update, report, and monitor the rig from a built-in web interface. Owners can connect this interface to the public internet to maintain LaserWash from afar. Strangely enough, they can even use the interface to keep up with PDQ on social media.
Unfortunately, this interface has some suds in its hardware.
The control system uses an embedded WindowsCE computer powered by an ARM-compatible processor. But Microsoft no longer supports that WinCE version. This means someone could potentially exploit security flaws to gain access to the system.
That’s the hard way for an attacker to authenticate themselves. If the owner hasn’t changed the default password of “12345,” they can just log in. Piece of cake.
At that point, an attacker can do some truly terrifying things with the rig. As the researchers told The Register:
“Car washes are really just industrial control systems. The attitudes of ICS are still in there. We’ve written an exploit to cause a car wash system to physically attack; it will strike anyone in the car wash. We think this is the first exploit that causes a connected device to attack someone.”
Rios and Butts found they could also close the car wash doors or slam the rig’s rollers down onto a car, thereby potentially injuring any unsuspecting passengers inside.
Given the severity of these exploits, the duo alerted to PDQ about the flaws back in 2015 but didn’t hear anything back until just before Black Hat USA 2017, where they presented their research.
PDQ told the researchers that it was impossible to patch the issues. But it did say it had worked with ICS-CERT to develop some mitigating security controls.
Anyone who owns LaserWash technology should therefore check out the ICS-CERT alert. They should then implement the security recommendations contained therein, which include isolating LaserWash’s web interface behind a firewall and changing the password to something, anything, more secure.


