
There’s an amusing story by Simon Sharwood in The Register today.
Apparently when Cisco shipped its Unified Computing System (UCS) boxes between November 17, 2015 and January 6, 2016 it made a configuration error.
You see, when you try to set them up you won’t be able to access them with the default admin password of – wait for it – “password”. Instead, for reasons best known to Cisco they changed the default password to the marginally less insecure (but not documented) “Cisco1234”.
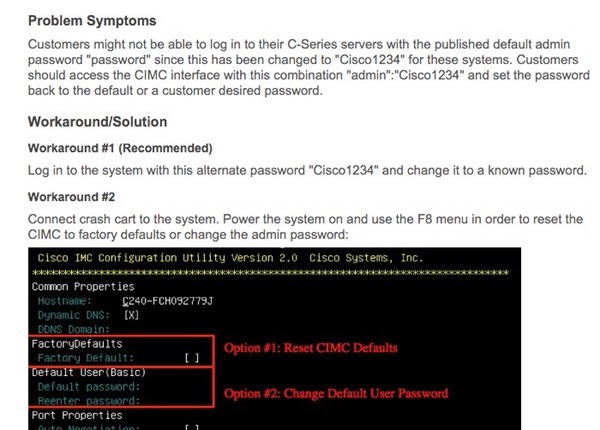
So, no. If you’re a sysadmin who is trying to log into your new Cisco kit’s Cisco Integrated Management Controller (CIMC), and are banging your head against the wall because the default password isn’t working, for once it’s not a case of RTFM.
It should go without saying that as soon as you gain access to your shiny new Cisco box you should reset the password. But not to “password”. Obviously. If you stick with the default password that a product ships with you’re just asking for trouble.
More details about the issue are given in an advisory that Cisco published yesterday.



Actually, the cisco1234 is the one used in the labs for the CCNA (and old CCNP) certificates (once the practices for hardening begin to take place). So, seem someone from Cisco had been with nightmares with that password
Priceless!! All coming from the "security company" that instead of joining standards like IF-MAP has decided that after sitting in for awhile (to gather what it could) decided to go make their own proprietary one (as usual)
1. Cisco Systems isn't a security company.
2. Humans aren't perfect.
3. Humans make mistakes. See point 2.
4. Even those with the best intentions can go afoul. See points 2 and 3.
5. As Raul points out, there is some history with this password.
You also demonstrate some of these points. No, I'm not criticising you but merely pointing out that this is an honest mistake and that is something we all do (anyone claiming otherwise isn't being honest to themselves and by extension to anyone else).