
The BankBot trojan is targeting hundreds of apps on Google Play as part of a plot to steal Android users’ banking credentials and payment card details.
Securify information security consultant Niels Croese first came across the malware, whose source code went online earlier this year, in an app called Funny Videos 2017. The app appeared legitimate other than the fact that someone had infected it with the trojan probably around 8 April 2017, which was the last time it had received an update. A closer look revealed that as many as 5,000 users had installed the compromised app onto their devices.

Not good!
Croese wanted to get under the hood and analyze the malware, but its developers had used DexProtector to obfuscate its code. The information security consultant was determined, however. He got a sample of the malware that wasn’t as heavily obfuscated, ran a deobfuscation routine, and ended up with the following code:

He then threw this obfuscating code into the Java code and executed the program. Doing so produced a list of all the apps BankBot was targeting. In total, that sample of the trojan had compromised more than 400 apps available for download on Google Play.
Croese reflects on his discovery in a blog post:
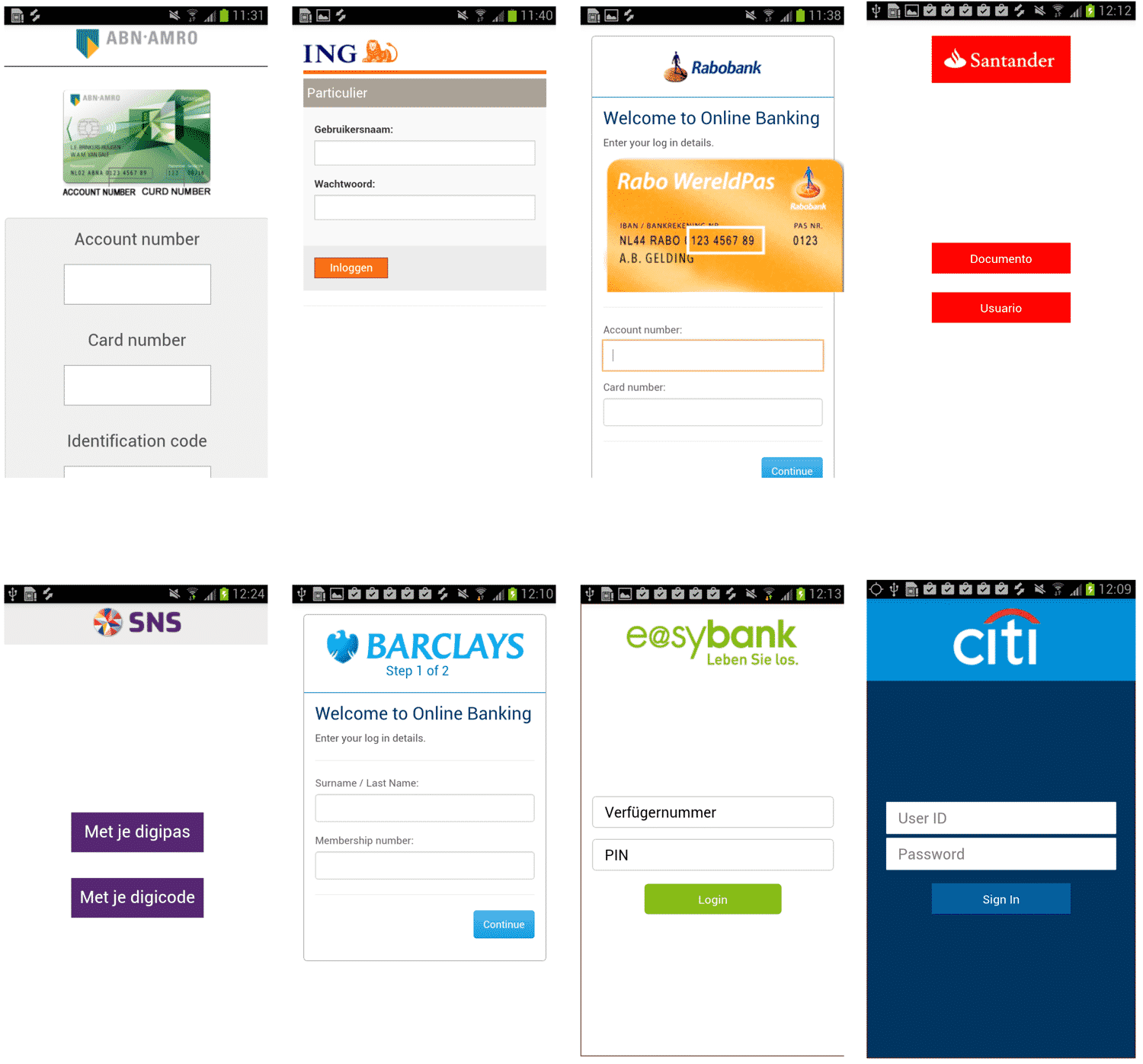
“To our surprise the list was more extensive than expected and for the first time contained some new Dutch targets including ABN, Rabobank, ASN, Regiobank, and Binck… After seeing one of our customers on the target list we decided to update our detection signatures so we can now also detect this sample in our effort to prevent online banking fraud. I guess the game has started once again after some nice and quiet period. So far I have no reason to believe the functionality of the malware is significantly different from the previous samples, but I’ll have a closer look at it.”
For each of the apps it infected, BankBot used phishing overlays to steal users’ banking credentials and payment card details.
Google has since removed Funny Videos 2017 from its Play Store. But even if Google expunges all the compromised apps from its Store, we all know there are other malware families like BankBot out there.
Acknowledging those threats, users should research an app carefully before they install it on their phones. Specifically, they should read the user reviews while staying alert for complaints about unexpected behavior and look at the permissions for unusual requests. They should also install a mobile anti-virus solution on their phones just to be safe.



Malwarebytes is about the only one left who offers a free Android app, without ads. Avast is still a good product, and the ads are not too bad. But, MBAM plays nice without draining any resources.