
There’s bad news if you’re a cryptocurrency investor. Billions of dollars worth of wealth were wiped out this weekend after a South Korean cryptocurrency exchange was hacked.
The exchange in question is called Coinrail, and if you visit its website right now you’ll see a “System maintenance” message that tells you more than they’re just updating the servers. The devil’s in the detail – the site is down because it got hacked over the weekend.
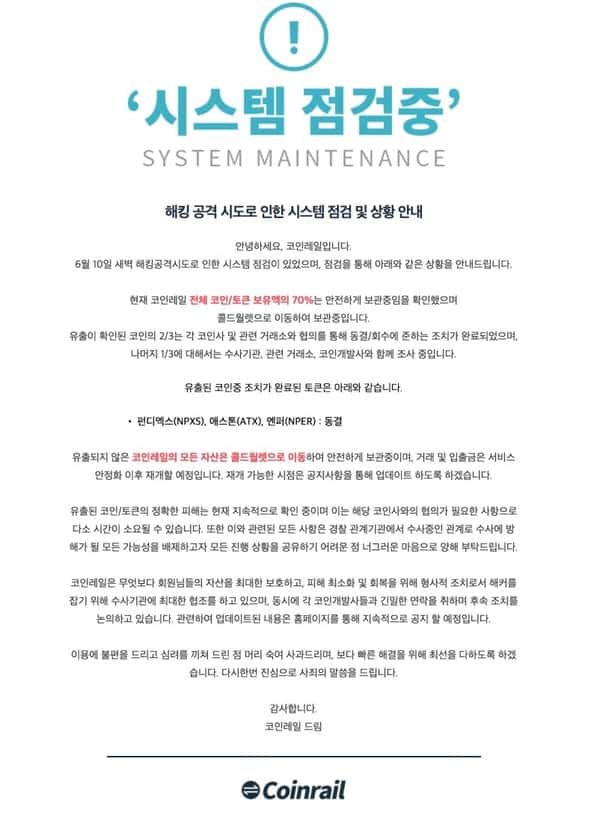
The statement on Coinrail’s website says that some (but not all) of the cryptocurrency exchange’s digital currency was stolen by hackers. Coinrail claims that 70% of the cryptocurrencies it holds are being stored safely in a cold wallet which is not connected to the internet, and thus considerably more difficult for criminals to access.
Coinrail hasn’t released much information about what has occurred, but has released released the names of a few of the tokens affected in the hack: ATC from Aston, NPXS tokens from the Pundi X project, and NPER project tokens.
In all, the hackers are thought to have stolen about 30% of Coinrail’s virtual currency, and that news has sent shockwaves through the markets.
Even a hack of a relatively unknown South Korean cryptocurrency exchange like Coinrail can have a big impact on cryptocurrencies worldwide, because of media coverage. Media coverage gives investors the jitters which makes them sell more cryptocurrency which then leads to more media coverage, and so on and so on…
Stephen Innes, head of Asia Pacific trading at Oanda Corp, told Bloomberg that he believed panic-selling was to blame for the drop in cryptocurrency value:
This is ‘If it can happen to A, it can happen to B and it can happen to C,’ then people panic because someone is selling. The markets are so thinly traded, primarily by retail accounts, that these guys can get really scared out of positions. It actually doesn’t take a lot of money to move the market significantly.
So far this year Bitcoin is down about 50% in value. On Sunday alone it fell 6% after news of the Coinrail hack broke. And it’s not just Bitcoin that’s suffering, other commonly traded digital currencies like Ethereum have also taken a dive.
The problem with Bitcoin seems to be its very volatility – the thing which attracted many investors when its price was rocketing skywards last year, and is now proving a challenge as more people view cybersecurity as a huge threat to virtual currencies.
There is, of course, going to be plenty of speculation about who might be behind the Coinrail hack, and no doubt some will cast an eye north of South Korea’s border in their search for likely culprits. However, in cases like these it’s very difficult to attribute an attack on a cryptocurrency exchange with any certainty – as there are so many criminals who would salivate at the thought of breaking in and making off with millions of dollars.
Why is cybersecurity such a big issue to cryptocurrency exchanges and not seen as such a significant threat to traditional financial insitutions?
Mikko Hyppönen summed up the situation well in a tweet:
Cryptocurrency exchanges are ideal targets for attackers. Small companies with a lot of money. Run by startups, with small security teams and no experience. And if you get in, the loot is already anonymized and untrackable. https://t.co/uvBd6Shnox
— @mikko (@mikko) June 11, 2018
My advice? If you have a cryptocurrency investment, don’t leave your wallet lying around in an online exchange. Keep it somewhere safer.
In a past episode of the “Smashing Security” podcast we’ve talked about how you may wish to consider having your own hardware wallet that stores your private keys, so you have true control about when and where your funds are moved… rather than put your trust in a cryptocurrency exchange.
And, it should go without saying, if don’t invest anything that you cannot afford to lose.
Listen to this edition of the “Smashing Security” podcast to hear further discussion on this topic:
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
So what sort of cyber attacks do you think we might see which are in relation to the World Cup? Could these be sort of retaliatory attacks from other countries against Russia?
Or might we see patriotic Russian hackers attacking Brazil, for instance?
Hello, hello, and welcome to Smashing Security, Episode 82. My name is Graham Cluley.
And it's the only way I could think of doing it.
Over 1 million files are uploaded every day by folks analyzing malware and attempting to determine what different antivirus products call a sample.
But you can do much more than that with VirusTotal Intelligence, which helps you get more context about your alerts through advanced malware threat hunting.
Relationship and behavioral visualization, as well as historical analysis on billions of malware samples.
To learn more about how VirusTotal Intelligence can help you, visit virustotal.com/learn or email the team at .
And be sure to say you heard about them on the Smashing Security podcast. And welcome back. Well, the big news over the weekend— did you see what happened? With the bitcoin price.
Carole, John, do you religiously follow the price of bitcoin?
Well, it's bad news if you were a cryptocurrency investor, because billions of dollars worth of wealth were wiped out this last weekend after a South Korean cryptocurrency exchange was hacked.
And if you visit the website right now of Coinrail, South Korean cryptocurrency exchange, you will see that they're undergoing a little bit of system maintenance.
Those are the only words in English. Now, I don't speak Korean.
And according to CoinRail, hackers stole about 30% of its virtual currencies, and that has sent shockwaves through the market because even though most of us probably haven't heard of Coinrail, right?
I mean, I imagine they might be known in South Korea, but not in the rest of the world. Their hack still had a big impact on cryptocurrencies around the world.
And it's because of media coverage.
But what's happened is the media coverage about that has given investors the jitters around the world and made them sell more cryptocurrency, which in turn has led to more media coverage.
And you get into this sort of whirlpool of fear and, oh my goodness, sell, sell, sell, sell, sell, sell, sell.
The more you sell, the more stories there are, the more people who sell. So I put it to you, Mr. John Leyden, representing journalists today, that it's all your fault.
He just needs a minute or two to decide whether this is someone he can do business with, whether he can denuclearise the Korean Peninsula.
And some people predicted that it would keep on going higher and higher, and some people I still think maybe it will, but on Sunday alone it fell 6%, and by the time this podcast is released, who knows?
Who knows where it will be? And it's not just bitcoin that's suffering. Other commonly traded digital currencies like Ethereum have also taken a dive.
Now, there are profits to be made, of course. Some people go, hehehe, if all this selling's going on, what I'm going to do is I'm going to sell short and bet on the prices to fall.
So some people wonder, well, why is cybersecurity such a big issue to cryptocurrency exchanges and not seen as much of a threat to traditional financial institutions like banks?
And Miek Gohibban, a friend of the show, pointed out in a rather good tweet, I thought, earlier this week that cryptocurrency exchanges are different from banks because they tend to be small companies.
And they're often startups and they've got little or virtually no experience and little maturity in their security team. So why wouldn't they be attacked?
Why wouldn't criminals try and break into them because of the rewards?
And don't forget that if they manage to steal money from a cryptocurrency exchange, that money is anonymous and untrackable, untraceable. So terrific, right?
Once it becomes a more ubiquitous service where banks are actually running crypto services, you're going to lose a lot of the transparency and anonymity that comes with the service.
We're not suggesting people jump on this bandwagon of attacking cryptocurrency exchanges, but we want to give some advice for regular users.
And we've covered this sometimes in past episodes of Smashing Security.
But certainly, if you have a cryptocurrency investment, don't leave your wallet full of bitcoins or Ethereum or whatever it is lying around in an online exchange, because who knows how well they are being secured.
My preference is to have a hardware wallet that stores your private keys. So you're not leaving it somewhere up on the net.
Now, soon as we've gone lavatorial, I think maybe now is a good time to point out that no less a luminary of the security industry, a veteran, than John "Mad" McAfee— do you remember what his proclamation was about the price of bitcoin?
Would have been a sensible No, when it comes to bitcoin, John McAfee has said that if bitcoin has not reached $1 million by the end of 2020, so he's got, what, 18 months or so, he says he will eat his own dick on national TV.
After that, it was called out by whistleblowers for cheating. And after that, the World Anti-Doping Organization got hacked and a lot of information was released from that.
So there's a continuum between sports events, national prestige, and things that go on in cyberspace.
And the situation in Russia is quite fraught generally, because no less a person than Robert Hannigan, former head of GCHQ, last week said that the UK was perhaps at cyber war with Russia.
This is partly to do with tensions around the Skripal poisoning, but also there's other things afoot.
And the UK intel agency and its Western counterparts don't really know what's going on with Russia, what its military doctrine might be.
And that has gone back a few years to an attack on French TV station TV5Monde, which took it off the air for several hours and was initially blamed on the Cyber Caliphate.
Do you remember that?
Codenamed APT28, quite notorious in the world of cyber espionage.
But there we saw a TV station which was actually taken off air effectively by hackers and very public example of the kind of— now I'm not sure why TV5Monde was actually taken off air.
But I think maybe the most memorable thing which happened during that attack was when the journalists from the TV station went on air to explain what was happening.
And they had in the background, stuck on a wall behind them, some of their social media passwords.
Oh yes, we have now sorted these out. We're not going to have any more problems from the hackers.
And of course, their Twitter or Facebook or whatever was at the same time being taken over by hackers who were watching. Just incredible incompetence on their part, but also common.
This is a strain of malware that affects routers.
When it first came out, there was speculation that it might have been put together by the Russians and it might be a prelude to the attack on the Champions League in Kyiv last month between Real Madrid and Liverpool.
Oh, yes.
There was a thought that maybe it would be used to disrupt communications or disrupt energy systems while this very high-profile event was happening in Kiev.
We know it's out there, but we don't know what it's for.
So what sort of cyber attacks do you think we might see which are in relation to the World Cup.
Could these be sort of retaliatory attacks from other countries against Russia, or might we see patriotic Russian hackers attacking Brazil, for instance?
No, let's think really out of the box and let's admit that attribution in cyberspace is difficult. Maybe somebody in Ukraine is playing the long game.
Maybe it was them that have come up with VPN filter and maybe bang, they're about to unleash on Russia. Or maybe it's just something else. We don't really know. It's a mystery.
You know, it's a game of two halves, isn't it, John?
And of course, also be wary of turning mobile data off because they might have a very nasty bill. At the end of things.
Good luck using Telegram, which Russia wants to shut down and block its citizens from using as well.
It's difficult when you go to some countries these days to keep yourself secure, isn't it?
And for more than a year, applicants for concealed weapon permits— this is weapons where you're not wearing them on display, but they're concealed— in the state of Florida were being given the green light without the right background FBI NICS checks.
Let me just let you take that all in for a second.
And basically, this is the background checking system that's used federally by licensed firearm traders.
It came from the 1993 Brady Act that was signed by Clinton, and it requires that everybody who wants to transfer a firearm must do so without violating state and federal laws, right?
So if someone was not of age to have a firearm, or if someone had limited mental capacity, or if someone had a warrant out for their arrest, or someone was a criminal, they would maybe be told, no, you're not allowed to have a firearm in that particular state.
You'd call up and you'd check and say, look, I want to check on this person. It was basically a way to kind of check systems and databases that were out of state.
And of course, now you do it via the internet.
The employee who worked at the Florida Department of Law Enforcement, yes, who was responsible for the NICS checks, forgot her password and then just kind of forgot about the whole database background checking for concealed weapon permit thingy.
So there's a password, there's some form of authentication.
And she decides to look into that. This is your boss.
So she goes and sees the employee, surname Wilde, who was responsible for managing the NICS database since 2013, okay?
So this is three years before the problem actually started occurring.
And Wilde looked, quote, "bewildered." This is from the report. And said, quote, "I had a login issue and never followed up."
So she's trying to get into the system, can't get into the system. 40 days later, raises the issue, saying that she can't get into the NICS database.
There was a bit of back and forth, someone trying to help them gain access to the system, but she seems to kind of got bored with the emails and effectively stopped responding to them.
So they couldn't log in, they raised an issue or a support problem, said, "Oh, by the way, I can't log in" with the NICS people or with tech support.
Tech support came back and said, "Well, you should be able to log in." And she's like, "Well, I can't." And they were like, "Well, have you got caps lock turned on?" "Yeah, I've made sure caps lock isn't turned on.
Don't worry about that." "Well, are you typing it like this?" "Yes, I'm typing that."
And she is quoted as saying in the investigation, "I dropped the ball. I know I did that. I should have been doing it." And no, she did nothing wrong at all.
Everyone can have guns." It's like Oprah. "You've got a gun. You've got a gun. Everyone in the room is getting a gun." Fantastic.
And upon learning of Wilde's negligence, the department immediately completed full background checks on the applications in question, ended up revoking 2,191 of them.
Oh, 80%, about 80% were revoked.
And what makes this whole thing worse for me is that NICS have been maintaining their telephone checking, background checking system during all this, and each call only takes a few minutes for each applicant to be approved or denied.
Just check out this NICS video that explains everything.
FFLs are strongly encouraged to register with eCheck And don't forget, even as a registered eCheck user, you can still use the telephone to reach one of our contracted call centers.
Think about it. On average, the NICS eCheck provides responses to its users in under 2 minutes.
So in the time it took to watch this announcement, you could have received your results. So I don't know what the fuck, man.
I don't know how anyone in the office didn't notice for 13 months either. 13 months.
And if, so it's important that an institution or an organization has clear policies, procedures, and systems in place for people who forget passwords, a button that says, forgot your password, click here and we'll help you.
Or if you forget your password, please contact this person. And build in team redundancies.
How could one person be in charge of all this and there's no one else who's kind of checking in? There's no reporting mechanism. It's very bizarre to me.
Maybe educating employees on actually what they're doing.
She told the Tampa Bay Times that when she was working at the Agricultural Department mailroom, she was suddenly given oversight of the background check database in 2013.
And she says, I didn't understand why I was put in charge of it.
So from her own words, she was put in charge of this thing that she was never really introduced to or explained how it worked or how important or vital it was.
And I'm not trying to excuse her behavior. She should have figured it out.
Let's give it to Martha, who is working in the mailroom. Put her in charge of it.
She should have found some other moron to take over the job and say, oh yeah, try and work out what the password is if you can. Just passing the buck all the time.
Because otherwise passwords do too easily get forgotten, don't they? Or aren't managed properly.
Over a million files are uploaded to VirusTotal every day for analysis and to determine what different antivirus products call them.
But you can do much more than that with VirusTotal Intelligence.
VirusTotal Intelligence helps you get more context about alerts through advanced malware threat hunting behavioural visualization, as well as historical analysis of samples.
Learn more by visiting virustotal.com/learn, and be sure to let VirusTotal know that you heard about them from the Smashing Security podcast. And welcome back.
Can you join us on our favourite time of the show? It's the part of the show that we like to call Pick of the Week.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a website, an app, a podcast, whatever you like. See how I changed that round after last week?
That's good, that's good. It doesn't have to be security-related necessarily.
And you just may find it strange. So basically you can post your question up there and others will vote as to whether what you're describing is normal or not.
And then you won't feel like such a weirdo.
So for instance, is it normal that I let my dog eat popcorn off my tongue? 29% said yes. That was normal. That's perfectly normal.
First of all, imagine, if you will, a situation where you don't have to worry about the phone, you don't have to worry about email, any of that.
Life is just stripped back to good food, wine at the end of the day, and companionship and conversation and walking exercise and with scenery.
It really is. And it's even better after a hard day's walk. So, okay.
They might not be able to download next week's episode.
Get some exercise, get off the net. Yeah, look, in my defense, I've just been to the Infosecurity Show last week, which was cyber to the power of tech.
And when I was asked to come up with a recommendation, I wanted to come up with something that was so opposite of that.
You know how annoying it is when you go to Google and you do a search because you're trying to learn something, especially if you're writing a story, for example, you're trying to do a search on something you don't know a lot about, and it always provides you with a wiki page, a Wikipedia page at the top.
While I admire Wikipedia and what it's trying to do, I think I would be much more comfortable with a well-known fact-checked site.
A site like Encyclopedia Britannica to give me non-Fox News Cliff-style note info on a topic.
So say hello to Britannica Insights extension powered by the folks at Encyclopedia Britannica. So you plug in this little extension.
And every time you do a search, it provides you with Britannica Insights. So for example, I was looking up Brady Law earlier for my story. Smashing Security.
And you can see from my screenshot here, I have a little sidebar with a bit of information on it.
It also gives me the Wikipedia information, but I have a bit more information that I find a bit more trustworthy.
There's many Google users out there.
So specifically designed to work with Google search results, it's going to put up a little extra box giving you the Britannica definition.
Then they're not going to have anything like the number of entries that something like Wikipedia is going to have, obviously.
I'm sure I won't be overlooked again. Well, on that excellent, fascinating— I don't know if that was the best actually, Carole.
I don't know how we can compare a 700-odd mile walk to a plugin for Chrome which displays Encyclopedia Britannica results.
You can buy things in our online store at smashingsecurity.com/store, including t-shirts and stickers and mugs.
And John, if anyone wants to follow you online, where's the best place that they can do that?
Apparently she found a little kitten and it was nuzzling between her, on her sort of unborn tail.




This is yet another reminder that "the cloud" is not your computer. Once you learn to backup a file or image a hard drive, you can and should ditch the cloud services for security reasons. Local storage can be made to be convenient.
Replicating cloud services with your own services and a VPN seems like an untapped market. Perhaps a custom Linux distro to run on your own hardware can be part of the answer.