 Independent IT security testing authority AV-Test.org has put nine different fitness trackers under the microscope, in order to explore how well they are protecting users’ data.
Independent IT security testing authority AV-Test.org has put nine different fitness trackers under the microscope, in order to explore how well they are protecting users’ data.
At first it may seem peculiar that the organisation, famous for its in-depth tests of anti-virus technology, has turned its attention to fitness trackers.
But in recent months security researchers have shown increased interest in digging into vulnerabilities on the wearable devices, uncovering weaknesses in authentication processes, and how easy it can be for an unauthorised party to connect to a wearable device without the owner even knowing.
So it’s good to see an independent testing agency also investigating the issue.
After all, fitness trackers are becoming more sophisticated – with vendors adding new features all the time in an attempt to increase their popularity in an increasingly competitive market. But the more features that are added to the system, making it more complex, the chances of it becoming less secure increases.
In its investigation, AV-Test.org researchers examined nine fitness wristbands – Acer Liquid Leap, Fitbit Charge, Garmin Vivosmart, Huawei TalkBand B1, Jawbone Up24, LG Lifeband Touch FB84, Polar Loop, Sony Smartband Talk SWR30, Withings Pulse Ox – and found some big differences when it came to their security model.
(Unlike most product comparison charts, in this case the more checkboxes displayed next to the name, the worse it is!)

There are a variety of issues raised by the investigation, including that many fitness trackers appear to make it too easy for an unauthorised smartphone to connect to the wristband. On one device, which the testers declined to name, they say that it is “disastrous” that that the PIN required is “practically a no-brainer”, and the manufacturer has been informed.
Additionally, some of the products failed to properly authenticate that the smartphone app communicating them was legitimate, opening the door for abuse:
“For this case, the tracker must be able to determine the identity of the connection initiator. At least four of the tested trackers have the ability of authenticating the app they are communicating with. The Jawbone UP24 for example does a challenge-response authentication. It sends a byte sequence to the app which then has to use a secret byte array to calculate an MD5 byte sequence which is then sent back to the tracker. The concept itself seems to be robust, whether or not this authentication procedure works as intended depends on the actual implementation. In contrast, we have the Fitbit Charge, which does not use any authentication on tracker side at all and carelessly provides the saved fitness data to everyone asking for it.”
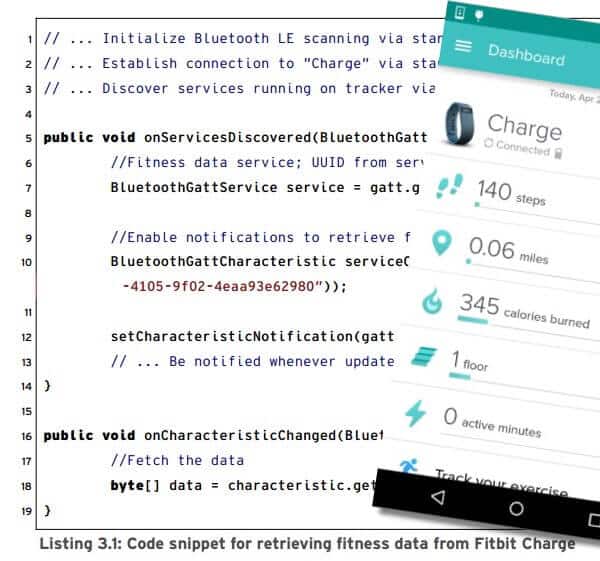
The Fitbit Charge raised concerns in other ways too.
In the words of the testers, “[the Fitbit Charge] simply connects and voluntarily hands over all its data. The data is not even encrypted or protected in other ways. The FitBit app is currently pre-installed on all new HTC devices in the One M8 and M9 series. According to unconfirmed sources, the One M8 alone is said to have been sold between 500,000 and 1 million times.”
Although no products came out with completely flying colours, some clearly did better than others.
“Despite minor areas for potential improvement, the products Sony Smartband Talk SWR30 and Polar Loop offer the most robust security models. The other fitness trackers are ranked lower in their security and therefore higher in the risk assessment. The product with the highest probability of a successful attack is Acer Liquid Leap.”
According to AV-Test.org, concerns with the Acer Liquid Leap may also be present in other products from other vendors which use relabelled versions of the same technology – Striiv (Touch), Tofasco (3 Plus Swipe) and Walgreens (Activity Tracker). Although, it should be noted, the testers have not confirmed the same vulnerabilities are present and it is always possible (although I would be surprised) that those vendors have modified the app or firmware.
For more information, read the press release from AV-Test.org or check out the full findings.

Unfortunately, the AV-Test researchers limited their test to products available in Germany, with apps running on Android phones of different manufacturers, which excluded the likes of the Microsoft Band and the Samsung tracker.
Maybe a wider range of products will be be covered in future testing, by which time lets hope that products have improved.



Having security flaws like these, for such important – we should all be wearing them – devices, can best be described as doubleplusungood.
"we should all be wearing them"
It isn't a need but a want. Just because some might think they're useful doesn't mean they are useful to everyone (keyword everyone because different people think/act differently). People become aware of things differently (some are ever aware and don't need reminders or anything to tell them this or that). As for fitness devices, many actually know where they … well, fit.. in the spectrum. I do not at all need any of these devices and I never will. I am constantly aware (something about having life long health problems makes me very aware of my health and very experienced in dealing with medical problems of all sorts including perhaps even especially emergencies) and there isn't a single feature of these devices that I could use (and just to be sure I just checked a list of features of some). Even if it told me, for example, that I should be taking in more calories, it doesn't mean my weight is somehow unhealthy or that I could be eating healthier (and it won't make me more hungry anymore than it would make someone who has had too many less hungry; keep in mind that calories alone doesn't equate to healthy or unhealthy). The statistics of heart rate over time is interesting, I suppose, but not strictly called for (and when it is there is the holter monitor which has far more[1]). In any case, I have enough instinct/intuition to more or less know what my current bpm is (and much more). The integration I see with smart phones is completely worthless to me because I don't have a smart phone (phones actually irritate me more than anything else). Ultimately, even if there was something of value, wearing a device isn't the only method of helping oneself (a device might not be needed at all).
So by all means, if it helps someone, fine. If it makes someone feel better, all the better. But it isn't a should (need) but a want. But all that said, yes, it is unfortunate they have these security problems. But it also shows even more that they too have many flaws (everything does, of course, but the point is they aren't necessarily as great as they seem; other parts might be better than thought or expected, true). Regardless, the problem will over time get more obvious as more and more wearable technology is developed.
[1] Pacemakers and ICDs also come to mind.