
Researchers have uncovered an advanced modular backdoor that is capable of logging victims’ Skype calls and copying files off removable drives.
On Thursday, Josh Grunzweig and Jen Miller-Osborn, two malware researchers at Palo Alto Networks, published an article on their company’s blog in which they explore the multi-stage execution process of T9000, a next-gen version of the Plat1 T5000 malware family.
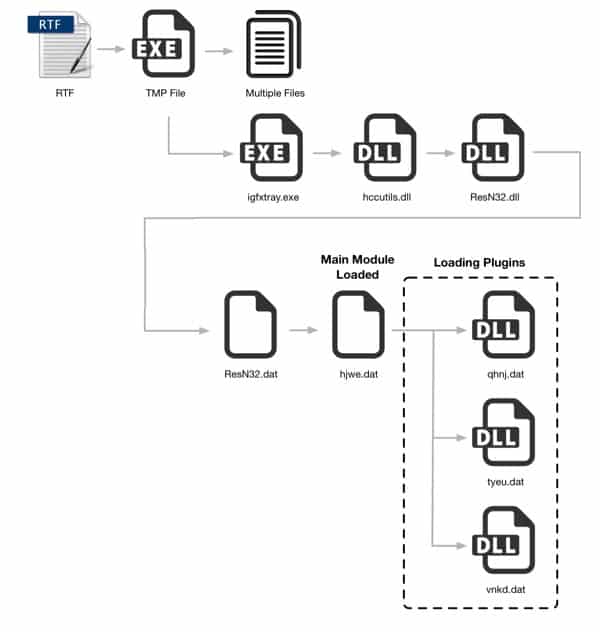
The initial exploitation occurs when a victim clicks on an .RTF file that is attached to a spear-phishing email message. That file exploits two Microsoft Office vulnerabilities, CVE-2012-1856 and CVE-2015-1641, in order to create a shellcode that loads the embedded malware payload and saves it to a temporary file.
Once that temporary file is executed, the malware proceeds along an additional four stages by which it completes its setup.
In order to ensure that the infection process runs smoothly on each victim’s computer, each stage begins by verifying whether any security products are running on the victim’s machine. These include McAfee, Kaspersky, Trend Micro, and close to 20 others:
- Sophos
- INCAInternet
- DoctorWeb
- Baidu
- Comodo
- TrustPortAntivirus
- GData
- AVG
- BitDefender
- VirusChaser
- McAfee
- Panda
- Trend Micro
- Kingsoft
- Norton
- Micropoint
- Filseclab
- AhnLab
- JiangMin
- Tencent
- Avira
- Kaspersky
- Rising
- 360
Stage 1 involves the malware dropping a number of files to the %APPDATA%Intel directory. One of those files, a legitimate Microsoft Windows executable known as “igfxtray.exe”, loads the ResN32.dll library in Stage 2, which then decrypts another file in the next stage. The process concludes with Stage 4, when the malware decrypts and decompresses the malware’s three main plugin files before exfiltrating several bits of information, including the MAC address, IP address, and username.
The first plugin, known as tyeu.dat, is the one that Skype users need to look out for. If a user is signed in to Skype, the malware uses social engineering in an attempt to force the user into granting the process access to the Skype API, according to the researchers.

“The victim must explicitly allow the malware to access Skype for this particular functionality to work. However, since a legitimate process is requesting access, the user may find him- or herself allowing this access without realizing what is actually happening. Once enabled, the malware will record video calls, audio calls, and chat messages.”
The second plugin, vnkd.dat, scans removable drives and makes copies of common Office files like .DOC, .PPT, and .XLS, which it then encrypts and stores for later use.
Finally, the qhnj.dat plugin allows an attacker to monitor file changes that occur on the system and to collect sensitive encrypted data sent to and from the victim machine.
“This last plugin allows the attackers to record important actions taken by the victim, which in turn may allow them to gain additional access as well as insight into the victim’s actions.”
Thus far, the malware has been spotted targeting various organizations in the United States. However, given its multi-stage structure, including the lengths to which it goes to verify that security products are not intruding upon its infection process, the researchers feel that the malware could target a much broader range of users. For that reason, they have provided the malware’s indicators of compromise with the hope that organizations will use them to protect themselves against the tool.
Please view the original blog post here to view these indicators of compromise for yourself.
Update: A Microsoft spokesperson has been in touch since this article was published with the following statement:
“To further protect our customers, we’ve added detection for the malicious software known as ‘T9000’ to Windows Defender. Customers that have installed security updates released in 2012 (MS12-060) and 2014 (MS14-033), either manually or by enabling automatic updates, will already be protected. Our recommendation is to enable automatic updates, which installs the latest security protections, and use the latest version of Skype.”

