
You think you’ve had problems online?
Spare a thought for William C Bradford, an American lawyer who was recently appointed by Donald Trump to run the Energy Department’s Office of Indian Energy.
As The Washington Post discovered, before entering public office, Bradford’s Twitter account was prone to making some eyebrow-raising declarations about the previous US president…
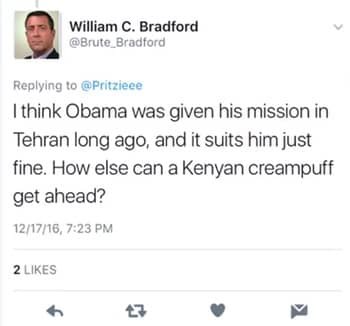
…and the founder of Facebook.

The tweets from @Brute_Bradford have since been deleted, and Bradford emailed an apology to the newspaper:
“As a minority and member of the Jewish faith, I sincerely apologize for my disrespectful and offensive comments. These comments are inexcusable and I do not stand by them. Now, as a public servant, I hold myself to a higher standard, and I will work every day to better the lives of all Americans.”
Okay, so that would be awkward enough. But if you’ve owned up to acting in an inappropriate way, don’t be surprised if other media outlets wonder if they might be able to dig up some other past misdemeanours.
Like, for instance, the account CNN uncovered that Bradford had with the Disqus commenting system.
CNN uncovered plenty of awkward comments left by Bradford’s Disqus account on assorted blogs, but here’s a choice example:

I have to say, I’d be pretty upset if someone had called my mum a “porn actress”, but even more outraged if I was told she was only fourth-rate.
However, we would be wrong to jump to conclusions that these Disqus messages were sent by the same person who admitted sending the tweets.
PLOT TWIST!
Because, it turns out that William C Bradford was not the potty-mouthed scamp who left those comments uncovered by CNN, but instead he is actually the victim of a hacker.
And possibly not just one hacker, but a concerted attempt “over the past several years” by hackers to attack him and break into his email, according to a statement the recently appointed DOE office director gave to CNN:
“I cannot comment on an ongoing federal investigation into multiple cyber attacks and Internet crimes committed against me over the past several years, to include email intrusions, hacking, and impostors in social media.”
Obviously no-one deserves to be hacked. And it must be ghastly to have your account hijacked by others who seem dead set on damaging your public reputation year after year.
It’s a ghastly situation, but Bradford has done the right thing calling in the Feds to investigate what’s been going on. I hope they will do a through investigation and determine precisely who was behind this scurrilous attack.
By the way, in 2015, Bradford resigned from the US Military Academy at West Point after urging attacks on Islamic holy sites and claims he exaggerated his military service record and academic career.
Unless, of course, that was the hackers too.
For further discussion on this story, make sure to listen to this episode of the “Smashing Security” podcast:
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
And she also said to me that one of the episodes she listened to was sponsored by Recorded Future.
And Recorded Future produce a daily threat intelligence newsletter that she decided to sign up to.
She works in media, so she wants to know all the security things that are going on, and she says it's an amazing newsletter and she loves it. So isn't that cool?
Hello, hello, and welcome to Episode 40 of Smashing Security for the 31st of August, 2017. I'm Graham Cluley, and I'm joined as always by my good chum and co-host, Carole Theriault.
Hello, Carole, how are you doing?
It's almost an Instagram celebrity.
But just briefly describe who you are, what you do, and what are you doing here on our podcast anyway?
But in between doing that, gee, what do I do now? So I do a lot of traveling and speaking at events on security things. I do a lot of training. I do a lot of workshops for companies.
I do a lot of online training. And I run this little thing called Have I Been Pwned as well.
I'm going to kick off and now guys, I don't know if you— well, Carole, you were here for last week's episode.
Troy, I think you may have heard last week's episode with Scott Helmee. I ran a very, very popular and successful quiz last week on the show.
And when I say it was popular, I had one person who replied positively.
I'm going to give you a statement by a politician and you're going to tell me if it's the truth or a lie.
I want to say one thing to the American people. I want you to listen to me. I'm going to say this again. I did not have sexual relations with that woman, Miss Lewinsky.
But it is late here and I've had a bad day. So yeah, why not?
He's an American lawyer who was recently appointed by Donald Trump to run the Energy Department's Office of Indian Energy.
I have no idea what that is, and calling Mark Zuckerberg— and apologies for this, I am quoting— an arrogant, self-hating Jew.
Now, he admitted sending some tweets saying Barack Obama's mum was a fourth-rate porn star and whore.
Especially if it's someone's mum, although not as bad as a fifth-rate. What he's saying now, right, is this.
He's making a statement which says that it wasn't him who left similarly veined and similarly styled messages via the Disqus commenting system, as dug out by CNN.
No, no, no, he says, although he admits to the tweets, those comments weren't from him at all because, and here's the quote, right?
Here's the next round of the game, final round of the game. Here's his quote. I don't know what he sounds like, so I'll just do a standard American accent at this point.
Over the past several years, which include email intrusions, hacking, and imposters in social media.
In other words, he's saying that hackers took over his Disqus account and are leaving all these offensive comments on blogs and things, but he can't go into more details because the feds are investigating it.
My question for you two, is he telling the truth or telling a fib?
You know, it does seem a little bit of an odd coincidence considering the tweets which he has admitted to. Really?
We've seen over the years, for instance, I know there's been a number of rappers and things, you know, sort of celebrity rappers who sometimes have said really offensive stuff on social media.
And then their get out of jail free card is always to say, "Oh, my account was compromised. I was hacked." Didn't—
I mean, if you're in that kind of panic, maybe you would use that excuse. "Hey, honey, it wasn't me.
There's some hacker who's installed all of this hardcore porn onto our computer or hidden it away in my Dropbox folder." I mean, maybe this is like the standard excuse that people use.
I just think it does us all a disservice to allow this kind of thing to be got away with. And it kind of discredits the genuine attacks in a way.
You know, I just wish people were honest. Yeah, I did get hacked. Or no, it wasn't a hack. I was just being dumb online.
I mean, look, everyone listening to this knows this sort of stuff is— these are solvable mysteries, right.
So it's the sort of thing where if you want to go and sort of spin a yarn on this, you want to be pretty sure no one's actually going to look into it, or else the whole thing is going to come apart pretty quickly, right?
I think if you're going into public office, particularly if you've already been outed for something else, maybe do your best to clean up the rest of your online activity, or if you can't do that, just put your hands up when you're accused and say, yeah, I used to say those things several years ago.
I've grown up now.
Sometimes there is a genuine hack or compromise of a social media account.
We saw this last week, Selena Gomez, who used to be dating Justin Bieber, her Instagram account got hacked. She has 125 million followers on Instagram.
How are you comparing with that, Troy?
That every time I hear about people with massive followings like this, that the first thing that comes to my mind is that this would be the most awesome sort of organic DDoS engine in the world.
It's like, I don't like someone, I'm just going to tweet something, you know, or Instagram it or whatever they do. And it's like, boom, that's it, you're gone, you're offline.
You know, you've got to have some serious defenses.
But I reckon 120+ million followers might do it.
And he actually used to contact companies before he tweeted their website because he knew the power of his audience could bring down sites, which obviously wasn't his intention.
So it can be a problem. Gomez, her Instagram got hacked. Chances are, I think, that she didn't have two-factor authentication enabled. Instagram does offer it. You should turn it on.
Unfortunately, Instagram only offers two-factor authentication via SMS message.
It'd be nice if they got a little bit more modern about that because some have concerns about that method of authentication.
But I think the other message is, you know, aside from everyone should turn on 2FA or two-step verification, when you say something unpleasant online, when something bad happens, in this case, Justin Bieber's— I believe in Australia you call them ankle spankers.
Anyway, a part of his anatomy was exposed.
I would love one of these celebrities one day when they get hacked, not just to go, oh yeah, I got hacked, but actually talk to their 125 million followers and say, don't make the mistake I made.
Turn these features on to protect your accounts.
You did something stupid. Like, that is what it boils down to.
And it's probably the same stupid thing that 90% plus of people do, which is it's a crap password and you used it on LinkedIn, and then that got hacked, and then it was SHA-1 and it got cracked.
And, you know, here we are. It's always the same story over and over again.
And I honestly can't remember a time where it was legitimately, 'Well, yeah, Twitter did actually have some funky 0-day and someone broke into someone's account.' It's always someone doing something stupid.
So basically he's already eating poo for his comments he's already done.
But as luck would have it, things eventuated such that I came across 711 million email addresses which are now and have ever been pwned.
And now it's like, yeah, here's just one whack, 711 million.
So I have spent the last, basically the last 48 hours firstly consuming a great deal of Azure's capacity trying to load all this data.
Next I'll be explaining to my wife why we have suddenly spent a lot of money to a company based in Redmond. And then I've— I made this data live.
I'm at sort of 10:20 PM or something now, so I made it live about 15 hours ago.
And I've— I'm up to about 200 comments on the blog post, and the floods of tweets and emails, and I've been doing media and stuff today as well.
So it's just been an absolute write-off of a day, on a day where I was actually meant to write a talk. So I'm not quite sure how that one will work out, but—
So Troy, this— we appreciate you staying up late and taking the time to speak to us today, but this data you have, these 711 million email records, where did they come from?
How were they being abused? And what should people do if they are one of those 711 million?
And one of the things that always happens after I load data of sort of— I was going to say ill repute, but you know, where it's sort of from odd kind of sources— after I load it and people start finding their data on Have I Been Pwned, I start to learn a bunch of interesting things.
But the background in terms of how it turned up is a French malware reverse engineer bloke who does a lot of looking into how some spambots run had found an open folder share as part of— I think it was actually part of his reverse engineering of one of the pieces of malware.
He had ended up pointing to an IP address, found a folder share on there, and found 180+ files that totaled, I think, about 35GB worth of data.
Yes, you can actually have a 14-gigabyte text file. Don't try and open that in Notepad, everyone listening.
But all of this seemed to be— well, a lot of it seemed to be sort of unrelated to each other, other than it was all in this sort of realm of credentials.
So the usernames and passwords were kind of interesting because one of these files reconciled verbatim with LinkedIn, the LinkedIn data breach.
So every time I put in an email address to Have I Been Pwned, it was like, yep, LinkedIn, LinkedIn. Another one reconciled with one of the big combo lists I loaded.
So these were lists of email address password pairs. So sort of the origin, if you like, was clear there. But then just a bunch of random junk as well.
I mean, there are a bunch of files in there, or one file with a bunch of rows that indicated it was from the Roads and Maritime Services Department in one of our local states here, and it related to the e-toll, which is the little tag you put on your windscreen when you drive through the tolls.
So anyway, we've found all this data, and the guy who found it has explained that this is used by an online spam bot called Onliner Spam Bot, which is kind of interesting.
And he said what's actually happening here is it's a combination of some of these files have credentials as well as SMTP addresses of the mail servers that these accounts would use and the SMTP port it was using.
There's a few different ports that SMTP typically uses, and the spam bot is using these because it will then connect to those SMTP servers under the identity in these files because it's hard to find open SMTP relays these days to send spam.
So part of the value proposition of the data was here is a mechanism for us to send spam, and then of course, the masses and masses of email addresses and just email addresses in files.
Well, you know, every time you get Viagra spam, it's stuff like this. That's kind of interesting - they were just being used to send mail to.
And then as I loaded this and I started getting feedback, some really interesting trends popped up.
So one of the features on Have I Been Pwned is you can do a domain search and you could just prove that you own the domain via getting an email to the WHOIS record or adding a TXT entry to DNS or something.
And you do a search and people were saying basically 70% plus of the aliases on my domain in this quote-unquote breach were fake, you know, that they're not real.
And it looks like there's a bunch of junk in there as well as a bunch of fabricated addresses.
And one person actually said to me, he said, I have a catch-all on this domain, so I get everything that goes to @whatever.
And I found that a bunch of those aliases that were in this spam bot list had actually been getting spam.
And this sort of asked the question to him, you know, what on earth is going on? Where's this coming from? And that was just the beginning.
And then the day just unfolded as people came up with everything from really interesting insights to abuse. That was fun.
And as I said, a bunch of these were fabricated as well. And you can - geez, you can make up as many fake email addresses as you like.
But to your point about the flow, the flow is really interesting, you know, how data goes from one breach to another list somewhere, and then it gets abused somewhere else, and then gets passed downstream.
And one of the comments I made in the blog post I pushed out with this today was that most people have got no idea how far their data gets spread and reused.
And it's just mind-boggling.
So you've had a really, you've had a really crappy few days, or has it been really challenging in a good way, or you're just now, you're just dead?
I think the thing that sort of started to get to me a bit today is I made a judgment call when I started this service almost 4 years ago that I wasn't going to have passwords in the system.
So, you know, if you're in, say, the LinkedIn data breach, you can't go to Have I Been Pwned and find your LinkedIn password.
And there's many reasons for that that include technical reasons. So for example, a lot of passwords are, say, bcrypt hashes.
Nothing you can do with the bcrypt hash other than give the hash to people, which will make absolutely no sense to 99-point-something percent of people that use the service.
Because this thing is so mainstream these days, imagine saying to a non-techie person, hey, here's your bcrypt hash from Ashley Madison, just so you know what your password was.
Yeah, good luck with that.
And the other side of it is that no matter how much we sugarcoat it, this is all data that someone has illegally obtained out of various systems, often using means which will land them in prison for a long time if they get caught.
Yeah, the legitimacy of actually having it and making it available in this fashion is questionable without a doubt, and I am doing everything I can to try and run the thing ethically.
And, and to be honest, I was going to say keep my head down a little bit, but it's a little bit hard when it's this well known now.
But I guess not do things that would raise the ire of either individuals or organizations.
And we have seen cases in the past where the likes of LinkedIn has issued— this is It's just getting late.
LinkedIn issued a takedown to one of these really dodgy services that popped up called LeakedSource because these guys were making passwords available.
And, you know, to me, this was sort of one of the indicators of once you have passwords as well, you're sort of stepping into another realm.
And no matter how well I try and protect them, just the fact that I would have those passwords in the system and they were retrievable, just— it just is way, way too much risk for my comfort level.
I mean, it would be hard to sleep at night knowing that you've stored that much data and potentially, even if you've gone to great efforts to encrypt and keep it securely, that someone might have found a vulnerability or some way in order to get some of it to spill out.
And then you get your great unwashed out there, apologies to the great unwashed, and they're sort of going, "Well, why don't you just email me the password?" "Oh no, I can't.
Do I have to explain it?" Yeah.
And we'll also include a link to Have I Been Pwned as well, because it really is a fantastic service. I think everyone—
And I have searched for things on the internet that have led me to places I didn't expect to end up.
And folks really should sign up because, I mean, I got my warning because I've registered my domain with you and it told me about a number of email addresses which apparently are included in this spam bot dump, including ones which aren't really addresses.
You know, it was interesting to me as well that some of those popped up in the list. So it's only going to become a bigger problem, isn't it?
I don't think we're probably that far away from, I don't know, a billion record dump coming up.
So this was late last year, they said, hey, we had half a billion accounts exposed, and it was very embarrassing.
And then they came back a few weeks later and they said, 'Oh, if anything happened—' Well, they didn't say 'if anything,' but they came back and they said, 'We've just realized there was also another one and it was a billion.'
Yeah, it's apparently the worst hurricane that's hit the state in 50 years.
And today I just read that 13,000 people in the Houston area and surrounding areas have been rescued from the tropical storm, and there's been at least 18 deaths.
And one of the big problems is people don't want to leave their houses. They don't leave their stuff. They don't leave their lost pets. Right. And it's just horrible.
But with crazy situations and weather this, crazy things happen. And you might have heard about the planes that were flooded at Houston Airport thanks to the tropical storm.
You may have heard about a shark that was found swimming along the flooded highway, as reported by Fox News.
So the drowning planes picture was a 2013 mock-up created by Climate Central to show the effects of climate change.
And it's actually not even Houston Airport, it's LaGuardia Airport. So it shows you all the people sharing it actually can't even recognize that.
So all the people who are real airport nerds, it's, I think you'll find that's actually LaGuardia. Come on, Carole. Yes.
Well, if you can't— No, I mean, maybe from where you go in, the arrivals hall or whatever, but you can't tell when it's just a runway with some planes on it.
I think you've been a bit harsh.
So it was just basically doctored up and put onto the highway.
Some people would argue that because of these hoaxes, the disaster is staying in the press and it gives journos new angles to talk about the problem and the disaster.
And it's not just the politics side of things.
I'm seeing it the whole time even in the security side of things, where people will sort of say, hey, this incident happened, or this security thing happened, and it's like, well, it sounds stupid, but there's a lot of real stuff that happens that's actually pretty stupid too.
And I don't know what's legit anymore or not. And it's— in fact, I've read something about this only last week, because this is it.
I've certainly seen things and shared things that seemed perfectly feasible, and then, you know, here we are.
You know, you've found it interesting. You may not even have clicked on the link yourself. You just thought, oh, I should tell my mates about that.
And you kind of pass the buck onto them to find out whether it's true or not and to be skeptical. But you've given it some kind of endorsement by sharing it.
I mean, Journalism 101 was always, you know, have two independent sources verify a fact, right?
And today, that's quite difficult, because if everyone's repurposing news and not necessarily crediting a source, you can— it's easy to kind of think you've done your research and you've got something that's valid.
In fact, you're just spewing garbage.
And that's things like insurance and charity scams. So basically, fake disaster relief campaigns.
And US-CERT has just issued a statement this week warning people to remain vigilant of criminal activity capitalizing on the interest in Hurricane Harvey.
So according to CNET, we have seen a few phishing emails relating to Hurricane Harvey. And this is how they're working.
So they are citing legitimate fundraisers, right, like the Greater Houston Community Foundation and the Hurricane Harvey Recovery Fund, but the actual links go to bogus or fake sites.
And we've seen some actually on Facebook as well. So we've seen some— so, you know, Facebook have pledged to match, I think, up to $1 million in relief funds.
But we've also seen some people kind of put up fake ads saying, hey, you can support the Facebook Fund.
We've got a good heart and all the rest of it because they're touched just like the rest of us as to what is happening out in Texas.
And because you've seen them do that, you think, oh, well, I'll donate as well and I'll click on that link that Fred has just shared with me.
We saw this, for example, in — was it 2010 Hurricane Sandy? 2012? This is awful, I don't remember. But there was an email that came from redcross.net.
This is just to give you an example of another way that these work.
So the email would read, "Thank you for your donation to Hurricane Sandy relief." You haven't really done a donation. You never — you just received this unsolicited email.
"We appreciate your donation," the letter continues, "of $435. The credit card on file has been charged.
If you did not authorize this donation, please go to enter fake website URL to unauthorize the charge." Sounds legit. So a little reverse psychology going on.
How can they have debited my credit card for that much money?
And you're right, it is social engineering because you sort of have that moment of dread where you go, what have the kids done now? You know, let's go and figure this out.
And of course, they leverage off the combination of the inquisitiveness that we have when these incidents happen, whether it's a natural disaster or a celebrity dies or something.
And they sort of combine these factors together in a very cunning way.
So what can people do about this?
So I would recommend don't follow unsolicited web links and email messages that you haven't requested. Don't click on ads in order to give money away.
And go to the National Charity Report Index and check with the FTC information on wise giving in the wake of Hurricane Harvey. So these two links will be in the show notes.
And be wary, even if your friend is sharing a link, it may be that they've got some bad information.
I saw one scam being passed around where people were being told if they found themselves in an emergency situation to ring an emergency number and they gave a number and apparently it was the number, so I'm told at least, of an insurance company rather than —
But yeah, those things have happened before, and I'm sure we will see them if it hasn't already happened.
Recorded Future is the real-time threat intelligence company whose patented machine learning technology continuously analyzes technical critical, open, and darkweb sources to give organizations unmatched insight into emerging threats.
Sign up for free daily threat intelligence updates at recordedfuture.com/intel.
You know, there was that thing the other day which was showing how you— I don't know if you guys saw this— where it can take someone's voice, you can listen to a few words that they say and then reconstruct sentences.
So, you know, you'll— you'll— I don't know if it speaks Australian, but you'll work it out. Well, Graham can just—
Not necessarily security related. Something cool, which is our pick of the week. And my pick of the week I've got in my hands right here. Here it is. Can you hear that?
This is the Phoenix Comic, and this is a comic which my son gets actually, but I quite enjoy it as well.
So I've got a son who's about 6 years old, and this probably is applicable for kids between about the ages 6 and 12.
It's made in Oxford, which is where I come from and where Carole is based as well, but I believe you can get it ordered and delivered around the world. And it is fabulous.
It's got— Well, what's in it? Well, all right, I'm going to tell you. It describes itself as the weekly story comic, and it has fantastic artwork and comic strips.
I'm looking right now that there's another episode of Good Dog Bad Dog, The Golden Bone of Alexandria in it. There's Bunny vs Monkey.
It is tremendously slightly anarchic, very, very visual, but there's also puzzles in it and there's advice on if you want to draw smoke, this is how you draw smoke, and it describes different kinds of smoke in this particular tutorial.
So you're learning how to draw, because these guys are terrific artists, and it is a great read.
And if you've got someone in your family who's maybe a slightly reluctant reader and won't pick up a regular book, maybe something like the Phoenix Story Comic would be right up their alleyway.
There are adventure stories, funny original sort of jokey comics, some non-fiction as well, and mind-bending puzzles.
I have to say, I think I probably actually look forward to its arrival every Friday morning a little bit more than my son does.
Maybe I should get you a copy, a subscription for your birthday or something like that.
What about your house, Graham? What about your pension, Graham? Well, I mean, eventually, right? It's going to become— what about your wife, Graham?
Do you prefer your son or your wife? Right? That sort of question.
Now I've put a little link in our document here, and this only goes for 30 seconds, so you guys can watch this while I'm talking about it.
It is called a Little Ripper Lifesaver drone that can spot sharks. Now this is pretty awesome.
This was in the news, probably the news all the way around the world, certainly the news here just last week.
And it is a drone that they fly over the beaches, and it has— it's OCR for sharks, right?
Or it's— well, it's not even OCR, it's facial recognition for— I'm watching it right now. So, you'll see it's going dolphin, dolphin, fish, shark. Yes.
You know, so it's flying above the ocean and it's just that it— you could just see these blobs, right? But it knows what is a shark and what is a dolphin. Well, there's a whale.
And the cool thing about it is that this obviously feeds back to a bloke who's sitting there, you know, flying the thing around, and you can then sort of go, okay, surfers, it might be time to get out of the water.
Okay then, that's really cool.
And it can be like 2 cents or 5 cents or 3 cents. And you can also set an upper limit because, you know, we know he loves the Twitter.
All right, so you don't want to sit there finding out that you've got 10 grand to owe every month.
Apparently that is—
I think they're trying to raise a billion dollars so that they can buy a big enough share of Twitter to get his account deleted. I don't think they've raised very much.
Well, that just about rounds off the show, I think, for this week. Oh, you know what? Sorry.
If you want to wish us a happy 40th you can follow us on Twitter @SmashingSecurity without a G, that's Twitter's fault, not ours.
They wouldn't let us put a G in there, too many characters. Or you can follow us on Facebook as well.
You can go to smashingsecurity.com/facebook and that'll take you straight to our Facebook group. And we've got swag now. You can buy a t-shirt at smashingsecurity.com/store.
All that remains to be done is ask our guest. So Troy, where can folks find you online? What do you want to plug? Where should people go if they want to find out more about you?
And of course, you can find HaveIBeenPwned.com as well.
So if you're listening to this thinking you're going to get it, it's too late. You can go there right now and you get redirected. You are brilliant.
Thanks for costing me $14 a year Graham Cluley, I'll send you the bill.
If you like the show, tell your friends, leave a review on iTunes, go to smashingsecurity.com for past episodes, and drop us a line at .
Until next time, from all of us, cheerio, bye-bye. Thanks for listening. Thanks, guys. Ah, smashing. Well, we made it.



I'm sure there are plenty of people on the other side of the political spectrum equally dubious. But the problems Graham, is the MSM only seem interested in embarrassing those on the right. Which is why, the majority of Americans have very little respect for the Media in general. They have for years, the MSM have only attacked conservatives, or Republicans, in the most scurrilous ways, but when Democrats are exposed, they ignore, or spin those problems that make them all look bad.
Rest assured David, I'm just as happy to criticise left-leaning politicians as the right when it comes to sloppy security or – indeed – the age-old game of blaming some personal goof on external hackers.
And I think it's inaccurate to claim that Democrats have got away scot free from media attention. Just consider the countless news reports about the John Podesta attack, Hillary Clinton's dubious use of her own email server, the hacking of the DNC…
Hey, also, a lot of celebrities identify with the liberal left, and there's no shortage of internet security screw-ups there.
Graham- you have swallowed David's unspoken premise: that you are a member of the mainstream media. As a technical specialist reporting on specific topics you can easily disassociate yourself from the bias displayed by the major organs of news distribution.