Irfan Asrar is a security researcher focusing on threats targeting embedded and mobile devices.
In this article he explores how hackers attempted to infect the Android devices of users protesting against a Saudi Arabian ban on women drivers.
It’s a region of the world where the penalty for hacking a website is less than the penalty for female found defying the ban on driving a vehicle.
So it probably shouldn’t come as any surprise that the website for the Oct 26th Driving Campaign – a grass roots movement that is fighting for the right for woman to drive in Saudi Arabia – came under repeated attacks from hackers wanting to keep the ban in place.

Hacked by ..:: G6RaaT Hacker ::.. Freedom for – KSA –
Additional attempts to derail the movement are now coming to light. Hackers were clearly not satisfied just with the act of defacing websites, and have also distributed malware for Android devices.
The malware, dubbed Android/Hackdrive, was disguised as an Android app in support of the online campaign, and even used the icon that has come to symbolize the movement of the Oct 26th Driving Campaign.
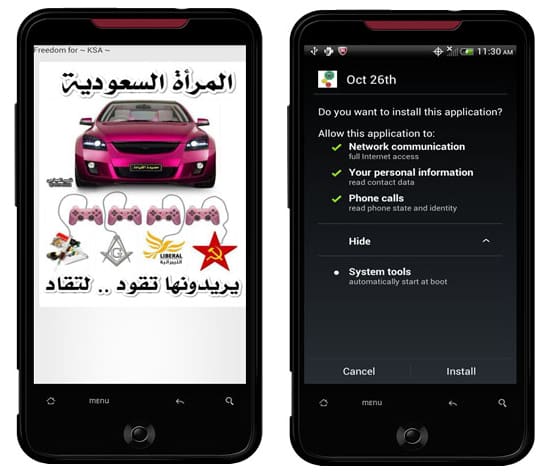
In reality, however, the app was designed to spread the same hate propaganda that was placed on the hacked/defaced websites it was being distributed from.
After it has been installed, the malware activates once a headset has been plugged in.
 Firstly, audio is jammed by the app repeatedly playing the audio from the YouTube video hit “No woman, no drive”, making it impossible to listen to anything else on the device or carry out a phone conversation.
Firstly, audio is jammed by the app repeatedly playing the audio from the YouTube video hit “No woman, no drive”, making it impossible to listen to anything else on the device or carry out a phone conversation.
Additionally, a message in Arabic text is displayed similar to the defacement messages used on the hacked website.
Curiously enough there were signs of additional functionality built into the malicious code.
For instance, the malware has the capability to scour through your contact database, harvesting names and phone numbers from infected Android devices, and send the stolen data to a remote website.
Strangely, although the code is there, the app does not actually it. Could this be a work in progress? Will later versions of the malware contain this additional functionality? We shall have to wait and see.
On the surface the antics used in the app and the website defacing may seem juvenile. But make no mistake, this is hate and prejudice manifested into an Android app.