
The latest member of a notorious family of Android trojans downloads and launches malicious apps without the user’s knowledge on infected devices, according to researchers at Russian anti-virus firm Dr Web.
The malware, known as “Android.Xiny.60,” hails from the same family as Android.Xiny.19.origin, which made its grand entrance back in January 2016.
At the time, Xiny hid itself in over 60 games available for download from the official Google Play store, and used instructions relayed to it in the form of image files modified via steganography to run arbitrary APK files.

As Softpedia reports, the latest versions of the Xiny trojan don’t need to trick users into granting it admin privilges, but instead deploy exploits to root the device.
Once the malware launches, it loads up its malicious components and saves them to the system directories. The trojan can use those elements to wreak all kinds of trouble.
For instance, Xiny can inject malicious processes into IM chat apps, snooping on conversations and even sending messages without the user’s permission. Furthermore, the malware targets banking apps, and can display fake login pages to steal usernames and passwords.
As Dr Web explains in a blog post:
“The trojan launches the igpi module (Android.Xiny.61) which uses the ptrace function to inject the igpld.so executable Linux library (Android.Xiny.62) into the system processes of Google Play (com.android.vending) and Google Play Services (com.google.android.gms, co.google.android.gms.persistent) applications.”
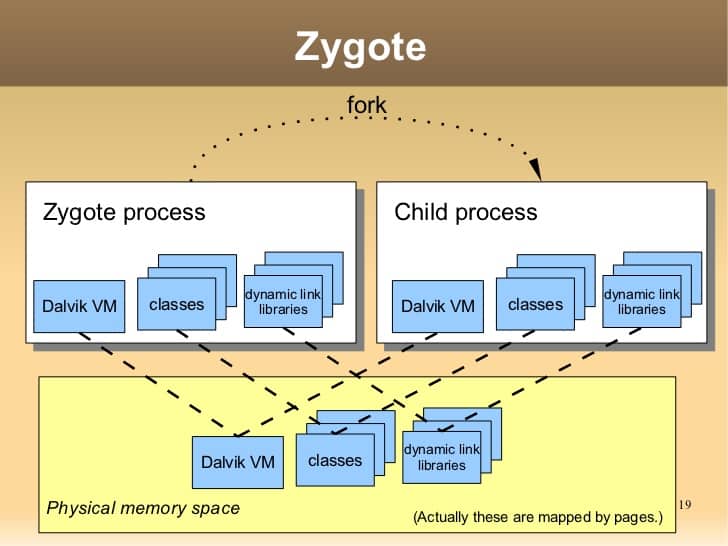
The malware can also inject Android.Xiny.62 into the zygote, a crucial Android process whose infection allows the trojan to launch new applications and additional malware.
All the while, Android.Xiny.60 waits for a charger to be detected, the home screen to turn on or off, or several other specific events to occur. Whenever one of those events takes place, the trojan connects back to its command-and-control server and sends all kinds of information about the device to home base.
Android users should work to protect themselves against all versions of the Android.Xiny malware by maintaining an up-to-date anti-virus solution, reading the reviews of apps before they install them, and checking to make sure an app’s requested permissions jives with its advertised purpose.
Few if any legitimate apps actually require root privileges, so beware of imposters looking for rights they don’t deserve.



This is what has happened to to me. I've been tormented by hackers controlling and violating me for 3 years. No matter what I do, I can't stop them. Please advise