 Back in 1995, the anti-virus world took a sharp intake of breath as it realised that malware wasn’t just limited to boot sectors, EXE and COM files.
Back in 1995, the anti-virus world took a sharp intake of breath as it realised that malware wasn’t just limited to boot sectors, EXE and COM files.
The Concept virus, accidentally shipped by Microsoft on CD ROM around the world, rapidly became the most widespread malware ever – and it infected Microsoft Word documents, via its embedded macro language.
Macro viruses spread more quickly and insidiously than conventional malware, for the simple reason that people were much more likely to share documents and spreadsheets with their colleagues than executable files or floppy disks.
As interconnectivity increased and email became a regular fixture of the workplace, it wasn’t at all uncommon to see a vast amount of macro-based malware spreading across email systems.
Twenty years on, you might have imagined that macro malware would have been assigned to the dustbin of history. But sadly, it’s seeing something of a resurgence.
Researchers at Trend Micro, for instance, are reporting attacks designed to spread the Vawtrak banking malware distributed via spammed-out Word documents containing malicious macros.
The emails typically pretend to come from the FedEx delivery service or American Airlines, but clearly the possible disguises that the attackers could use to disguise their emails are limitless.
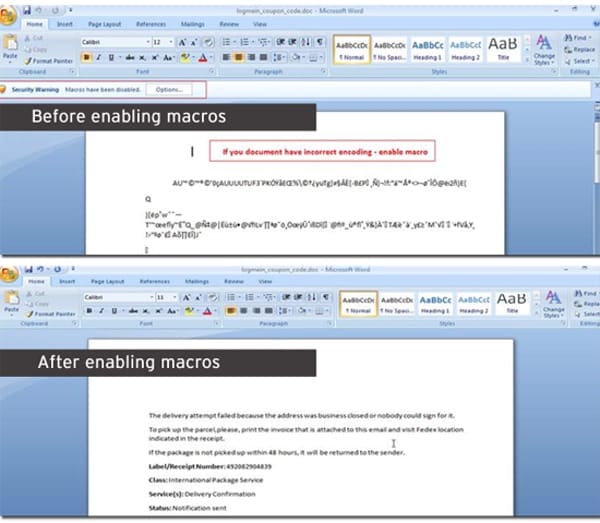
The danger comes if you open the attached Word document. Although Microsoft learnt years ago to disable the automatic running of macros by default (thank goodness), the attack uses social engineering to trick users into enabling the facility which will then allow the malware to begin its attack.
According to Trend Micro, the documents do this by appearing as a jumble of random characters with advice to enable macros to view the message. If you already have macros enabled, the advice is not displayed.
Enabling macros is obviously a very bad idea. Before you know it, a batch file, .VBS file and PowerShell script will be dropped onto your computer. When the batch file runs it will execute the other files and download a version of the Vawtrak banking trojan onto your computer.
That’s pretty bad news if you’re a customer of some of the banks targeted by the Trojan horse, including Bank of America, Barclays, Citibank, HSBC, Lloyds, and J.P. Morgan.
Martijn Grooten of Virus Bulletin has also written about the rise of macro malware, and was able to find a sample of a malicious Word document intended to start a Vawtrak infection in his spam traps:

Once again, online criminals are exploiting a human weakness to get a toehold onto computers. Keep your wits about you, and always be suspicious of unsolicited emails and unexpected attachments – even if they do appear to be a “harmless” Word document.
More details of the Vawtrak malware threat can be found on the Trend Micro blog.


"Back in 1995, the anti-virus world took a sharp intake of breath as it realised that malware wasn't just limited to boot sectors, EXE and COM files."
I was thinking similar when seeing the title of (this) post. But then I don't remember Concept. Actually, the very first thought I had when seeing the title, was the Wazzu virus but then I wasn't sure if I was remembering right, and that it was indeed a macro virus (it seems it was indeed). But that came in 1996, apparently.
"Macro viruses spread more quickly and insidiously than conventional malware, for the simple reason that people were much more likely to share documents and spreadsheets with their colleagues than executable files or floppy disks."
True. Also that VB is far easier for the average person, than assembly (it is just that it mutilates the mind to the point of it being impossible to teach real programming, at least according to a quote attributed [whether misattributed or not I don't know] to Dijkstra (but that was regular BASIC and this is arguably worse)).
"Twenty years on, you might have imagined that macro malware would have been assigned to the dustbin of history. But sadly, it's seeing something of a resurgence."
… and here it is: as you correctly pointed out, the art of computer viruses (figurative and literal meaning of art) is mostly gone.. sure, some would argue it is because of more malicious uses (fraud, theft, etc.) but at the same time it is also easier (including to spread; an MBR/BS infector hardly used social engineering… after all, yet that is often how it is done now). Looking at it another way, we could call it what AVPVE categorises some viruses in (this in the algorithm features: student's i.e. extremely primitive viruses, often poorly debugged.
(I'll just add that while some malware of today isn't so primitive it still can be stated that the viruses of old, particularly those in assembly, took far better programmers).