 Jeep owners – you don’t want someone having “unlawful access” to your vehicle’s systems, right?
Jeep owners – you don’t want someone having “unlawful access” to your vehicle’s systems, right?
Of course not. After all, that sounds like it would be bad news. In the worst cases it might mean they could open your car doors, or mess with your steering.
Which is why you should consider installing a security update that Jeep has issued for cars fitted with a model RA3 or model RA4 radio/navigation system.
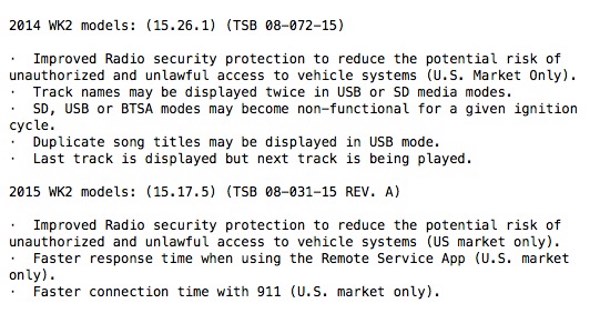
Improved Radio security protection to reduce the potential risk of unauthorized and unlawful access to vehicle systems (US market only)
Not being a Jeep owner, I wasn’t aware that a security update was available for the car until car-hacking expert Charlie Miller posted this ominous tweet yesterday:
This update might not sound particularly important, but trust me, if you can, you really should install this one. pic.twitter.com/qhTCrBIho8
— Charlie Miller (@0xcharlie) July 20, 2015
“This update might not sound particularly important, but trust me, if you can, you really should install this one.”
And when it comes to security vulnerabilities in cars, Charlie Miller knows what he’s talking about.
In the past Charlie has demonstrated his ability to not just hack into the likes of the Toyota Prius and Ford Escape, but also mess around with their braking and steering.
Check out this video, where Charlie and fellow researcher Chris Valasek took Forbes journalist Andy Greenberg for a drive he’ll never forget.
Basically, if Charlie Miller says you should install Jeep’s security update – you should install Jeep’s security update.
Details of precisely what Jeep’s update fixes aren’t made clear, but the car’s Uconnect Access system boasts that it allows car owners to start their engines, unlock doors or flash their headlamps “from almost anywhere. Just send a remote command from your computer or the Uconnect Access smartphone app.”
If you want to update your Jeep’s software, visit https://www.driveuconnect.com/software-update/, enter your VIN and download the software onto a thumb drive.
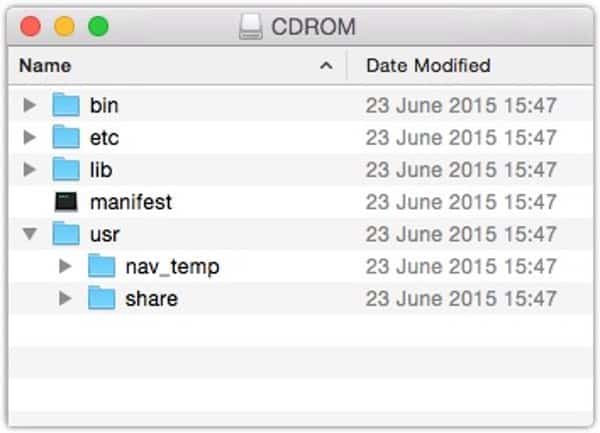
From there, consult your car’s manual regarding updating it from the memory stick.
The update notifications I have seen so far all refer to Jeeps sold in the US market. Consult your local dealer to see if a similar software update is available in your part of the world.
Update:
Well, what do you know… no sooner do I publish my article, than Andy Greenberg reveals he has been on another car journey with Charlie Miller and Chris Valasek – this time in a Jeep Cherokee.

The result of their work was a hacking technique—what the security industry calls a zero-day exploit—that can target Jeep Cherokees and give the attacker wireless control, via the Internet, to any of thousands of vehicles. Their code is an automaker’s nightmare: software that lets hackers send commands through the Jeep’s entertainment system to its dashboard functions, steering, brakes, and transmission, all from a laptop that may be across the country.
Note that the researchers believe that, although they’ve only tested it out on Jeeps, the attacks could be tweaked to work on any Chrysler car with a vulnerable Uconnect head unit.
Read the full story on Wired, and uh… update your Jeep’s software, ok?


'Ford Escape'
A very appropriate name.
It's not just jeep owners, it's all Chrysler Uconnect vehicles. I would suggest making that edit at the top of the story so as many people as possible patch their vehicles.