
Uber has awarded a researcher $10,000 for discovering a login bypass bug that an attacker could have used to compromise the company’s internal network.
On May 4th, Finnish researcher Jouko Pynnönen, who works for the security company Klikki Oy, submitted a report to Uber’s bug bounty program hosted on HackerOne.
He observed how several *.uber.com websites don’t use the WordPress login. Instead they rely on OneLogin, a provider of single sign-on (SSO) and identity management services for cloud-based applications that use SAML and OpenID as well as other formats and standards.

Therein lies the problem. As Pynnönen explained, the WordPress plugin provided by OneLogin shipped with a vulnerability that allowed anyone to sign in without a pre-existing set of credentials:
“The attacker can supply a username, email adress, name, and a role. If the username doesn’t already exist in the WordPress database, then the plugin will create a new user (if the provisioning setting is on, which it was on the two sites I tested). It looks like in order to gain administrator privileges the attacker has to guess some information – a role name such as ‘administrator’, or the email address or username of an existing administrator.”
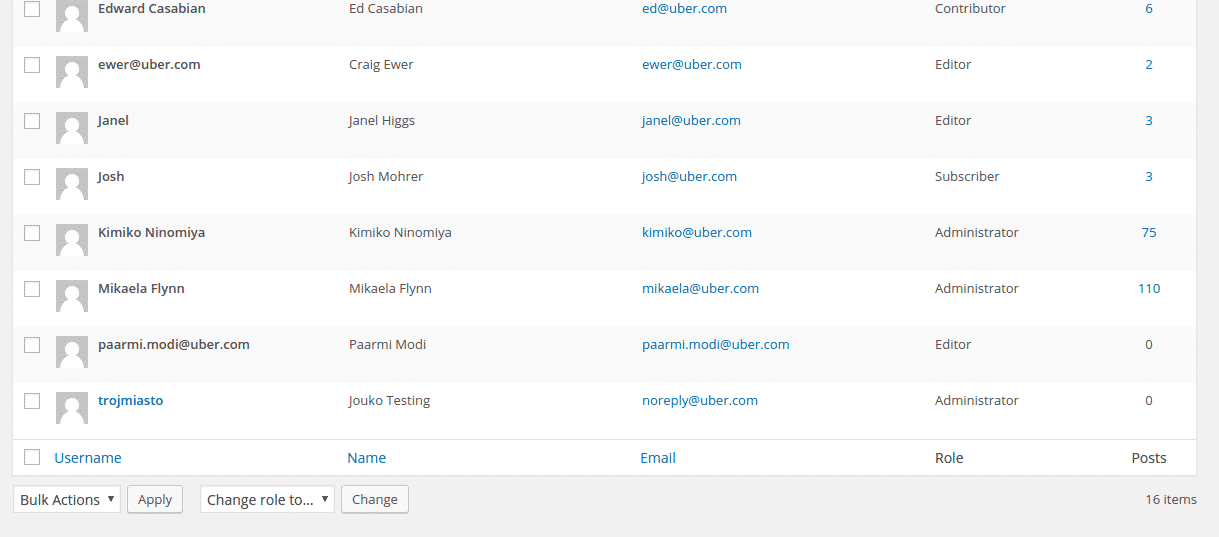
The researcher ultimately exploited that vulnerability on newsroom.uber.com by successfully guessing “administrator” as the administrator role name, thereby allowing him to use the website as a logged-in user.
From there, Pynnönen found he could compromise Uber’s internal network, which is hosted on Atlassian’s Confluence collaboration environment.
As he wrote in a separate report to Uber’s bug bounty program:
“Many (possibly most or all) pages on the said Atlassian Confluence environment refer a script hosted on newsroom.uber.com…. An attacker exploiting a vulnerability on newsroom can modify the adrum.js file… Any injected script would be evaluated for Uber employees logged on Confluence.”
In particular, the researcher described how he could use an attack script to achieve remote code execution (RCE) and install a backdoor servlet on Uber’s network.

The transportation company fixed both issues within a day after receiving Pynnönen’s reports and awarded the researcher the maximum payout of $10,000.
In early June, Pynnönen disclosed the two vulnerabilities publicly.
Perhaps nothing is more satisfying than a bug bounty program that works as it should. I commend the researcher for respecting responsible disclosure, and I give credit to Uber for promptly fixing the issues.
For more information about Uber’s bug bounty program, please click here. You can also read a transparency report issued earlier this year by the transportation company here.


