
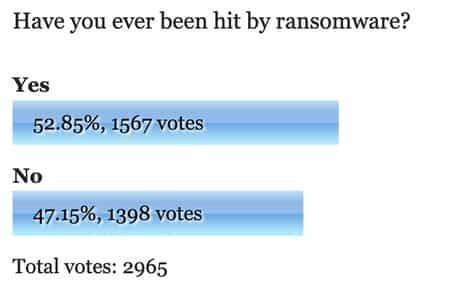
Researchers have uncovered a new type of ransomware that trashes victims’ Windows system and demands 13 Bitcoins in payment – one of the largest malware-based ransoms seen to date.
Lawrence Abrams of Bleeping Computer explains how the ransomware, which has been dubbed “7ev3n”, encrypts .DOC, .JPG, .PDF, and other common file types according to a unique process:
“When a computer is infected, the ransomware will scan all of the drive letters that match certain file extensions and when it finds a match rename them into numbered sequences of files with the .R5A extension. For example, if a folder contains 25 data files, the ransomware will encrypt and rename all the files to 1.R5A, 2.R5A, 3.R5A … 25.R5A.”
Once the ransomware has successfully infected a victim’s files, it displays a ransom message that demands 13 Bitcoins (approximately $5,100 USD). This note includes a Bitcoin address where ransom payments should be submitted:

As if paying thousands of dollars in ransom weren’t bad enough, 7ev3n also installs a number of files to the %LocalAppData% folder. These include %LocalAppData%system.exe, which is the main executable of the ransomware; %LocalAppData%del.bat, which removes the ransomware’s installer; and %LocalAppData%time.e, which contains a timestamp of when the infection began.
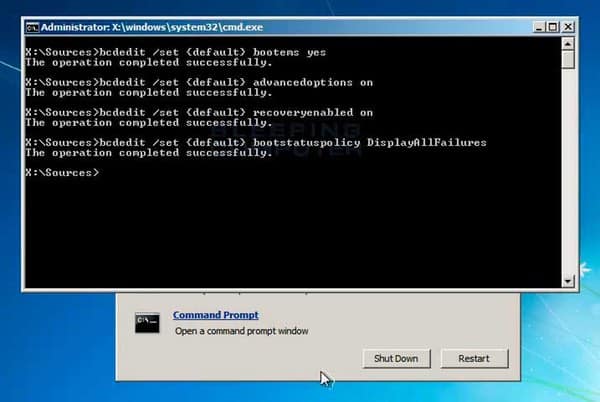
The destructiveness of these files pales in comparison to that of %LocalAppData%bcd.bat, however. Included in that particular install are several BCDEDIT commands which disable a number of critical Windows recovery options, including the Windows Emergency Management System, the Boot Options Editor, and Startup Repair.

“Now that 7ev3n has effectively locked you out of any recovery options, it will also add a registry entry that disables keys commonly used to troubleshoot Windows such as Alt+Tab, Task Manager and the Run dialog. It does this by adding a special registry value that disables the F1, F10, F3, F4, Enter, Escape, Left Alt, Left Ctrl, Left Windows, Num Lock, Right Alt, Right Ctrl, Right Shift, Right Windows, and Tab keys.”
Clearly, this particular ransomware is not to be trifled with.
At this time, there is no way for a victim to recover their files without paying the ransom unless they have a backup.
Even after victims regain control of their computer, they must invest some time in resetting the damage caused by the ransomware. This involves the use of a Windows installation disc to reactivate the recovery options originally disabled by 7ev3n. Once this is complete, a user can then enter into Safe Mode and remove all of the files installed by the ransomware. Installing a reputable anti=virus program and letting it run on your computer should clean up the rest.
Clearly, not only are ransomware authors upping the ante with regards to their ransom demands. They are also designing their malware to leave a lasting impact on their victims’ machines.
With this in mind, users need to protect themselves by implementing regular software updates, maintaining an updated antivirus solution on their computers, and backing up their data often. These small steps could help save you thousands of dollars and a lot of time spent restoring your PC to a workable state.



Worth mentioning that backing up to an external drive, network drive etc, is no good, IF YOU LEAVE THE DISK CONNECTED. Those files will be encrypted too …
I have a friend who was caught out by this. Ouch.
Yes. Offline backups for the win!
Most PCs come without installation disks. How do you get one without paying hundreds of pounds for a new license ?
You actually should be making your own install disk when you first boot up, Most new PC's ask you to creat them the first time you use the computer.
Jim I was just about to ask, I store all files on a NAS drive so my PC only has the OS and application files installed so obviously any ransomware would have access to this drive too if connected. So it looks like on line storage or back to good old USB or DVD storage :-( I don't like the risks with either particularly
I have a 2 drive NAS but own 3 drives. I change one on Sat mornings so at worse I only lose a week of stuff which would not be much here at home. I would hate to lose the Tb's of music I've been collecting since the Plextor 12-20 came out(I'm showing my age here lol )….
And don't forget a strategy of security awareness training to avoid infections in the first place.
If you get this DON'T do as the article suggests and do a repair.
Format your HDD and reinstall from scratch.
If you've got this, you are very likely to have some other dodgy stuff on our system.
This makes you want to really vet any new executable file the PC is trying to get you to run. I assume that is the only way this ransomware can get onto your PC. I must admit, I was really surprised at how easy it is to run bcdedit – Windows should have locked this down with all sorts of unbypassable onscreen prompts.
I would never "clean" an installation after an infection as serious as that, spend money on a new harddrive and reinstall.
Really? Buy a new hard drive? That is a ridiculous response. Just wipe the drive and reinstall from scratch. Done. No need to buy new hardware.
Here is a date which should worry you: July 29th 2016. This is the date Microsoft will start charging for Windows 10. Here is another date which should worry you more: July 17th, 2017. Why? Because it just made July 29th, 2016 one heck of a lot worse…
http://www.forbes.com/sites/gordonkelly/2016/01/27/when-free-windows-10-becomes-expensive-fear-this/?utm_campaign=yahootix&partner=yahootix#1c1f186c538d
Microsoft's new web browser reportedly tracks the websites you visit — even when you ask it not to
http://www.businessinsider.com/microsofts-private-mode-still-stores-websites-2016-1?r=UK&IR=T
Learn that Apple, Google & M$ are NOT the only computer/mobile operating systems in the world. There are other operating systems that are Free, Faster, Stable, Secure, Superior & far more advance, They are up2date, January 2016, Below
http://emmabuntus.sourceforge.net/
http://linuxmint.com/download.php/
http://zorin-os.com/free.html
Linux is not fast by any means of the word. It's a complete dog in fact. Kinda reminds me of some people I met that we running Vista and insisted on using AOL.
for all the time and effort as well as money to recover, you might as well just dump that pc in a lake somewhere and buy a new one. you're welcome