
Uber has suffered a security breach which allowed a hacker to break into its network, and access the company’s internal documents and systems.
The incident, confirmed by the company in a tweet, and reported by the New York Times, left Uber instructing employees not to use its internal Slack messaging system, and resulted in other systems being made inaccessible.
The hacker, who has shared screenshots of internal Uber systems to confirm his unauthorised access, claims to be 18-years-old. He says that he simply – having already determined a valid username and password – tricked an Uber staff member into granting him access to internal systems by bombarding them with a spate of multi-factor authentication (MFA) push notifications.
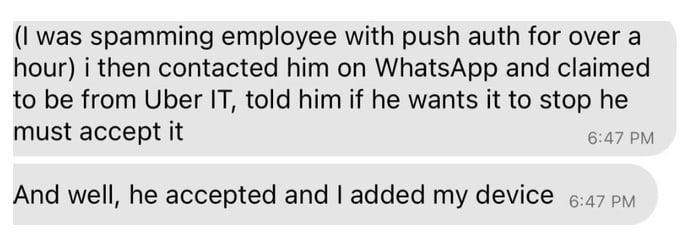
So-called “MFA fatigue attacks” repeatedly spam push notifications to victims until the user is so overwhelmed/irritated/fed-up that they simply grant access to stop them.
Having gained access via the socially-engineered employee to Uber’s VPN, the hacker is said to have scanned the company’s network, and found a PowerShell script containing hardcoded (doh!) credentials for a Thycotic PAM admin account, which then helped unlock access to many of Uber’s internal systems.
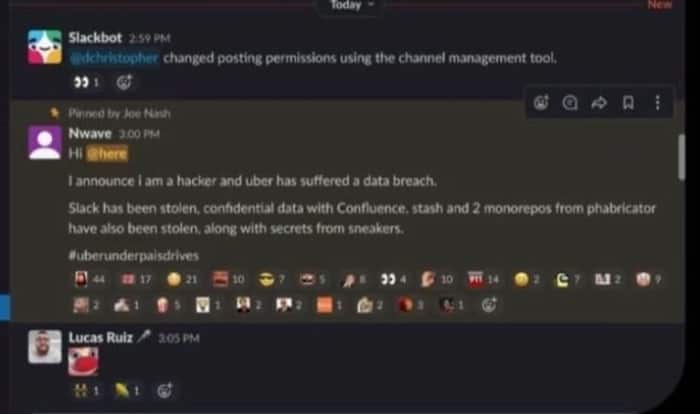
Uber’s security team can’t be feeling too good right now, and the hacker poured salted into the wound by posting a message on the company’s Slack announcing that the firm had been breached.
Hi @here
I announce i am a hacker and uber has suffered a data breach.
Slack has been stolen, confidential data with Confluence, stash and 2 monorepos from phabricator have also been stolen, along with secrets from sneakers.
#uberunderpaisdrives
The truth is, of course, that many many other companies are probably at risk of falling for a similar trick, and may well have staff who have made the mistake of hardcoding login credentials into their PowerShell scripts.
Unfortunately, some Uber staff assumed the message posted by the hacker was a joke.
Many MFA providers allow permission to be granted by receiving a phone call and pressing a key, or accepting a mobile app push notification. Although this can be convenient, hackers can issue multiple MFA requests until their request is finally accepted.
As the LAPSUS$ hacking gang, another group which has exploited MFA fatigue, has previously explained:
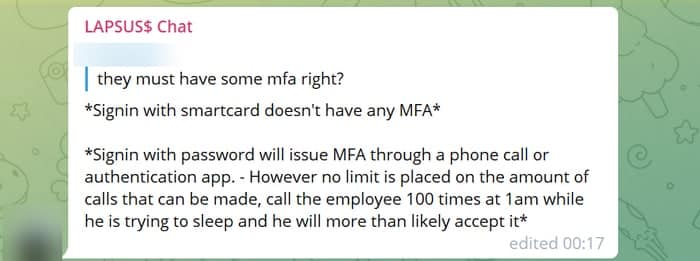
Signin with password will issue MFA through a phone call or authentication app. However no limit is placed on the amount of calls that can be made, call the employee 100 times at 1am while he is trying to sleep and he will more than likely accept it.
Multi-factor authentication is generally an excellent additional level of protection to have in place, but it can’t be implemented in isolation to other security measures, and it should also be carefully configured to maximise the level of security it can bring.


