At the end of last week, researchers at Kaspersky Lab announced to the media that they had identified a new trojan targeting Android smartphones, disguised as a Tic Tac Toe (also known as “Noughts and crosses”) game.
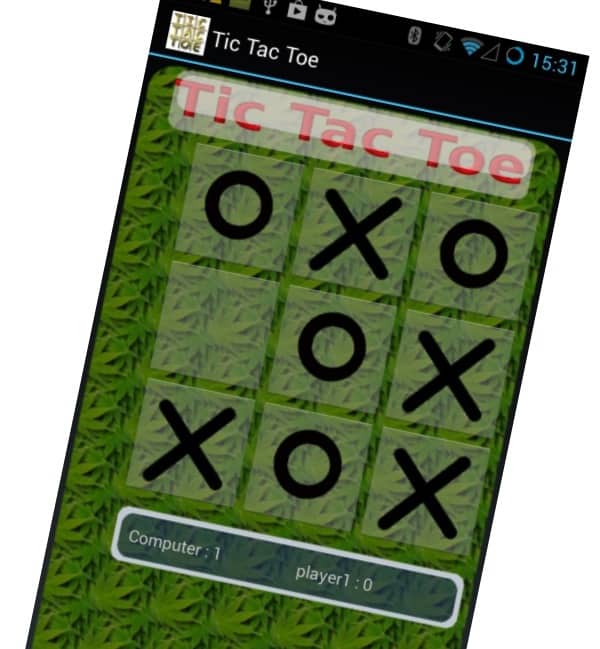
According to the Russian security firm, the Gomal Trojan hid behind the disguise of a seemingly harmless game to steal information from home and corporate users:
Gomal has all the usual spyware functionality. It can record sounds, process calls and steal SMS. In addition it possesses mechanisms that provide access to various Linux services, attacking the operating system on which Android is based. In particular, the Trojan can read the process memory, jeopardizing many communication applications. For example, it can steal emails from Good for Enterprise. That application is positioned as a secure email client for corporate use, so data theft here could mean serious problems for the company where the device owner works.
Sounds nasty, right?
Perhaps, like me, you would be interested in hearing who created this particular spyware game.
Well, hold onto your seats – because I can reveal that the creators are none other than… an anti-virus company!
 Yes, mobile anti-malware firm Lacoon Mobile Security has issued a statement that not only claims authorship of the spying code, but also says that the “new mobile Trojan” uncovered by Kaspersky is in fact a proof-of-concept app that it originally presented at BlackHat 2013 and RSA 2014.
Yes, mobile anti-malware firm Lacoon Mobile Security has issued a statement that not only claims authorship of the spying code, but also says that the “new mobile Trojan” uncovered by Kaspersky is in fact a proof-of-concept app that it originally presented at BlackHat 2013 and RSA 2014.
Indeed, I understand that the app’s code contains strings and URLs related to Lacoon Mobile Security, and examination of data sent by the app shows that it is passed to a domain belonging to the security firm.
Quite why Kaspersky’s research team didn’t spot that during their investigation that is unclear.
But perhaps most worrying is how did Kaspersky’s researchers get hold of the sample?
Lacoon claims that the spyware Tic Tac Toe game, which exploits a memory access vulnerability (CVE-2012-6422) patched by Samsung on its Exynos chips more than 18 months ago, has never been freely distributed:
This supposed malware is also not publicly available or ‘in the wild’ for hackers to use but has only been deployed in test environments.
But Kaspersky’s technical analysis says it was sent to its research team for analysis.
If someone malicious were to get their hands on Lacoon’s proof-of-concept spyware code, there is always the danger that it could be weaponised further and used for something more serious than a presentation at a security conference.
And maybe it would be smarter if firms building proof-of-concept spyware code for demonstrations in future ensured that there was a big fat message displayed at the beginning saying “This is PoC code, created by Lacoon Mobile Security. Contact us if you have any questions about it”.
I’m sure the presentation would still be effective, even if there was a message displayed explaining the code’s provenance.


Re:"And maybe it would be smarter if firms building proof-of-concept spyware code for demonstrations in future ensured that there was a big fat message displayed at the beginning saying “This is PoC code, created by Lacoon Mobile Security. Contact us if you have any questions about it”."
Even better would be to add to the above what used to be commonplace among hackers (i.e., those who were actually ethical and still very skilled because it was a different scene then, entirely):
Modify it slightly so it does not actually function unless you know what to do to change it to work (i.e., it is broken as released and if it is for learning how something works or indeed a proof of concept, then there is no need for it to not have this). And/or do what some have done with other PoC code – encrypt it (even if quite weak encryption, weak as in XOR). Or what about protecting it in the first place, i.e., not make it public, ever, never copying it to a system or disk that could be connected directly or indirectly to a network. Or…list goes on. I'll ignore some other issues in the context of this proof.
As for Kaspersky: indeed interesting they didn't detect that string especially if it was plaintext. And since they believe (ahem…) that we shouldn't worry about what others know about us, maybe we should question them about it, relentlessly. Then again, better is to leave that to them as the suggestion is absurd.
Thanks as always for the comment Coyote.
For what it's worth, my understanding is that Lacoon did XOR the exploit code as you suggested.
It's looking like the Tic Tac Toe game ended up in Kaspersky's hands because someone at Lacoon uploaded it to VirusTotal back in April (https://www.virustotal.com/en/file/d12d4ed427c7fa4c75a8ddc94bda8f1f1f0041e2874724efa6f1b17cd0f340be/analysis/)
Perhaps the Lacoon researcher didn't realise the sample would then be automatically shared with other security vendors?
Although why it then took Kaspersky six months to analyse the code is a question best left to others.
Quite welcome and thanks for the appreciation and your website (as well as the extra information here) – is quite enjoyable and definitely good reading material (no one will hear every single flaw around and many that do will not understand all implications).
Interesting that they did indeed XOR it. Still, I have to question if they truly needed to have it work as is at least if they uploaded it anywhere. I can understand if they did it to test and then not upload it but it does seem irresponsible and rather ironic that an anti-virus company would release code with viral capabilities (I can understand the research, the experimenting, the fascination, but why does an anti-virus company need or want to upload any type of malware somewhere?). Actually, reading it again, it is worse in some ways because it has spyware traits (maybe it isn't viral at all ?). That is even more helpful to attackers (and isn't exactly nicer for the unsuspecting user). I don't see why they needed to show this at all. We all know that computers, phones, any device really, are not 100% secure (and cannot ever be) and trojan horses are old. With the nature of trojans, they can carry any number of things. Spyware being old too makes one question it.
To be fair, and I think this is the most important bit, I could see how I might not have the full story (and I didn't check – for example – Kasperky's site or even their site). In the end, however, humans are not perfect and we all make mistakes. Some mistakes are embarrassing, some are simple, some are complex but they're still a mistake. Mistakes could even be deliberate actions but done for the wrong choice/reason. One can only hope it isn't done again although I don't think this is exactly new or surprising. Indeed, it could be much worse. I'm reminded of CIH and how vendors shipped computers with it (and I seem to remember that security software was hit by it too). Hopefully no one else got their hands on this bug.
As for Kaspersky, I think your suggested answer is indeed the best – there is no good answer, probably not even from them.