
A hacking gang posted 3.12 terabytes of VEVO’s internal files online, after the company told them to “f–k off”.
The cache of files belonging to the music and video service appeared on 15 September 2017. Included in the data leak were office documents, promotional materials, and other items pertaining to approximately 90 well-known pop artists including Calvin Harris and Taylor Swift.
One leaked file, for instance, documented how the videos of Katy Perry, who suffered a Twitter hack in 2016, had so far generated 12.2 billion views and attracted a gender-based viewing ratio of 54 percent men to 46 percent women.
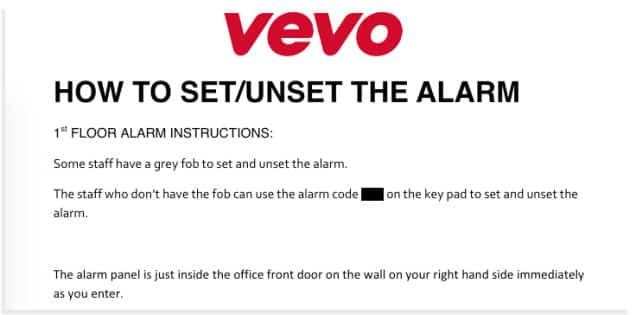
But some of the files contained more sensitive data. One included the alarm code for the service’s UK office. Needless to say, VEVO might want to change that code ASAP.
So who was responsible for this hack?
The OurMine group, a notorious group of hackers which previously launched digital attacks against FC Barcelona, WikiLeaks, and HBO’s social media accounts, has claimed responsibility for the leaks.
As reported by Gizmodo, the group apparently compromised a VEVO employee account for the single-sign-on (SSO) workplace app Okta. It then contacted the service via LinkedIn about the hack, causing a VEVO employee to reply with a less-than-courteous response.
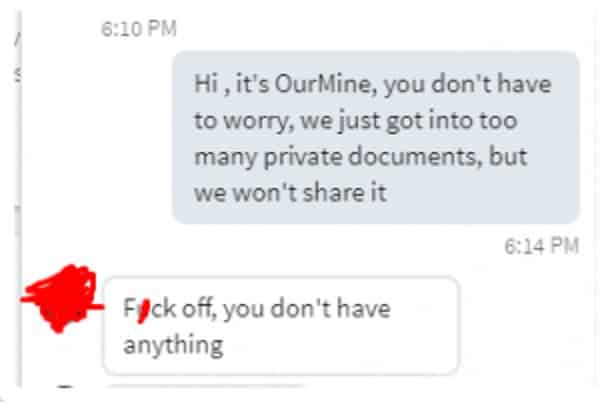
Well, OurMine didn’t take kindly to those words. So it posted the data online. It doesn’t appear the group wanted to monetize the information, however, as it leaked the information for free and said it’d remove the files if VEVO asked.
The service did eventually ask OurMine to remove the documents, and the hacking gang removed some of the download links. According to Bleeping Computer, just one of the remaining URLs actually links to documents for download.
VEVO has confirmed the hack in a statement provided to Gizmodo:
“We can confirm that Vevo experienced a data breach as a result of a phishing scam via LinkedIn. We have addressed the issue and are investigating the extent of exposure.”
A LinkedIn phishing scam, huh? Let’s hope VEVO makes an effort to conduct phishing education training with its employees going forward. It should also emphasize the importance of employees enabling two-step verification (2SV) on their social media media profiles and other corporate accounts.


I'm so confused, isn't Okta there to utilize single sign on and 2 factor? Or were they just too dense to turn on 2 factor and were only using it for single sign on. Seems like if they'd used Okta correctly they could have avoided this, or is there some actual vulnerability in Okta or how they were using Okta? There's something missing here!
This is only the beggining ..a Big party is coming
Phishing education for employees is useful, but VEVO may also want to consider educating its employees on manners.