
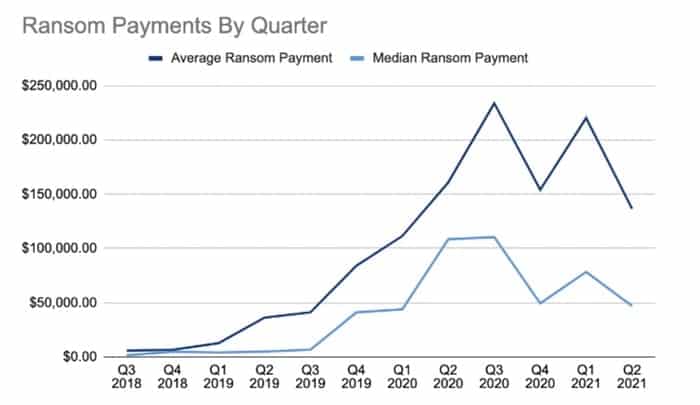
The latest research by Coveware shows that ransomware attackers are attempting to extort, on average, a smaller amount of money through their criminal activities.
According to the firm, the average payment following an enterprise ransomware attack has fallen 38% since the first quarter of 2021 to $136,576 with a median down 40% to $47,008.
That’s obviously a much larger figure than any consumer is likely to be required to pay after their home PC has been encrypted by a ransomware attack, and underlines that ransoms vary depending on who has been hit and how many computers have been compromised.
According to the experts at Coveware, the drop in the average ransom may actually be due to the increasing number of attacks done by Ransomware-As-A-Service (RAAS) affiliates:
“The decrease was primarily driven by a growing number of disparate Ransomware-as-a-Service brands that have proliferated recently, and which have diluted the concentration of attacks controlled by just a few. The lower prevalence of several groups that have historically made some of the highest demands (such as Ryuk and Clop) allowed the average and median ransom payment to drift lower during the quarter.”
In short, the average has gone down because more ransomware attacks are taking place, orchestrated by more criminals. I find it hard to view that as good news.
Here is the top 10 chart of most common ransomware variants seen at enterprises in Q2 2021, according to Coveware:

To add to corporate headaches, Coveware says that it has seen an increase in the proportion of ransomware attacks which include a threat to leak exfiltrated data (81%, a rise of 5% over Q1 2021.)


