
Criminals have updated the AbbadonPOS malware with the ability to search for known point-of-sale (PoS) processes, in its hunt for consumers’ credit card data.
First discovered by Proofpoint’s security researchers last fall, AbbadonPOS is a form of PoS malware that scans all processes except itself for credit card data and then sends that information back to its handlers via a command-and-control server.
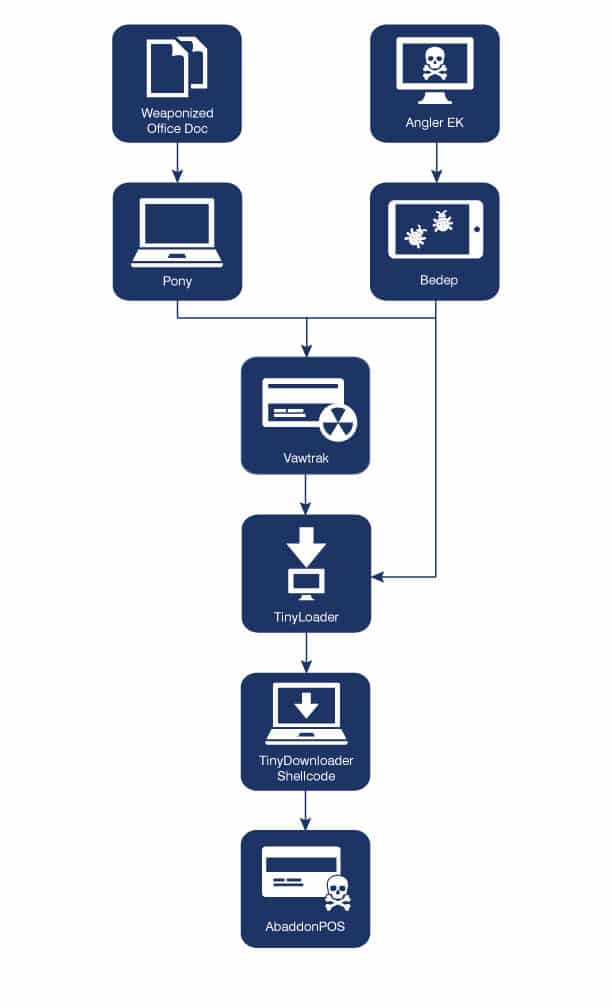
The first sample of AbbadonPOS malware observed in the wild was installed by Vawtrak, a banking trojan known for leveraging malicious Microsoft Office documents to prey upon customers of Bank of America, CitiBank, and other well known financial institutions.
In addition to Vawtrak, the PoS malware has been known to leverage the notorious Angler exploit kit and Bedep malware for delivery.
At the end of the day, however, all roads lead to TinyLoader, a malicious downloader that is ultimately responsible for installing AbaddonPOS onto a victim’s machine.
AbbadonPOS and TinyLoader. TinyLoader and AbbadonPOS. Friends ever-working towards criminal ends, including in their decision to make some modifications.
Indeed, according to a blog post published by Proofpoint, both malware samples have been observed in a new spam campaign sporting a few upgrades.
The campaign begins with a spear-phishing email that includes the recipient’s name and the company’s name in its body
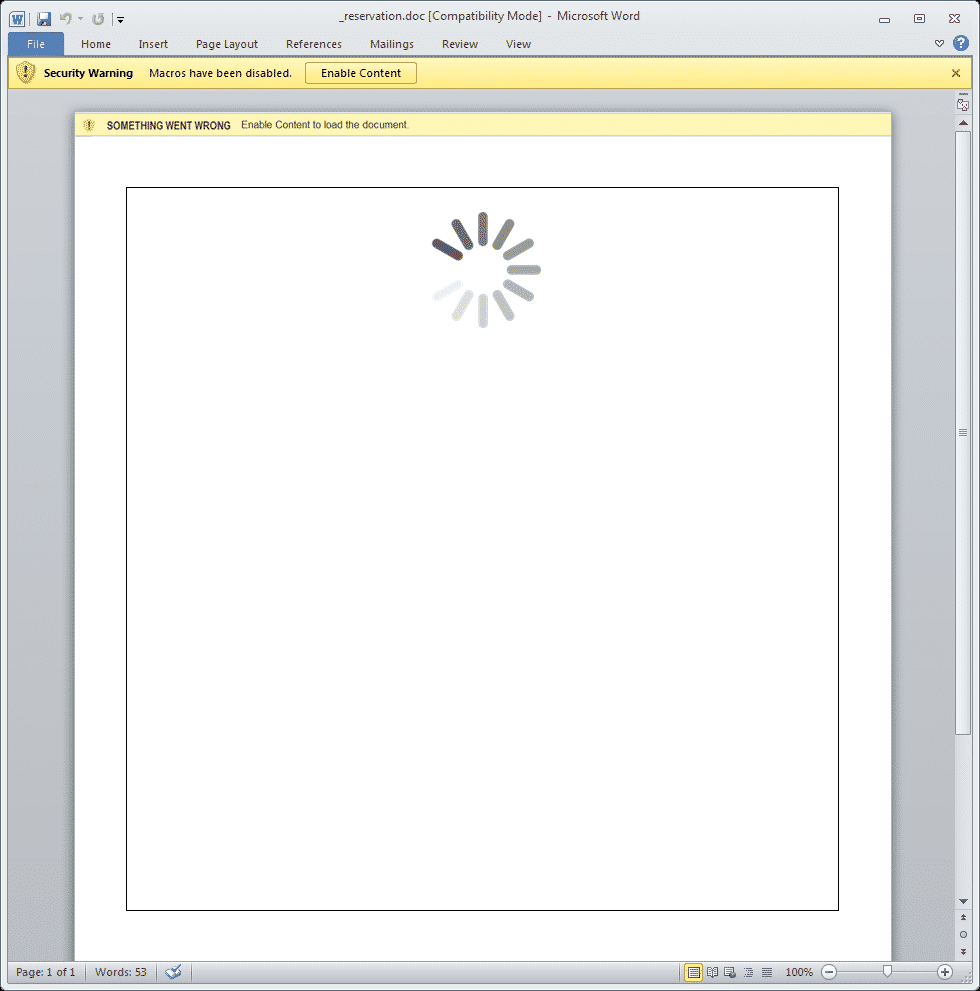
The email also comes with a malicious attachment that, when clicked, uses the image of a spinner displayed in a malicious Word document to lure the recipient into clicking on the “Enable content” button. Doing so will install TinyLoader onto the recipient’s computer.
As Proofpoint explains, TinyLoader now comes with a 4-byte XOR layer of obfuscation over the shellcode that is received from the command-and-control (C&C) server:
“The XOR key is dynamically generated by the C&C and is different in every session. Once the shellcode is decoded, execution is immediately passed to the decoded shellcode. Although the controllers of TinyLoader could theoretically perform any action through custom shellcode, we are still observing this family of malware being used as a downloader.”
Ultimately, TinyLoader loads up another TinyLoader payload, which then installs AbbadonPOS onto the victim’s machine.
A few minor changes have been made to AbbadonPOS. For example, it no longer stores the IP address in an ASCII string, and its hardcoded XOR key has been revised.
The big upgrade, however, comes in the form of two parts: code to check deny-listed processes (or processes that wouldn’t otherwise be checked) for credit card data, and an allow-listed process list to scan for common PoS process names.

Interestingly, the deny-list code is not in any way connected to the allow-listed process list. That could be a mistake, as that means the deny-list code will always scan all processes for PoS data regardless of whether their name appears on the allow-listed process list.
For its part, Proofpoint feels this is a temporary error in a malware sample that is being continuously updated by bad actors:
“TinyLoader and AbbadonPOS are under active development. We expect both to continue to appear in email attacks as cybercriminals target point-of-sale systems to harvest credit card data. Despite changes in the credit-card landscape and more stringent PCI DSS compliance requirements, credit card-related cybercrime remains profitable for threat actors when it can be conducted at scale. Comprehensive email, network, and endpoint protection–along with user education–remain the best ways to protect systems and customer data.”
AbbadonPOS and TinyLoader are for the most part spread via the Angler exploit kit and malicious Microsoft Office documents.
With that in mind, ordinary users can protect themselves against this threat duo by disabling macros by default, implementing security and software updates as soon as they become available, and never clicking on suspicious links or email attachments.


