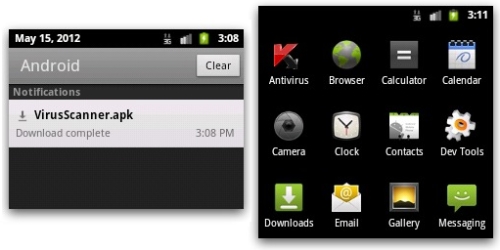
 The release of a brand new version of Sophos’s free anti-virus for Android (it actually does much more than just anti-virus, hence our marketroids call it Sophos Mobile Security) makes this an opportune time to update users on the Android malware landscape.
The release of a brand new version of Sophos’s free anti-virus for Android (it actually does much more than just anti-virus, hence our marketroids call it Sophos Mobile Security) makes this an opportune time to update users on the Android malware landscape.
SophosLabs has examined the stats produced by installations of Sophos Mobile Security, which is now being used on Android smartphones and tablets in 118 different countries around the world – and it’s making for interesting reading about which malware is being most frequently encountered on the platform.

1. Andr/PJApps-C. When Sophos Mobile Security for Android detects an app as Andr/PJApps-C it means that we have identified an app that has been cracked using a publicly available tool. Most commonly these are paid for apps that have been hacked. They are not necessarily always malicious, but are very likely to be illegal.
2. Andr/BBridge-A. Also known as BaseBridge, this malware uses a privilege escalation exploit to elevate its privileges and install additional malicious apps onto your Android device. It uses HTTP to communicate with a central server and leaks potentially identifiable information.
These malicious apps can send and read SMS messages, potentially costing you money. In fact, it can even scan your incoming SMS messages and automatically remove warnings that you are being charged a fee for using premium rate services it has signed you up for.
3. Andr/BatteryD-A. This “Battery Doctor” app falsely claims to save battery life on your Android device. But it actually sends potentially identifiable information to a server using HTTP, and aggressively displays adverts.
4. Andr/Generic-S. Sophos Mobile Security generically detects a variety of families of malicious apps as Andr/Generic-S. These range from privilege escalation exploits to aggressive adware such as variants of the Android Plankton malware.
5. Andr/DrSheep-A. Remember Firesheep? The desktop tool that can allow malicious hackers to hijack Twitter, Facebook and Linkedin sessions in a wireless network environment? Andr/DrSheep-A is the Android equivalent of the tool.
As I’m here writing this run-down, I might as well document some of the other most commonly-seen Android malware:
Andr/DroidRt-A is a set of privilege escalation exploits that can allow someone to to obtain root access to an Android device.
Andr/Opfake-C is a fake Opera app which may install other malicious Android packages and send SMS messages to a premium line number, depending on country.
As you can see for yourself in the following video by SophosLabs researcher Vanja Svajcer, the Andr/Opfake-C malware has been spread via Facebook in the past.
https://www.youtube.com/watch?v=JPlJrB652w8
Andr/Boxer-A. Similar in terms of functionality to Andr/Opfake-C, this malware poses as a fake installer for an Opera browser update, Skype, Anti-virus software, Instagram and many other popular apps.
The malware may install other malicious Android packages and – predictably – send SMS messages to premium rate services numbers. It attempts to evade detection by adding a random number of images of “witness from Fryazino” therefore making the APK file binary different every few downloads.
It’s quite clear that Android malware is a growing problem.
Thanks to SophosLabs researcher Vanja Svajcer for his assistance with this article.



