 The website of AVG, makers of one of the world’s most popular free anti-virus products, appears to have been hacked by a pro-Palestinian group.
The website of AVG, makers of one of the world’s most popular free anti-virus products, appears to have been hacked by a pro-Palestinian group.
Visitors to http://www.avg.com will not be greeted by the normal promotions for anti-malware software but instead be greeted by a patriotic rendition of the Palestinian national anthem (courtesy of an embedded YouTube video) and a message from a group calling itself “KDMS Team”.
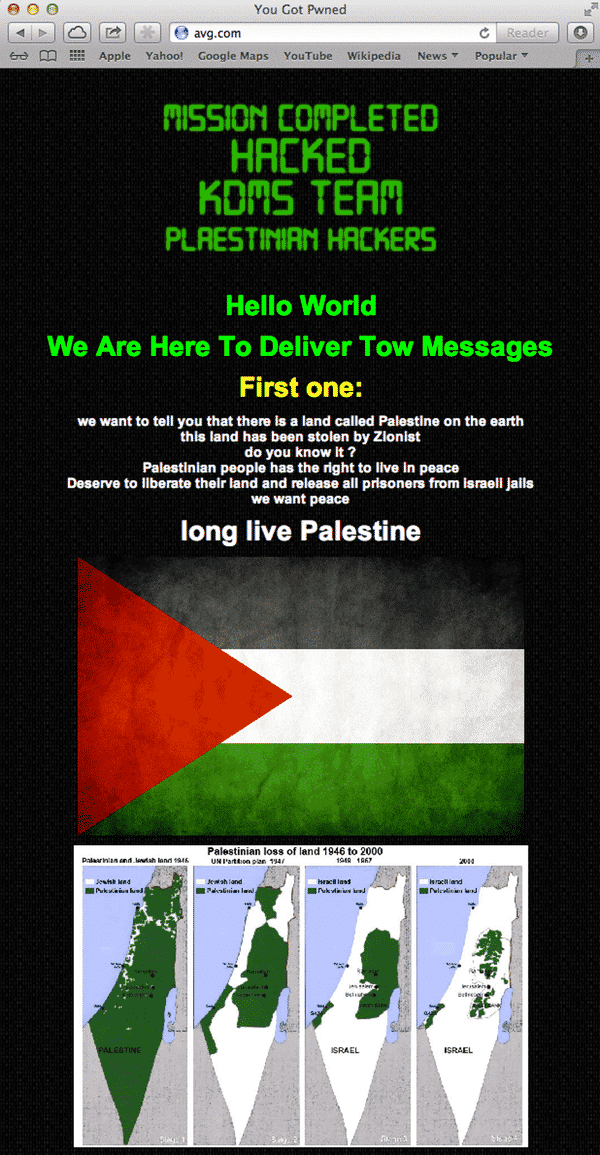
Here is the (not terribly well spelt) message left by the website’s defacers:
MISSION COMPLETED
HACKED
KDMS TEAM
PLAESTINIAN HACKERSHello World
We Are Here To Deliver Tow Messages
First one:
we want to tell you that there is a land called Palestine on the earth
this land has been stolen by Zionist
do you know it ?
Palestinian people has the right to live in peace
Deserve to liberate their land and release all prisoners from israeli jails
we want peacelong live Palestine
Second Message:
There Is No Full Security
We Can Catch You !Hacked by KDMS team
Now .. We Will Quit Hacking
It’s possible that the hackers managed to change the website’s DNS records, redirecting anyone who attempted to visit www.avg.com to a different IP address.
It’s clearly embarrassing for a security company to hit in this fashion by hackers, but there is no indication that any customer information or sensitive data has been compromised.
![]() Update: Another anti-virus company, Avira, has also been hit in what appears to be the same attack.
Update: Another anti-virus company, Avira, has also been hit in what appears to be the same attack.
Softpedia reports that Avira has confirmed that the cause of the disruption was DNS hijacking, and quotes Avira’s Sorin Mustaca as blaming bogus password resets at Network Solutions:
It appears that several websites of Avira as well as other companies have been compromised by a group called KDMS. The websites of Avira have not been hacked, the attack happened at our Internet Service Provider Network Solutions.
It appears that our account used to manage the DNS records registered at Network Solutions has received a fake password-reset request not being initiated by anyone at Avira.
Network Solutions appears to have honored this request and allowed a 3rd party to assume control of our DNS. Using the new credentials the cybercriminals have been able to change the entries to point to their DNS servers. We are working with the ISP to receive control on the domain name and only when we have solved the problem we will restore the access to the Avira services.
At this point we are not aware of any effect to our customers.
DNS records work like a telephone book, converting human-readable website names like avira.com or avg.com into a sequence of numbers understandable by the internet. What seems to have happened is that someone changed the lookup, so when you entered whatsapp.com into your browser you were instead taken to a website that wasn’t under the legitimate company’s control.
The question now is how did the hackers manage to change the DNS records for these sites?
Could it be that cybercriminals managed to guess the passwords used to secure access to the information, and log in as though they were the administrators of the sites’ DNS records?
Or was Network Solutions – which manages the DNS records for these companies – tricked into changing the passwords, and as a result allowed the hackers to gain access to the DNS entries?
Hopefully the AVG and Avira teams will be able to resolve this issue quickly, and normal service will be resumed.
See also: WhatsApp homepage defaced by hackers, goes offline
Update 2:
AVG has now also been in touch, with its official statement on the issue:
AVG can confirm today that it has had a select number of online properties defaced as a result of our domain name system (DNS) registrar being compromised. A number of other companies appear to have been faced with the similar issue. The situation is being further monitored and assessed closely. Customers are our priority, the DNS records have been corrected and AVG is working hard to resume normal service levels to its customer base and continue to protect our customers and their privacy.



It would actually appear as though its a DNS poison attack narrowed down to only Google's DNS servers. When using a provider like OpenDNS you go straight to the AVG website.
I think Guy is right – it's all good here via
Virgin Media DNS,,,
avira website too…now!
As previously thought, its a DNS related attack meaning none of the defaced site owners have had their own servers compromised;
"A number of security experts have pointed out that all compromised sites share a common domain registrar – Network Solutions – which indicates the Kdms Team hackers compromised this network rather than the individual company websites."
Source: http://www.ibtimes.co.uk/articles/512269/20131008/kdms-team-pro-palistinian-hackers-whatsapp-avg.htm
Guy .. Thanks for good explanation. when you move a website to a different domain then the DNS servers across the world don't update instantly … it takes varying times to propagate … Hence 2 different people can be possibly viewing content on 2 different servers my guess
Show us a map of Palestine before WW-II. I doubt
you'll find one.
How about one published in 1915?
http://en.wikipedia.org/wiki/File:Palestine_1020BC_Smith_1915.jpg
This could have been worse; If this was done on a site that has logins, they could've made a believable start page that stole info. The advice to check the URL Sophos had given would be done and it'd look like you were in the site, so unless the person looked for a slight difference from what they're used to seeing, they'd go through with it and have their info stolen.