Back in 2020, law enforcement agents across Europe had a major breakthrough in their fight against organised crime. They managed to crack into EncroChat – a secure encrypted messaging service which ran on modified Android phones, that promised “worry-free secure communications”.
EncroChat’s customers were almost all criminals, who had no qualms about buying a encrypted phone from EncroChat (for roughly £1000), and then pay a hefty subscription for continued use of the system.
EncroChat handsets even came with a “panic” option where just entering a 4 digit code could delete all of your data, supposedly messing up any attempts by police to gather evidence of your wrongdoing.
But investigators managed to gain full control of EncroChat’s infrastructure, and could read users’ supposedly-encrypted messages in real-time.
In a livestreamed press conference this week, Europol shared the latest results of the investigation into the EncroChat encrypted messaging system – used widely by criminal groups.
Law enforcement agents were able to intercept over 115 million conversations between criminals, by an estimated 60,000 users. Europol says that the surveillance helped “prevent violent attacks, attempted murders, corruption and large-scale drug transports, as well as obtain large-scale information on organised crime.”
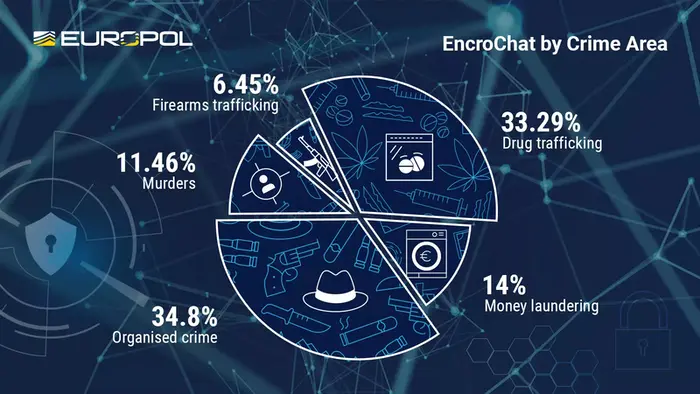
According to Europol, the dismantling of EncroChat has resulted in 6.558 arrests to date (including 197 high-value targets) – with the seizure of close to 900 million Euros, and hundreds of tonnes of drugs. To date, criminals convicted as a result of the evidence gathered from EncroChat face a total of 7,134 years of imprisonment.

As you can hear on this episode of the “Smashing Security” podcast, one EncroChat user was identified after he sent a photo of his pet dog via the service (perhaps not realising that the dog’s pet tag was revealing a phone number that he should have probably kept private.)
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Smashing Security, episode 302. Lensa AI and a dog collar. A Blog Called Bob with Carole Theriault and Graham Cluley. Hello, hello, and welcome to Smashing Security episode 302.
My name's Graham Cluley.
Now, coming up on today's show, Graham, what do you got?
He is head of IT at Bitwarden and tells us everything we need to learn about how to train staff. All this and much more coming up on this episode of Smashing Security.
They have bagged some baddies once again. They've caught some criminals and they've done it in an interesting way. Would you say yes? Say yes.
A fascinating situation to be in, of course, because you're seeing crimes being committed or you're gathering information, and when do you play your cards?
When does it become obvious that the communications are no longer secure?
But EncroChat was a supposedly secure encrypted messaging service, a bit like Telegram or Signal, but it ran on modified Android phones.
So bad guys could buy an especially modified Android phone with EncroChat.
It'd cost you around about £900, and then you would pay a subscription to access the service, which would be probably about £3,000 for the entire year.
The cops did it in an operation called Operation Venetic, or is it Venetic? I'm not sure.
So I suppose that's where it all comes from. Anyway, EncroChat was loved by the bad guys. Said to be about 60,000 users worldwide, 10,000 of them were in the UK.
The app even had a panic button where if you entered a 4-digit code, it would delete all of your data.
So if you thought the cops were going to collar you, you'd quickly go, you know, 1, 2, 3, 4, and it would delete all the data.
We talked in the past about a guy who got caught after posting a picture of stinky Bishop cheese in his supermarket and his fingerprints were picked up by the police, and they were able to work out who he was.
Anyway, they wanted to prove the identities of people who were involved in a particular drug dealing operation, because these guys had used pseudonyms.
And there was another guy called BoldMove. His real name was Stefan Baldauf. And they had a plan.
I know about what that is.
And apparently you can make a lot more money out of MDMA in Australia than in the UK. It's got a higher street value.
Anyway, the question is this: how do you sneak that amount of drugs into Australia?
It'd have to be a big suitcase, of course. I don't know.
And then we can hide the drugs inside the arm of the digger behind a lead lining.
They repaint the digger. It gets sent over to Australia. It looks all legit. And they— Well, before they send it to Australia, what they do is they put it up for sale on eBay.
And they arrange with the intended recipients. They say, look, we're gonna put this digger on eBay. Make sure you buy it, right? You pay this much.
So they panicked apparently because 6 people were watching the auction on eBay who they thought were going to make bids. And it's, this is not good.
We need only our mates to buy this. Anyway. Jeez. Their mates in Australia, they managed to buy the digger. And the digger finally arrives in Brisbane.
But of course, EncroChat has been compromised. The cops are watching it. And so, the Australian police, they X-ray the digger. They remove the drugs.
They reseal up the digger arm, and they install a tracker and a listening device inside the digger.
Now, the cops, of course, still want to know the identity of whoever it is who's done this.
So, all they knew were the code names of these guys on EncroChat, who'd sent it from the UK. So they looked at all the messages that they'd sent.
And one of them, the guy called— his name was Danny Brown. He had sent a photograph of his pet dog, Bob.
What they did, it was of course the phone number of the owner, which was there.
Now, that wasn't the only thing that these two guys had made a mistake when they'd posted up on EncroChat, thinking it was all end-to-end encrypted, thinking they were safe.
They'd also accidentally sent selfies of themselves to each other. Accidental selfie.
I was sort of propping it up. As everyone does.
In my panic, covered in soap, I dislodged the phone, which fell into the shower tray, pointing upwards.
What they did was, in one case, Danny Brown of Bromley, Kent, he sent a photo to his fellow criminals of his TV, which he'd just bought.
Have you ever encountered that phenomenon?
This is because the company Prisma Labs added a new avatar generation tool based on Stable Diffusion.
Okay, generate image. Here we go. Okay, it's thinking about it. Progress bar. All right. And oh, it's done. Okay. Poor Diana.
That looks a very uncomfortable way to ride horse sidesaddle, I can tell you. But anyway. Not very gracious, but yes, it is Diana Rigg. The horse isn't wearing clothes.
That may be my fault. She is wearing clothes though, thankfully.
Well, why don't we talk about maybe the issues that have come up with this huge slam of this? This product Lensa AI, okay?
Okay, so we know that mass surveillance can and is used in law enforcement and mass surveillance around the world.
By using something like this, you are helping to improve the tech.
The way it works with Lensa AI so that you don't end up with these abysmal pictures of Diana Rigg or whatever is that you load 10 selfies up to its iteration of it. There you go.
And from those 10, it will create a cute little avatar, sometimes up to 50 avatars. Right? Which you then can use on your socials or wherever.
Journalist Olivia Snow wrote in Wired that she decided to test the app's limits. So she scrounged around to find 10 pics of herself as a kid.
Right, she says, quote, I found a few photos of myself from childhood until my late teens.
Between my unruly hair, uneven teeth, and the bifocals I started wearing at age 7, my appearance could most generously be described as mousy.
I managed to piece together the minimum 10 photos required to run the app and wait to see how it transformed me from an awkward 6-year-old to a fairy princess.
She says the results were horrifying.
She says later in the article, for Lensa, which endeavors to beautify, as in whiten and sexualize, user-submitted content the lack of moderation similarly threatens to unleash a torrent of likewise horrifying content, in this case, child sexual exploitation material.
And I thought I'd take it as a challenge. So I'm going to name 3 tools and you tell me how you would use these as a weapon. Okay?
Perhaps if you got them to swallow it and it got stuck a bit, a bit like a fishbone with the Queen Mother. You know?
So users of non-Anglo descent have also alleged Lensa whitens their skin and anglicizes their features.
And this is a common complaint of image editing software on TikTok and Instagram.
Again, the man-made unfiltered data sourced online introduced the model to the existing biases of humankind, he said. The creators acknowledge the possibility of societal biases.
So do we.
So again, it's a shitty answer in my book because they're providing a service and taking absolutely no responsibility for blocking certain requests, which surely is their job, as it is Facebook's job to weed out scams and hate comments and all that stuff, as it's YouTube's.
So as explained in Artnet, Sarah Cascone wrote, I had no intention of using Lensa, but then my husband called my name excitedly across the apartment asking me to check out the 100 artworks the app had just created based on 20 images of my face.
Neither my husband Nathan nor I had downloaded the Lensa photo editing app, but a friend had a trial period 50% discount on image packs which normally cost $12 for 100.
He had offered to run our faces through the app, and without consulting me, Nathan eagerly sent over our photos.
I could have loaded up 10 pictures of you to find out what it made of you, but I'm then teaching the AI based on your images without your consent?
Oh, you can see the pictures that they created. So it kind of airbrushes you and gives you this weird bigger eyes, fatter lips, bigger boobs.
And Prisma Labs responded on Twitter, "The AI learns to recognize the connections between the images and their descriptions, not the artworks.
This way, the model develops operational principles that can be applied to content generation," basically saying the outputs cannot be described as exact replicas of any other artwork.
They're saying that the image that they've generated on your image is not an exact replica, and therefore, what's your point?
The other point is that they're selling this stuff cheap, right? So $8 gets you 50 avatars, takes seconds to use, and no artist can compete with that.
And well, they can, but they won't probably be eating very much. They're profiting from stolen, uncompensated, and uncredited art. That's the way I would put that.
Now, what's nice is that it's open source with published third-party security audits. Bitwarden is transparent and secure.
It utilizes end-to-end and zero-knowledge encryption with source code that can be scrutinized by all.
And the team at Bitwarden are always introducing new features to make your life easier as well as more secure.
For instance, they've just introduced passwordless login for the Web Vault, meaning you can authenticate into the Web Vault using your Bitwarden mobile app instead of entering your master password.
Learn how Bitwarden can help you do business faster and more securely at bitwarden.com/smashing and start a free business plan trial today. That's bitwarden.com/smashing.
With Drata, G2's highest-rated cloud compliance software, you'll have continuous monitoring and visibility into your risk security controls and audit readiness for standards like SOC 2, ISO 27001, GDPR, HIPAA, and more.
Plus, Drata can streamline compliance for over 14 frameworks and even automate the custom frameworks and controls you create to meet your organization's unique security needs.
With more than 75 native integrations and a risk management solution, you'll have a tool that will scale with you.
Professionals from companies like Notion, Lemonade, and BambooHR have shared how crucial it has been to have Drata as their trusted compliance partner.
Listeners, you can get 10% off Drata and waived implementation fees by visiting smashingsecurity.com/drata. That's D-R-A-T-A.
You need visibility into your fleet of devices in order to meet security goals and reduce service desk tickets.
But how do you get that visibility when different parts of your company run on Mac, Windows, and Linux? Well, you get Kolide.
Kolide is an endpoint security solution that gives IT teams a single dashboard for all devices regardless of operating system.
Kolide gives you real-time access to your fleet's data and can do things that traditional MDMs can't.
And instead of installing intrusive agents or locking down devices, Kolide takes a user-focused approach that communicates security recommendations to your workers directly on Slack.
You can answer every question you have about your fleet without intruding on your workforce. Visit kolide.com/smashing to find out how.
If you follow that link, they'll hook you up with a goodie bag just for activating a free trial. That's kolide.com/smashing, and thanks to Kolide for supporting the show.
And welcome back, and you join us for our favorite part of the show, the part of the show that we like to call Pick of the Week.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they wish.
It doesn't have to be security related necessarily.
And she was in the news this week because she was talking about how she'd had a really hard time filming a dance sequence, which appears in one of the episodes.
And I have seen the dance sequence. It's up on YouTube, and it's pretty cool. She does this kind of jerky, robotic, angular dance sort of thing. Have you seen that, Carole?
She dances a little bit like she's a marionette, but the person who's doing the puppeteering is completely and utterly rat-arsed on MDA or something like that.
But anyway, it's a peculiar thing.
And as soon as the result came back positive, you know, I got whisked away, but you know, I was feeling so bad." And it's like, "Well, hang on, what?
Hang on, so you were on a film set?" surrounded by all these other people.
Anyway, I was thinking about dancing because I'd— admittedly, it's a good dance sequence. And I was thinking about dancing.
And I was reminded— And I'd like to take you back to 1980 at the West Park Pavilion, which is the major entertainment venue on the island of Jersey in the English Channel.
And in 1980, I think it was September 1980, they held the regional final of the EMI Disco Dancing Competition on Channel TV, the local TV station.
And that has been immortalised in the form of a YouTube video where you can see all the best dancers from the best discos, not just in Jersey, which is a tiny island, but also Guernsey, and maybe Alderney as well, where there's about 3 people who live on Alderney.
I have not yet discovered whether they went on to win nationally. But it is a glorious 30 minutes watching people strut their stuff in fantastic costumes.
It took me down a rabbit hole reading more about Channel TV on the internet.
And that is why the regional final from the Channel Islands of the Disco Dancing Championship in 1980 is my pick of the week.
And I wanted to get the trifecta, all the emotions there in the story. And I had to craft it very carefully in order to get that. But boy, she lost it.
But then Maria's story and your reaction to it was really— all I can say is hand cream and horses. That's, I think that's all we need to really say to sum up the episode.
Yeah, and if you like your comedy clean and family friendly, this episode is definitely not for you.
This is, for people who don't know, this is the strange cousin of Smashing Security, the estranged cousin.
My hunksband, he's a regular listener, but only because I always want to have a second listen before I go live. He said after listening to it, pretty kick-ass beauty.
And in that vein, we have a featured interview this week, don't we, with the guys from Bitwarden?
Rico talks all about how to train people into being more secure online. Check this out. Listeners, I am thrilled to welcome Rico Acosta.
He is the IT manager at Bitwarden, and he's also responsible for the security and the security training of all his teammates. So, welcome to Smashing Security, Rico.
You know, it just didn't exist really at the time, or I couldn't find it. So, I had to make it up on the fly. There's so many more tools available to you now.
So it must be so much more efficient, effective in terms of driver training. So tell me, what's your approach to it? How does it work?
You know, when I first started working on computers, when, you know, I was a young teenage boy, you know, the internet was still not an accessible thing to most households, right?
So, you know, there wasn't, there was some need for cybersecurity, but not at all the same way now. So, you know, now it's this ever-present need for training.
And I think a big way, you know, it's vigilant and it's constant and it's never-ending. And my start to that, I think, is explaining to people why, why are we doing this?
You know, not just with cybersecurity, with anything, but especially with cybersecurity, it's important for them to understand why.
Or, you know, your teammates need to understand why they're doing it, what they're doing, right?
And because that effectively lets them know, okay, how do I act when, you know, my teammates aren't around or my direct leader isn't around?
How can I help lead others in that effort as well?
And I remember, I think when I took over the training, the reason I did it is because IT at the time was responsible and they were basically scaring the poop out of new employees by giving them rules of, you cannot do this, do not do that.
Use this number of characters or this many phrases. It's, hey, you should use a good password because here's how easy it is to crack a weak one, right? And then showing an example.
And that is much more eye-opening than just saying, hey, standard password length of whatever is insecure, whatever it may be.
If you can explain that, they buy into that, because now they understand, oh, wow, if I use this password 123, it literally takes a computer 2 seconds to crack this, right?
They can understand real-world applications, they can understand the real-world threats when they understand what we're doing here.
It's not, it's no big deal if my password is the name of my cat.' Sure. And I had trouble explaining that the weakest link, you're only as strong as the weakest link that you have.
So how do you deal with that?
They're trying to gain knowledge about you and gain access into your life and into your credentials. Right. So they don't know that you're a low-level intern or whatever it may be.
You may think, oh, I'm not this high-level person or whatever. But if your account grants access and it's inside the castle walls, now that person is inside, right?
And they can start to move around from that point. And John from accounting may be a good friend of this person, and so they can reach out to John, build access from there, right?
That's where our primary focus and development efforts are, password management. So I try and give everything equal weight. All of these things are important all the time.
So we can't focus on just one area more the other, but it's definitely a strong component. It's one that the team is highly aware of.
I would be flabbergasted to know that anyone on the team hadn't used a password manager. And there shouldn't be kind of this distinction, I think, between personal and business.
You should have them for your personal accounts as well.
I mean, even someone who uses computers only as a sideline, maybe they don't even do it for their job, will still have a dozen different accounts from healthcare to banks to everything that's vital for existence in society versus all the fun accounts.
There is no chance unless you have eidetic memory where you can memorize everything. Unless you have that, there is no chance that you remember all of your passwords.
And you may think, oh, I barely own a computer, I barely do this and this. I guarantee you have at least 20.
You more than likely have 40 to 50 different passwords for different things. It just stacks up too quickly.
You said, bank accounts, health insurance accounts, but then you think about social media accounts, or if you're part of a forum or a blog, you have logins for those things.
You have logins for your electric bill, you have logins for everything.
So I think in this current era of technology, you are doing yourself a huge disservice and you are putting yourself at risk by not using a password manager.
And it's not because you're not using the password manager, it's because there is no possible way to remember that many.
I've used other password managers as well, and I agree, everyone has their strengths, but I really love the approach that you guys take.
It's very simple to set up, especially on a consumer level. How is it from an enterprise point of view?
We can deploy quickly. There's lots of integrations that IT managers do every day and lots of backend configuration.
And I certainly feel for anybody that is in that field doing that, you can understand how time-consuming those things can be.
But Bitwarden has a very straightforward method of setup.
And what was really impressive for me coming onto the team and then taking over the reins for IT management was the documentation. The team writes excellent documentation.
It's all available online. And really, it's just well done. The team does write really great guides.
So being able to have this kind of step-by-step guide that walks through, it actually works. It's very helpful.
But typically when people are moving from one password manager over to Bitwarden, is that more complex than having someone who's never used a password manager before?
Actually, a vendor of ours, they expressed an interest in moving, but the initial roadblock was gosh, but it's like, I'm gonna have to invest so much time.
No, let me show you real quick. Let's hop on a quick call. 5 minutes, let's talk about this. And it's very easy. It's very easy.
So prior to using Bitwarden, I was using a different password manager. And I thought the same thing.
You know, what if everything doesn't transfer properly, and all this, but when you dive in, it's simple. I mean, it's straightforward.
And I think that's part of the Bitwarden business model in a way, right? Let's make things that are easy. Get out of the way so the user can use it. That's so important.
And that helps build that buy-in, helps build that use. Because if something is so complicated all the time, you're not going to use it, right?
And that includes everything, you know, switching over to it, you know, personally, or even switching for an entire organization. Enterprise situation. It's straightforward.
It's simple. It helps your users get up and running quickly and be about their day.
You know, I think obviously with some bias, it's a really great product. If you're not using Bitwarden, that's okay. We'd love for you to try it out, obviously.
But please use a password manager.
And Rico Acosta, IT manager at Bitwarden, thank you so much for making time to talk to us today.
It's really terrific as an independent podcast to have support from brands such as Bitwarden. We really appreciate it.
And if you want to check out Bitwarden, go to bitwarden.com/smashing. Well, that just about wraps up the show for this week. You can follow us on Twitter while Twitter still exists.
We're @SmashingSecurity, no G, Twitter won't allow us to have a G. And we're also on Mastodon.
If you want to find us on Mastodon, easiest thing to do is go to smashingsecurity.com/mastodon and it will take you to our account.
And look up the Smashing Security subreddit on Reddit as well.
And never forget, if you don't want to miss another episode of Smashing Security, sign up, follow us in your favorite podcast apps such as Apple Podcasts, Spotify, and Google Podcasts.
It's thanks to them all that this show is free.
Episodes, show notes, sponsorship info, guest list, and the entire back catalog of more than 301 episodes is all on smashingsecurity.com.
Just, you know, please, I'm putting it on the table.
In another hilarious case, a drug dealer from Liverpool was identified after he sent a picture via Encrochat of some mature Stilton blue cheese he was buying at a supermarket.
What he didn’t realise, as we describe in a different episode of the “Smashing Security” podcast, was that the photo showed enough of his palm and fingertips for Merseyside police to identify him.

Imagine believing you’re a big cheese in the world of crime, and to be caught out in such a way…
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Hello, hello, and welcome to Smashing Security, Episode 229. My name's Graham Cluley.
And I'm the founder of securerepairs.org, which is a group of security and information technology professionals who support the right to repair.
Coming up on today's show, Graham, what do you got?
Well, you know, in the middle of the night, if you can't sleep, do you find yourself sneaking out of bed, trying not to wake your partner, creeping tippy-toe down the stairs, opening the fridge, and hallelujah!
There, hidden behind the kale and the quinoa, there it is, the thing which will satisfy all of your munchies: some stinky cheese.
I could go down to the fridge, no one would, you know, I wouldn't wake anyone up, whatever, whatever. But I never do it.
I am going to give you a name, and you, you are the contestants, Paul and Carole. You have to tell me if it is a cheese or something else narcotic. Okay?
Are you ready to play the game?
Okay, next one. Poochie love. Poochie love.
I'd become a rent boy if I thought I could fund my love of a stinky bishop. But some people, some people aren't like me.
Some people haven't gone as deep into vice as me, and they've contented themselves with the likes of cocaine, heroin, MDMA, horse tranquillisers, that kind of thing.
And it's not just from the Wallace and Gromit, but I mean, of course, here in the United States, we are defined by American cheese, which if you've ever had it, that's not cheese at all.
It's barely cheese. I mean, it's mostly noticeable for being incredibly regularly square.
Do you guys know what EncroChat is?
Now, can you imagine who would be particularly interested in spending thousands of dollars and a regular subscription to have such a phone?
And apparently it had over 60,000 users worldwide, 10,000 in the UK. And everyone thought they were safe with it, right?
They thought, I've got this special phone, I've bought it from this French company, EncroChat, and if the cops ever come knocking on my door, all I have to do is enter a 4-digit PIN onto the phone and it wipes automatically all the data from the phone.
And they had this chap, Carl Stewart, who they suspected was supplying large amounts of Class A and Class B drugs under the name Toffifee. How could they prove this?
Well, it turned out that this chap Toffifee was a lover of Stilton cheese.
What he did was he had posted on EncroChat a photograph of a block of Stilton cheese in the palm of his hand while standing in the aisle of Marks & Spencer.
And from that picture, just of his hand holding the cheese, the police were able to identify him.
Carl Stewart, this chap with the cheese, he's now been sentenced to 13 years and 6 months in the clink.
And usually what that means practically, because you'd be like, well, I can repair it.
But these days, increasingly, because everything we use basically has software on it, and also these days digital locks, right? Like DRM, digital rights management software.
Owners need more than just the thing itself. They need access to the software that runs it to read error codes and figure out what's wrong with it.
If there's a part, a component on a circuit board that has burned out, they need a schematic diagram to figure out where that component is on the board and a part number to replace it themselves if they want to do that repair.
And so right to repair laws basically codify that in law and say, as a manufacturer, if you make a thing and you have authorized repair people who get access to these tools and parts and information, then you also need to make that available to your customers, the people who own the device and basically their agents, people they might hire to do a repair.
So independent repair shops.
I think most people don't pay a lot of attention to this, but it is a movement that's been picking up steam both in the EU and in the UK and in North America and in Australia, and really has a lot of people paying attention to it.
And I think because we are increasingly inhabiting a world of intelligent, internet-connected, software-driven stuff, and the more onerous these kind of manufacturer-imposed ecosystems, kind of walled gardens become, the more people are kind of taking notice of this and saying, "You know what?
This is not fair," or, "This is inconvenient for me," or, "This is costing me money needlessly." I want to do a repair myself.
And I spilled all the whiskey all over the keyboard of the laptop, which basically, you know, I then put it upside down in rice because I read that was a good idea, but it's not been working really well.
So in that situation, are you saying that that would be something I could say, look, you have to help me try and fix this?
And in that situation, there is probably some damage caused by that that is preventing your laptop from working correctly.
You can try to repair it yourself if you're technically inclined, and many people are, or you could hire an independent, in other words, non-authorized repair shop to do it.
And generally, it's your automobile, right? Your car.
If you bring it to the dealership and their repair people, they'll have all the parts and tools and stuff, but it might be more expensive.
If you bring it to the corner repair shop, same thing, they'll be able to fix it, maybe slightly less expensive.
Maybe they won't use the manufacturer's OEM parts, but you'll save money.
And obviously if you go out in your driveway and go under your car and repair it yourself, that's the cheapest solution. And that's a functioning market.
The way it works for many devices these days, including your MacBook, you need parts and access to information.
So the reality for many consumers today who are in your situation is they bring their you take your MacBook to the Apple Store, to the Genius Bar, and they say, mm, they take it out back and light incense and wave their hands over it and bring it back out to you and say, sorry, no, liquid damage.
We don't do repairs this. We suggest that you buy a new MacBook.
Apple doesn't want to hire and retain the people to do the soldering work or the more complex repairs that would require.
It is not the cheapest option available to you. Your old laptop gets thrown in a landfill where it leaches dangerous chemicals into the earth.
But that's the way that system's set up.
The other alternative would be to take it to an independent repair shop where they might have the skills and tools to repair that liquid damage.
But many of those independent repair shops do not have access to the tools that Apple makes available to figure out, okay, Carole spilled whiskey into her laptop.
What components actually burned out?
Tools that they don't make available to non-authorized repair people. They also don't make the parts available.
So if you want to replace a discrete component, they don't give you the schematic diagram to tell you what those parts are and where they are.
And they don't give you access to the parts.
Companies like Dell and Hewlett-Packard make both parts diagnostic tools and schematics.
Which is our parts are superior to their parts. Their parts are going to break or cause you to get in an accident.
Our mechanics are PhDs walking around in lab coats and their repair people are grease monkeys without high school diplomas.
You know, we care about the safety and privacy of your data and those other people are probably criminals who will steal it and sell it.
So it's a bunch of kind of misleading and untrue qualitative statements about the superiority of authorized repair, but there's no data to back up any of those claims, but they make them anyway.
In the case of Apple, there certainly is, you know, obviously having a monopoly on aftermarket service and parts is incredibly valuable to Apple.
You know, they make money off the Genius Bar, certainly.
However, I actually think that that's less of an issue for them than the fact that they really want to try and create a situation where the lifecycle of their phones, particularly, and iPads is as low as possible.
They want you to get a new phone every 2 to 3 years.
And if there are robust repair options that let you extend the life of your phone to 5, 7, 10 years, that has a major impact on Apple's revenue models.
For other companies, and I've written a lot about John Deere, a major US agricultural equipment maker, it seems clear that the monopoly on the aftermarket parts and service is the point.
And service revenue as a percentage of their overall revenue has skyrocketed in the last 10 or 12, 15 years as they've been able to basically lock out independent repair and owners from being able to work on their own stuff.
Okay, so first of all, let me tell you, do you want the, this is a cybersecurity podcast, so here's the link to cybersecurity.
Before COVID they were a thing. And ended up talking to a guy, Nathan Proctor, who is the head of the Right to Repair program at US PIRG, the Public Interest Research Group.
And he was talking about the efforts to get this law passed in some of the states in the United States.
And he was saying that one of the big arguments against, one of the things that sends lawmakers screaming is cybersecurity.
That vendors, OEMs can come in and say, hackers, hacking, data theft, and people kind of run screaming.
And I knew enough to know that those arguments were almost certainly not accurate, that there wasn't really a cyber risk in repair and the types of things these laws were asking about that devices get hacked because of other problems.
Right? You know, poor configuration, vulnerable software, you name it.
And so I started this group Secure Repairs to basically say, listen, as a security community, we should speak with one voice on this and we should speak the truth about where security risks are with connected devices and where they aren't.
And we should use our influence to sort of try and bend this policy discussion in the right direction. And the right direction being the one based on facts and not fear.
If I made a cell phone and the world decided, oh my God, I need to have that, and everyone bought it, yes, I would be an absolute control freak about everything about it.
I would be exactly the same and it would suck. And I would need people like you on my case.
And we called it Yik Yak.
Like, we were making up this algorithm for ourselves, like hair color, height, right?
Did that ever occur to you?
There's a shift. So it obviously had a reputation for being a little fast-paced. You know, I knew people who could munch through matches as though they were Skittles, right?
The BBC suggested that some of the changes might be here to stay even as life returns to normal, because of course this all has to do with the pandemic.
So someone said, I think video calls are very much here to stay as a means of pre-screening people you meet on apps.
I feel it's definitely a positive trend. I'm now going on fewer dates, but when I do, it tends to be far more likely that date goes well.
But then pandemic happened.
And this is confirmed by people like Match Group, you know, which own dozens of dating apps, Tinder, OkCupid, Hinge, or Hinge, as some of us like to call it.
They reported an 11% increase in average subscribers in a 12-month mid-pandemic period. That's pretty big, right? And they just think that the pace is slowing down.
So the data is showing that people are being more selective and intentional about who they're reaching out to in the first place.
There's a jeu de mots there somewhere in the OMIA.
As someone described it in an app review, saying the search function is very detailed, allows you to specify preferences in various fields including nationality, education, income, and body type.
So in Japan, that seems to be the 4 things that matter. Nationality, education, income, and body type. So Japanese, smart, rich, thin. That's all they care about, it seems. Okay.
It focuses on trying to offer its customers an opportunity for a long-term relationship rather than a short-term fling.
I don't think it is.
So they did this and they said that the personal data of 1.71 million users was likely to have leaked due to unauthorized access to its servers.
Okay, and that is the biggest drop that company ever saw since it got listed in 2017, and they're valued around $70 million. So a big chunk of change.
The parent company notified the public of the breaches, and they've put together this document which I want us to look at in a second.
But basically apparently the still unknown hackers have made away with usernames, photographs, as well as data from ID cards, driver's licenses, and passports, all of which were mandatory during the registration.
And this was all for their security messaging, which we'll get to in a second.
And has probably read millions of these.
You may have to do a little quick Google Translate depending on how good your Japanese is, 'cause I don't think I can send it to you in English.
From a liability standpoint, right?
So inconvenience, I think, is a little bit of a light word considering you've somehow my passport number has gotten snarfed along with all my other personal ID.
But they say at this time they're searching the web and they're saying they're not looking. Let's see, that's a really hard statement to make, right?
Like, we haven't seen it be used, therefore it's not happening yet because maybe we're not looking in the right places, you know? I don't know.
So they— but like health insurance cards, passport numbers, they have this also, this ID number Japan, the numbers, car driver's license.
I like the deep bow thing as well, and I would love to see Western companies do that because I think it's both deserved and would be a really welcome change from the sort of legalistic, "Regarding the incident that occurred last week regarding our members." If you were offended, we're—
"We have no reason to believe that any of the stolen information has been used." It's like, "We have no reason to believe that the $600 they took from your bedside drawer has been spent." Well, I think it will be spent.
I think that's actually why they took it.
They say basically there, we make various efforts so that users who want to have a serious relationship can use it safely and securely.
So we only display nicknames, only the people that have passed the age confirmation, which we have, you know, checked through every single.
Only people who've uploaded their passport will be allowed onto the site.
And you know what, that when I look at these faces, they all look young.
You applaud them for their sincere efforts to verify the actual identity of all their applicants, but you wonder, having verified that identity, why are you holding onto this data?
Because it's like the 30,000-gallon tank of spent diesel fuel in the back of your lot. If it just sits there long enough, something bad's gonna happen.
But I'm guessing it would be an ugly scene.
In the world of security, we call confidence tricks social engineering. And as our sponsors KnowBe4 can tell you, human error is how most organizations get compromised.
Where there's human contact, there can be con games. It's important to build the kind of security culture in which your employees are enabled to make smart security decisions.
And to do that, they need new-school security awareness training. KnowBe4, the provider of the world's largest security awareness and simulated phishing platform.
See how your security culture stacks up against KnowBe4's free phishing test. Get it now at knowbe4.com/freetest. That's K-N-O-W-B-E and the number 4 dot com slash freetest.
Think of KnowBe4 for your security training.
All kinds of teams can securely share everything needed to work together. Give employees access to logins, documents, credit cards, and more on all of their devices.
See if company email addresses or credentials have been exposed in a data breach and get alerts when accounts are compromised, so you can update passwords right away.
Find out more and try 1Password for free for 14 days at 1password.com.
In today's work-from-anywhere era, CISOs and IT executives work tirelessly to make sure the organization's information assets and technologies are properly protected.
And this increased pressure has led to deteriorating mental health, addiction issues, and even suicidal thoughts and tendencies. OneLogin's message: you are not alone.
Smashing Security listeners are invited to attend their live event on Wednesday, May 26th, for free. It's called Keeping the Mind Clear and the Company Secure.
Learn more at smashingsecurity.com/oneloginiamokay. That's smashingsecurity.com/oneloginiamokay. And thanks to OneLogin for supporting the show.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they wish.
It doesn't have to be security-related necessarily.
I have, over the last few days, watched a TV program on the old television, in fact, on BBC iPlayer, and it is an adaptation of a book by Nancy Mitford called The Pursuit of Love.
He was also in Fleabag, if you remember him. And we also have Emily Mortimer, who appears as the Bolter, who is the mother of one of the characters.
And Emily Mortimer, the actress, also directs, and she wrote the adaptation as well of The Pursuit of Love. And it's really very entertaining.
I wasn't quite sure what to expect when I started it, but I thought, oh, this is a lot of fun, and I greatly enjoyed it.
And I was reading an interview with Emily Mortimer where she said it was partly based, or at least inspired by, that Marie Antoinette movie from a few years ago, which had modern bits and period bits, but modern music and all the rest of it.
It's cut very well.
And it's by Renee Dudley and Daniel Golden. This is one of those stories that I didn't write, but I kind of wish I wrote.
First of all, it profiled the work of this group called the Ransomware Hunting Team that is a volunteer group that helps ransomware victims get free of the ransomware and kind of works behind the scenes.
Really interesting looking at that.
It's also interesting because it talks a little bit about some of the ethical quandaries that cybersecurity firms face when they look to both call attention to their wares and their technical expertise, but also in the process might actually do a favor for some of the cyber criminal groups that they are actually working against.
And that was a big red flag to the DarkSide group to fix that flaw in their ransomware, which they promptly did, and then thanked the cybersecurity firm for ticking them off.
So there was a big discussion in this article just about that dynamic. What is the moral responsibility of cybersecurity companies? And is there a right way to do this?
Because if you produce a tool to decrypt the damage done, you want to tell people that it's available because there may be victims who never find out that there's a tool available or there's a way to do the decryption.
You know, did Franklin Roosevelt know about Pearl Harbor but didn't do anything because he knew that then the US would be able to get into the— I mean, these type of ethical quandaries come up all the time.
And in the cybersecurity ransomware world, they come up all the time as well.
The big problem that this article raised, and this is a sort of structural problem, is that the traditional people we look to to address these problems, like the FBI or Scotland Yard, are way behind even volunteer groups like this ransomware hunting team in actually being able to intercede and help companies.
I wrote an article for Security Ledger years ago, in 2014, based on a presentation I had seen in Boston by the head of the Boston FBI, where he basically told an audience, if you get infected with ransomware, just pay the ransom because we can't help you.
The encryption's too good. We don't have the technical expertise to decrypt this stuff. So just pay the ransom. We can't spin straw into gold.
We don't have the ability to do this— behind the bad guys in terms of our technical expertise and our ability to fight back.
Carole, what's your pick of the week, brackets, not security related, close brackets.
Well, if you used to take pictures with an old camera and you miss the flexibility of that, but you don't really want to carry around a DSLR all the time. And it's called Obscura.
Basically, Apple has a very good native app, but it's highly automated, right?
And to some people that might be used to taking pictures with old cameras, it can feel a bit like a digital straitjacket because you don't have any manual control over the images.
I mean, it's been getting better. I'm not saying it's the worst, but I'm just saying for a— However, you can get Obscura, which I really like.
You get full control over the key camera settings. The UI is very nice, easy to kind of intuit and clear, speedy, and it's got great haptic feedback.
And it also can read different picture formats. So JPEGs, but also the Apple HEIC and the RAWs and all those things. And it works in landscape portrait and has loads of filters.
Filters, which I haven't, I'm not really into filters, but if you are into that, there's tons of them. And it's just a really cool app. And I think well worth the money.
So if you're into—
And I'm like, no, no, just go to the other app and then fix the exposure and I'll get a much better pic. So it's worth it. So the app is called Obscura and it's my pick of the week.
All right, we're here with someone who has actually been a guest host on Smashing Security before. That's Javvad Malik. He is a security awareness advocate at KnowBe4.
Welcome, Javvad.
So on top of being a security awareness advocate at KnowBe4, you also are a host on a podcast, you're a popular vlogger and blogger, you do events, you're basically an all-round security pundit.
Would that be fair?
That's what I aspire to be in the security world.
So can you tell us a little bit about the company and what KnowBe4 does?
You know, we talk about all our layers in security and we have all of our technical layers and protect and defend and detect and respond and all that kind of stuff.
And majority of times we're focusing on the technical layers, which are very important. But what KnowBe4 focuses exclusively on is the human layer within that.
So people, they make mistakes and/or they can be fooled. And criminals, they, you know, if breaking into an organization technically directly is quite difficult these days.
So it's a favored technique is to just go after the user.
So whether that be a phishing email, of sending them a USB or drive to plug in or phoning them up and pretending to be someone and getting them to do something that's not in their best interest.
That is the preferred method that a lot of criminals break into organizations.
I mean, even if you look at a lot of these threat intelligence reports that track nation-states or organized criminal gangs, the majority of the time, point of entry is through phishing emails.
So what we do at KnowBe4 is we help try to strengthen the humans.
We give them security awareness and training, help them practice in a safe environment by sending them simulated phishing emails.
And then there's a whole ton of awareness content on the back of it in the form of videos and games and all the other material like posters and what have you, just to help people, you know, just remember what's important and what to do if they suspect anything to be a bit malicious.
You go knowbefore.com/freetest and you can sign up there. And what you'll see is that there's thousands of templates there. And these are in different languages.
They're bundled into different categories. So if you want, hey, let's do social media type one.
So you can say, okay, let's send our users a LinkedIn phishing template because that's quite a popular one in the work area.
You can tailor it to be, you know, more specific or more generic. And, you know, it goes off to all the users that you specify.
And the great thing about the platform is that it can randomize the time it sends them out.
So it's not like everyone in the office gets the exact same template at the exact same time, because you then get the meerkat kind of response where one person gets it, he looks up, and they look around and say, "Hey, has anyone else got this?" And everyone's "Yes, we got this." And then it kind of defeats the purpose of the test.
And then what you can do, you can see how many people have opened the email, how many people have clicked through on a link or whatever the payload might be.
It might be a link, it might be a, hey, enter your credentials here, it might be reply or whatever that is.
And then also you can see how many people have reported it to your security team.
So whether that's an internal process you have, if you receive a suspicious email, forward it to the security team, or you can download our Phish Alert button, or PAB for short, which is a Gmail and Outlook plugin that sits in your inbox.
So if you see an email that looks suspicious, you just click the button and it takes it out of your inbox and sends it to the security team to investigate.
They actually get to decide themselves completely. It's almost like an autonomous effort.
So they're best placed to make the right decisions if they have the right relationships.
And we've seen examples of where this has gone wrong, where they should have that environment where they tell people, hey, if you receive phishing email, this is what you should do, this is what you should look out for.
We're going to be doing simulation tests at this time throughout the year.
And these are some of the topics that we think are inappropriate for our user base because of whatever reasons.
It's when you get that wrong, people, instead of being educated in a phishing test, they end up getting annoyed.
We're all trying to get better here. We're not trying to catch people out and punish them for making a mistake, which frankly anyone can make.
What you'll get is people trying to bypass security to do things in a secret way, which puts the company presumably more at risk.
So it's important to work with the people to see that the point of this is to get people educated and protect the firm and the individuals.
And there was a biomedical institute and they partner with some universities and there was some visualization tool that you could use if you were on-premise.
But if you're using your own machines, which everyone was because everyone's working from home, they weren't offering a license for that, and the license was really expensive.
So what a user ended up doing, or a student, they downloaded a cracked copy, and Windows Defender threw up an alert, and so they disabled Windows Defender.
And this is the thing, is that people are just trying to do their job most of the time. They're trying to be helpful, and they're trying to get their work done.
And technology should be there to facilitate them in doing what they do.
And if it's there as a blocker, and security is no exception, security is probably, when implemented poorly, it becomes the biggest blocker.
If it's not implemented properly, then people will find creative ways to bypass it just to get the job done. And unfortunately, that does open up or exposes the company to breaches.
And most companies, when they do their first test without training and everything, it's typically over 30% of people will click on a— will fall victim to a phishing email. Right.
And that's a high percentage. That's like 1 in 3 people nearly.
If people have gone through a few simulations, have included, you know, presentations and education provided internally?
You know, typically if you're doing monthly sort of simulated phishing and you're offering ongoing awareness training, so you sign them up to courses and they can be short ones, but it's less but more often is probably better.
And you've run it like a proper campaign, then after 90 days even you can halve that to about 10 to 14% of people.
And if you actually carry that on for a year, that drops down to about 5%. So a significant reduction can be achieved over that period of time.
So I'm thinking and breathing and snarfling security all the time.
But people who work in other industries, say retail, finance, health, are they thinking about security as much as they should be, do you think?
If you take a problem to a security person, they're gonna reframe it as a security problem and present you with a security answer. So I think you're right.
We have this bias because we are in this echo chamber as security professionals or practitioners and other organizations and people working in other departments, they don't have that lens and they're looking at things, hey, what's our return on investment?
What's our profitability this quarter? How can we make it out of the pandemic without going bust?
If you ask me from just a pure security perspective, I'm no, people don't pay attention. And you know, they do far too little, far too late.
But I think on the flip side, I think when you look at over the last couple of decades, there is a rise in awareness.
People are a bit more clued on, and especially from a technical perspective, operating systems and platforms are a lot more secure than what they used to be.
Security, cloud services are really good by and large, but it's just making people aware of some of the dangers that are still out there.
And we see it all the time with unsecured S3 buckets out there.
It's not that the functionality doesn't exist, it's just that someone just forgot to check or didn't think to check that should this option be ticked to private or public.
It's like any behavior change, and that's ultimately what we're going for. It's like behavior change.
When we look at things like environmental awareness, growing up, there wasn't really a concept of recycling or separating out your rubbish. Throw away your rubbish.
But today you walk into any corporate office or even public dustbins, there's at least two, if not more, there's maybe five in some offices where when you go to throw away your rubbish, there's oh, let me separate my recyclables from my landfill and what have you.
And this is something that happened over a long period of time and raising awareness. And I think that that's the process we're going through at the moment with security awareness.
I think it's important for us to understand how we are being duped, and that changes all the time because, of course, as soon as we're all aware that something can happen, we tend to be on our guard.
So they change the pattern, and people like KnowBe4, for example, are paying attention to that all the time.
So I guess you're updating these tests and constantly providing new information so people can kind of get tested against what's going on right now outside.
Javvad Malik, thank you so much for coming on the show.
As every self-respecting journalist does these days, which is fighttorepair.substack.com.
And we're also up on Reddit, so look for the Smashing Security subreddit up there.
And don't forget to ensure you never miss another episode, follow Smashing Security in your favorite podcast app, such as Pocket Casts, Spotify, and Google Podcasts.
It's thanks to them all that this show is free.
For episode show notes, sponsorship information, guest lists, and the entire back catalog of more than 228 episodes, check out smashingsecurity.com.
Well, quite a few of you decided to take part and take that 60 seconds to write something nice about us. Well, guess what? It's really helped.
We've had our most downloaded show ever last week. How frickin' cool is that?
This week I want to do a shout out to Zixis, who wrote, "Many thanks to the hosts and guests for making the flow of entertaining and thought-provoking content.
Listening to the podcast used to be part of my commute, and now it's an even more essential part of my lockdown endurance routine. Awesome and well done." Thank you, Zixis.
And also to Red Piano Roland. "Always my pick of the week. This show never fails to make me smile. I always look forward to each new episode and listen whilst doing the cooking.
It's been a rough few months, and you guys have always been a lift to my spirits. Thank you, Graham and Carole." You are so, so welcome, Roland. Red Piano Roland.
Guys, if you've got the time, please keep them coming. It is seriously making a difference in keeping us independent. Plus, it's just really, really nice to hear from you guys.
Otherwise, it's just Graham, and I mean, ugh. Buckets of love.