![]()
Malicious hackers can use tracking pixels to help them gather intelligence for attack campaigns, both mass and targeted in scope.
Digital marketing firms have long used tracking pixels (longer than they’ve been using the Battery Status API, at least) to analyze email and web marketing campaigns. These pixels are image files that are usually just one pixel in size, a design which prevents users from noticing them in most cases.
With code as simple as <img src="http://example.com/cgi-bin/program?e=email-address">, the marketing tools ping a website whenever someone downloads an image.
Tracking pixels can do more than just provide notice of someone engaging with a media file. They can also gather information about a user including their IP address, operating system, web browser and send it to a designated email address. The operator of that address can then use that information to fine-tune an advertising campaign.
Unfortunately, tracking pixels don’t just help advertisers. Attackers can also abuse them to carry out malicious campaigns.
Donald Meyer of Check Point elaborates on this misuse of tracking pixels in a blog post:
“In phishing attacks, tracking pixels can be used to learn which recipients are most likely to open scam emails. Since some scammers retool mass phishing attacks against random users to target high-value enterprise users, scammers are turning to pixel tracking to increase the odds a spear phishing attack will succeed…. Our security researchers have already discovered tracking pixels being used in the wild as a surveillance tool to gather information for use in phishing scams.”
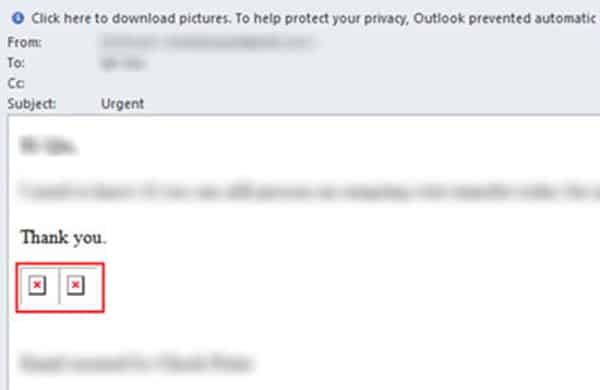
Indeed, Check Point detected tracking pixels used for a phishing campaign back in August 2016. The red “X’s” mark the location of the pixels, which email security tools prevented from loading properly.
Not only that, but because Microsoft Office documents also accommodate tracking pixels, attackers could insert one such image into a Microsoft Word document and send it to multiple individuals in a company. They can then track the documents as they move throughout the organization, mapping the company as they go.
When all is said in done, the bad actors can use this information to conduct targeted attacks in the future.
Fortunately, it’s not difficult to protect against this sneaky threat.
Organizations can use anti-phishing and email security solutions to protect against suspicious images. You may be able to prevent your email client from automatically loading images from unapproved senders. Continuous patch management and a healthy dose of skepticism around emails that contain anomalous image placeholders go a long way, too.


