
An attacker can easily use three pieces of publicly available information to pwn anybody’s Myspace account.
Security researcher Leigh-Anne Galloway came across this security oversight back in April when she stumbled across an old Myspace account of hers. The researcher decided she wanted to delete her account, but she needed to sign in first. To do that, she went to Myspace’s account recovery page.
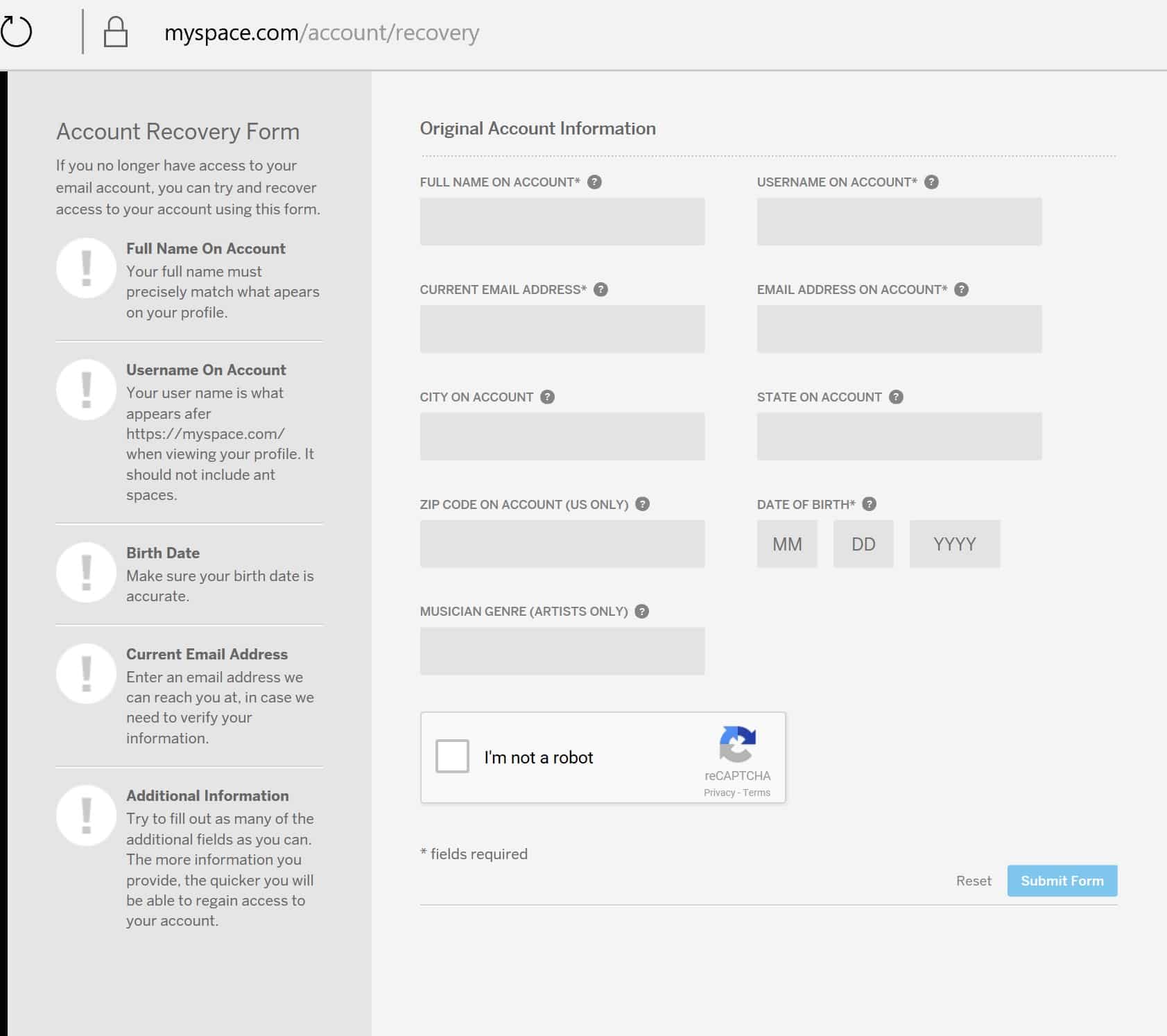
As you can see in the above screenshot, Myspace asks for several pieces of personal information before it will restore access to a lost account. There’s just one problem: notwithstanding the “field required” asterisk affixed to the email address text field, Myspace doesn’t validate a registered user’s email address. That means a user can recover their account with just their name, username, and date of birth.
Easy, right? A little too easy.
As it turns out, it’s nowhere near impossible to find these three pieces of data online.
Attackers can use a Google search to find a Myspace user’s name and username online. (A certain breach confirmed by Myspace in 2016 lessens the load of discovering these two bits of information.) Attackers might have a more difficult time finding someone’s birth date, but you’d be surprised how many people list their special days on Facebook or other social media platforms.
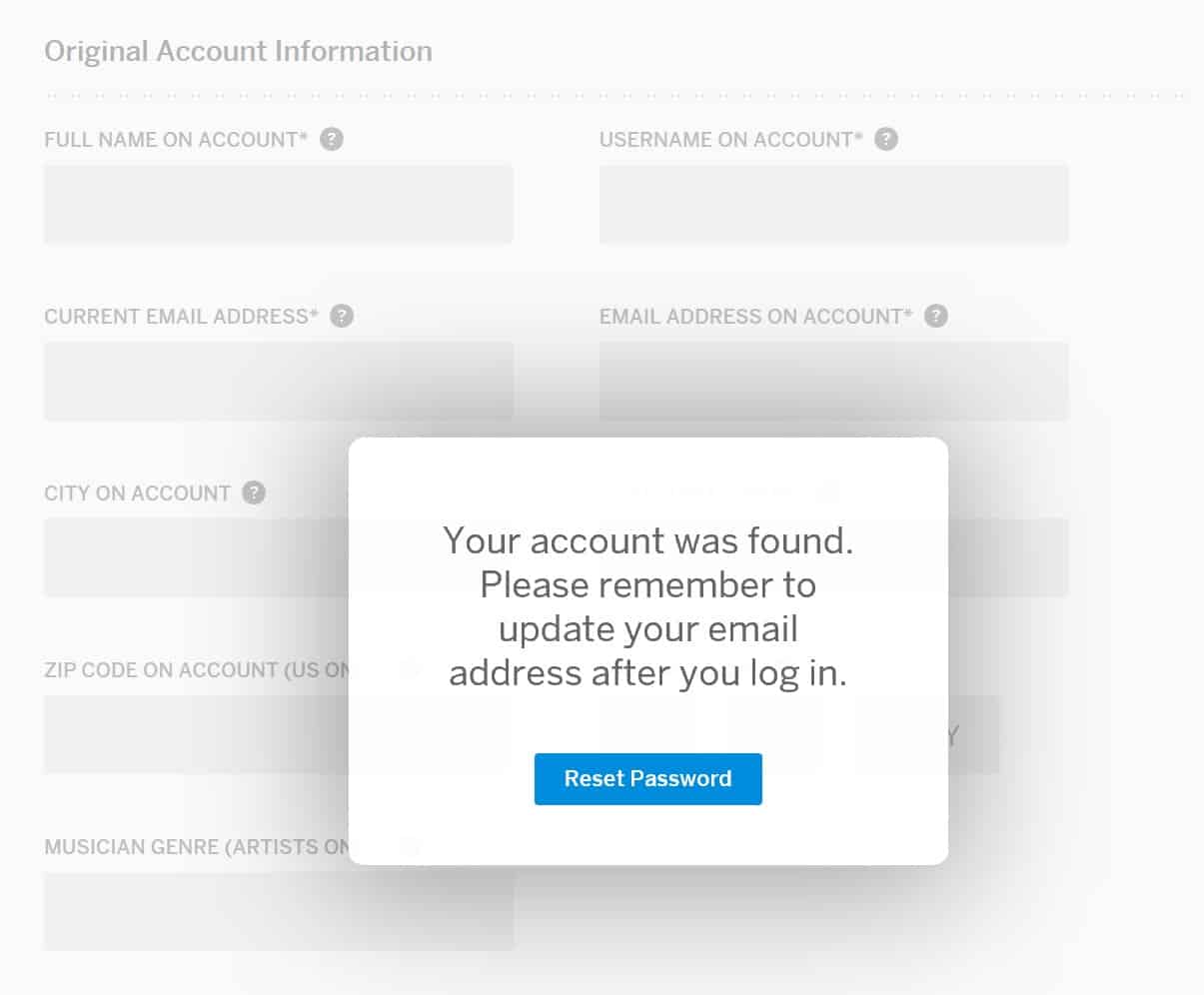
Whoever enters in that information receives from Myspace instantaneous access to the registered user’s account.
Galloway couldn’t believe her eyes. As she explains in a blog post:
“Myspace may no longer be relevant as a social media site, but its treatment of security is as relevant as ever.”
In support of this viewpoint, the security researcher wrote to Myspace about the vulnerability on 23 April. She had not heard anything as of 17 July, the date on which she decided to disclose the vulnerability.
Without any word from Myspace indicating it intends to fix the flaw anytime soon, users who are concerned that someone could access their account, read through their old messages, and abuse their information don’t have many options. There’s really only one course of action: users should leverage Myspace’s account recovery to regain access to and subsequently delete their accounts. It’s not the optimal course of action, but when a company doesn’t care about their customers’ data security, there’s nothing left to do.
Shame on you, Myspace, for such a disreputable end…
For further discussion of this incident take a listen to this episode of the “Smashing Security” podcast:
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Sign up for the free daily threat intelligence update at recordedfuture.com/intel. That's recordedfuture.com/intel.
Hello, Carole.
For people who don't know or people who don't live in the UK, tell us about yourself and why are you here?
Oh gosh, I hate this question about who are you, what do you do? And I really should have this down to a T by now, but I started off in the IT industry about 22 years ago now.
Doing actual IT, and then I got a bit bored of doing it. So about 10 years ago, I started to write about it and talk about it as well.
In fact, one of my first jobs, Graham, was to interview you. No. Yes.
We're talking about Facebook terms and conditions and about how they were longer than the US Constitution.
I've been their sort of tech expert and tech consumer champion for the last 6 or 7 seasons or so, and Watchdog.
And I'm actually on telly this Friday night, which will be the 21st, with a show in Wales on the BBC called X-Ray.
And it's a photography special where I'm going to be talking about ownership of photos once you've uploaded them to social networks, how to use cloud storage safely.
So sort of consumer stuff on safe use of the cloud.
If you aren't in the UK, then there may be other ways to view it, but I couldn't possibly comment on those.
Getting ready to go off to Estonia next week is one of them, so I'll be away, but hopefully we'll be recording from there.
There was a very, very odd woman on it with bright red hair.
What we do every week is we look back over the last week's security news and we, well, talk about things which caught our attention.
You know, there can be just a little story which caught our attention. We have a chat about it. I'm going to go first this week and—
First of all, I just saw, just before the podcast started, I saw a story on The Hollywood Reporter, which claims that Russian President Vladimir Putin is being written out of new movies because the studios are worried that they might get hacked.
What?
And they've got Jennifer Lawrence, who's the hot young thing, to play the Russian spy. And there is a part in it which is Vladimir Putin's part, right, in the book.
But it appears that they're not— they don't want Vladimir in the story because, of course, you remember what happened with Sony.
With Sony being hacked, and many people thought it was North Korea doing it because they had a movie out which was making fun of their glorious leader.
I can't imagine why people would think such a thing, but that isn't what I want to talk about. What I actually wanted to talk about was this. MySpace has had another security snafu.
But actually, I think MySpace does continue. And there may, of course, be many people out there who might have created their accounts on MySpace back in its heyday.
And it may be long forgotten about it. You know, they may no longer have the email address which was associated when they created that account.
But what's come to light this time has not been a breach as such. It's not been like when they lost data, which has happened in the past and they've had big snafus like that.
What's happened here is a security researcher found a shocking security hole, which meant that anyone could seize control of somebody else's account just by knowing their name, their username, and their date of birth.
So if you went to that account recovery page, the page where you'd normally go if you couldn't remember your password, you know how normally you have to jump through lots of hoops?
Date of birth, well, anyone who's a dab hand at Google might well be able to find out your date of birth. And bam, you've gained access and control of the account.
So she privately informed them, said, "Guys, what about this?" Responsibly disclosed it to them, saying, "Look, yeah, okay." And what she heard back was a, "Thanks for contacting MySpace.
This is an automated response. We'll take a look at this and get back to you if we have any questions." And she waited and waited and waited.
And she thought after 3 months, this is a bit of a joke, isn't it? It's still there. People's accounts could still be being abused.
Maybe we should fix this. And sure enough, they've now taken down that recovery page and, you know, they put a proper process in place.
But my feeling about this is, okay, that's appalling. And that's sort of ghastly in many ways.
But maybe what we need to do is think about all of the websites where we might have created accounts way back in the Iron Age.
Everybody who's making that joke about MySpace should try and work out if they have a MySpace account and delete it. Just wipe it because you don't need it. You don't use MySpace.
Come on, let's be serious. And ensure you're not using the same passwords anywhere else on the net.
I've actually recommended that people try and do it once every Friday, go in and try and delete five accounts, and if you can do that, you'll probably get through within three or four months.
I realize over time you're going to forget things or no longer have access to email accounts or simply may forget.
The other thing you should do, of course, is sign up for services like Have I Been Pwned, the service run by Troy Hunt, which will inform you when a big data breach happens and whether your details have been included in it.
That's a good idea as well. But I just think, this really is horrendous, and there are too many websites making appalling mistakes like this.
So basically it was going into the ether.
So a good reminder for companies is to make sure the email address you have available on your pages for any problems or disclosures is up to date and monitored.
What have you got to tell us?
The first one that's hit this week is that the UK government is going to attempt to introduce age verification so that only those who are 18 and above can access websites that are hosting adult content.
Now, this is really complicated. I mean, there's a number of angles on this. On the one hand, look, I'm a parent.
Now, what they're proposing—
So you're thinking, okay, yep, that kind of works, I suppose.
Now, you don't need to tell me that there are a number of issues with this because let's face it, companies as a whole, but particularly those firms that host adult content, do not have a good track record of keeping people's details safe.
And we'll come on to one of those in a moment. But the fact is, if teenagers are determined to get hold of adult content, to browse it online, they will find a way to do it.
And there are any number of places that they will be able to go through, whether they're going through a VPN and going through a different country or whatever.
But it means that I don't see this actually being particularly effective for those who are most determined to look at stuff online.
There's lots of tools that parents— parental control tools that they can use on computers and devices and stuff, which can seem to me a better idea.
So this would affect all websites around the world, presumably, if they don't want to be fined. It's not just British porno websites.
So whoever my internet service provider is, yours, whatever, to then block the content from those websites if they are found to be in contravention of this age validation.
And UK's only got a number of months in order to do this. What is that, 9 months or so? There isn't a regulatory body in place for this yet.
So what is being mooted is the BBFC, the British Board of Film Classification.
That's the body that looks at cinema releases and film releases and so on and says, yep, that's a 15, yep, that's an 18. And it looks at pornographic content as part of that.
And it sounds as though it is going to be the body that has to enforce this, at least in some way.
So if I was little Timmy, for instance— well, not so little Timmy, but teenage Timmy— I would go and grab my mum's credit card from her purse, write down the number, and give it to all my mates, right?
And then—
So are they going to be stored? Is the idea that they wouldn't be storing these credit card details?
Or maybe they would be temporarily while they're looking at them to see if they're valid?
There's a lot that still needs to be sorted out, but there will have to be a record of a name and presumably an email address and a credit card number that is stored online.
And so those details will then be associated with accesses pornographic content. And that sort of data is, I would say, pretty hot stuff.
Finding some adult, you know, stash.
Speaking of large stores of personal information and credit card details and so on, almost exactly two years ago, many of us were very, very busy indeed covering the Ashley Madison data breach, which landed, I guess, first of all at the end of July and then at the end of August or so.
Two years later, Ashley Madison's owners are laying down what's looking like being an $11 million settlement to those who are suing the online purveyor of extramarital nookie.
They need to prove rather some material loss. And they're estimating that those who can may get as much as $3,500. But the fact is, I mean—
But Ashley Madison is still there if you want to do that stuff.
The following segment may be unsuitable for young ears. We did warn you earlier. I hope you were listening. Anyway, it's David McClelland's fault.
That's the important thing to remember. Not Carole or Graham. Thanks, and good luck. So on to my final piece now.
If Ashley Madison left its members wanting when it came to security, another provider of online services is trying a little bit harder. So a porn website—
It has the added benefit of not being on public show to the same extent that your fingers and fingerprints and that your iris, your eyes are as well.
But in the first instance, from what I could tell, it's actually just asking you to take a picture of it. There's no special sort of scanner or any special sort of technology.
In the press release, it talks about the fact that one of the identifying features of the male member is vein size. Oh God.
So this is all about surveillance cameras. And can you guess how many are around estimated in the UK or the US?
Exactly, there are— When you get to central London, that's gonna be super intense, isn't it?
So how frigging scary is it when we learned this week that a serious vulnerability in hundreds, if not thousands, of security camera models let alone any other IoT device, was uncovered by security researchers.
So let me tell you how this vulnerability came to light.
It's from a security firm called Senrio, and they found a stack buffer overflow vulnerability in the security camera model from Axis Communications, a manufacturer of these security cameras.
And they've dubbed this vulnerability Devil's Ivy.
So these security guys found that if attackers managed to access the vulnerable camera, they could take remote control of this video feed.
They could deny the admin or owner access to the video feed and they could prevent the admin from making any setting changes.
So this company, right, who produced this particular camera that Senrio tested confirmed that this Devil's Ivy vulnerability was present in 249 distinct camera models that they sell.
Only 3 old models are unaffected.
So we're still— this buffer overflow vulnerability is not Axis Communications code, but part of an open source code library, and it's called GSOP.
Now this is managed by another company called Genevia. So why I'm saying all this?
So just as a background, many developers, rather than writing code from scratch, will use trusted open source code libraries to speed up their coding.
It's a cut and paste job, right? Just speeds everything up.
One of the problems with coding libraries is it kind of, if they're popular, it can act like a homogeneous environment, right?
If the library is found vulnerable, the impact can be huge, impact lots of people. And that's exactly what's happening here with these security cameras, right?
There's an estimated 34 different companies that have developed IoT products with this vulnerable GSOP code. So how many IoT devices are impacted? We don't even know.
They thought, has someone already written this code?
So you might go grab, you know, it's a bit like themes for websites. I think it's just kind of, you know, it's a cut and paste, helps you just get on with the job.
And that Axis Communications immediately pushed out a firmware update to fix their security camera software.
It's a firmware update, and they pushed it out for all their models, all their vulnerable models.
And I have to give them a hat tip actually, because I love that they were really honest in the press about how they were vulnerable, that they immediately issued a fix, and they've been trying to push it out to all their users.
And also, the other good news is that often, security cameras— not all IoT devices, but security cameras are often behind firewalls and other security measures that make it more difficult for hackers to get access to.
So what you want to make sure is that your IoT device is not public-facing.
So if you can't access it from the outside world, you've made it harder for others to access from the outside world. However, there is some bad news here.
Because this vulnerability requires a firmware update, the fear is that a lot of manufacturers aren't going to bother pushing out an update.
One of the reasons is because you don't even know if the IoT device you possess is vulnerable or not, right? Unless your manufacturer tells you, you're not going to be aware.
So you can imagine how much information you might have to give to someone who's not technically very savvy on how they have to go about doing this.
It's— they may not have the infrastructure for sending out updates to different products.
I mean, it's appalling to hear, but there's still lots of IoT devices which you simply cannot update, right?
So I think if you are concerned, you should maybe contact the manufacturer with the model number of the IoT device you have and request to find out whether the vulnerable GSOP code is being used in this device.
You may or may not get an answer. Let's hope they do answer you because this is, I just find this really scary because I don't think anyone's going to be aware.
And these things are looking at us everywhere. I mean, they're everywhere.
Even cops, I just read this week, cops are going to be wearing body cams that now can do facial recognition. So that's good.
Would you allow these things into your house? Do you feel comfortable with them? Are we being old curmudgeons? Where do you stand on this kind of thing?
That makes me think straight away of probably open source's worst day, which was Heartbleed, which was the OpenSSL library, I think. And that of course is still an issue.
So there is some case history there, and I wonder how many of those devices that were affected there still remain unpatched, still haven't had the updated version of that library pushed down to them.
But in terms of devices lying around my house now, I'm not going to lie, I do have quite a few and I've got many more sitting on a shelf behind me.
I have a Nest Cam looking at me right now, one of those Google home security cameras. I've got a Ring doorbell downstairs, which I know has had people have cried out at that before.
And I've got some Amazon Echo and Echo Dot devices around the house.
So, I mean, it's kind of my job to live the life, to feel, to get a sense as to whether this technology can actually help us.
And as part of that, I guess it's to experience the ups and the downs with that.
So yeah, I think—okay, so at InfoSec Europe a couple of weeks ago, I was having conversations with some security vendors and particularly when it comes to IoT security, I was saying, well, look, why is there not a traffic light system we have on food?
When we go to the supermarket, we can see from a little symbol on the front whether it's high in sugar, whether it's high in salt, and so on.
Why is there not the equivalent for home webcams, for home microphones or home whatever else that gives us a sense, an independent sense as to how secure these devices are, whether they have had some independent testing against them, which means that they don't ship with default passwords that are well publicized and so on.
I think that'd be a great idea.
It's just struck home to me the obvious flaw there is that many of these, we don't know about the vulnerabilities until one, two, three years later when someone finds that vulnerability in a bit of code.
So we might be lured into a false sense of security saying, yep, this saw's green all around, I'm going to buy this webcam and stick it in my bedroom.
It also gives me—it made me think that maybe this is a reason to register warranties or whatever with manufacturers when you buy specific devices, if only to get the security informational update.
Because otherwise, you may not even know that this is the case, and your TV could be sitting there recording you the whole time through its little camera.
Maybe some of the manufacturers that you buy stuff, if you buy cheap, you may end up buying twice at the end of the day from a security point of view.
If it comes from a no-name Chinese device manufacturer, then the chances are they're not going to be as eager to get in touch with you as if you're buying from a big name.
I mean, my kids love some of the things that Alexa is able to do for them, and it makes my whole life a lot easier as well.
So I think it's important—I know this is a technology security podcast, but I think it's important to try and get a sense of balance as well, which I know you do.
Yeah, we love sponsors. Are you going to interrupt me?
They peruse the internet in its darkest corners and they work out what are the new emerging threats and vulnerabilities from the world of hacking and cybersecurity.
And then they bundle it all up. They wrap it up in a beautiful ribbon and send it to you in a free email.
And thanks to Recorded Future for supporting the show. Welcome back to the show. And before we wrap up today, we are going to— Pick of the week.
Yeah, we're going to have a little pick of the week. Don't make it like that dreadful documentary, The Red Pill, please. Let's have some better. What?
Maybe he'll slag off the one I'm about to recommend because having watched The Red Pill, I thought, oh, I need to see something good now.
And now I might have mentioned before, I'm a bit of a Doctor Who fan.
And there's been a bit of a to-do going on because of course there was the unveiling of the new Doctor Who, who is a woman. Yes, finally.
An alien time traveller can apparently be a woman as well as a man, which is fantastic news. I think it's terrific. And Jodie Whittaker won the job, which is super duper.
But one of the other people who was in the running was an actress called Phoebe Waller-Bridge. Oh, I love her.
And I was reading this, I was on the Doctor Who forums online, because everyone was trying to work out who's it going to be? Who's it going to be? Please don't be Chris Marshall.
And you kind of always know with Doctor Who, in the last few Doctor Whos, about 24 hours before the announcement, there is a sudden rush of betting for the person who ultimately gets it.
There must be a leak in Cardiff or something like that.
So we all kind of guessed, you know, although there was this female element, which was as to whether that would really, really happen, but we all kind of knew it was going to be Jodie.
But anyway, Phoebe Waller-Bridge, and I was curious, I thought, oh, what is she in? And it turns out she's been in this show, which I'm rather late to.
I'm sorry about this, but I've been catching it up on iPlayer, and I think it's also maybe streaming on Amazon Prime. It's called Fleabag.
And I thought, well, maybe I should watch it too, because my wife was going nuts about this last year as well. So I kind of felt as though I had a bit of catching up to do.
And I quite agree. I think she's fantastic. And not only does she play the lead in there, but she also, I think, executive produces. That's right.
She had a lot at stake with this show, and it seems to have paid off.
But I think maybe the fact that she isn't Doctor Who might mean that we get a second series of Fleabag one day, which I think I'd be very happy about. But it is — it's adult.
Let's point this out. It's possibly even more adult than David's segment on the show today.
And I have to say, there is a bit of darkness in my heart, which really was attracted to the bleak, grim nature of this show, because David, you're going to have to watch all six episodes because, oh my word, it just gets better and better.
So there's my recommendation. Go and check out Fleabag. Don't show it to your kids, but you might well enjoy it yourself. It was phenomenal, I thought. Yeah. David, what have you got?
So Mozilla, who we all know as veterans of the World Wide Web, have released a new podcast called IRL, In Real Life, in net speak, because online life is real life.
It's only launched a few weeks ago and it's two episodes in so far, but it's great.
And the two episodes have been, first of all, about how our data moves around online and the roles that so-called data brokers play in buying it, aggregating it, selling it, what happens when it goes wrong as well.
And that's, I mean, even for those of us who work in the industry, have various lenses onto the industry, it was fairly eye-opening.
And the other topic that they talked about was net neutrality. Massive topic that I know you guys discussed only a couple of weeks ago. And it's really good to listen to.
It's very energetic and it's produced very much like a kind of NPR radio feature, not the kind of conversational thing that we have. It feels a little bit faster paced than that.
Slicker. More professional. Less swearing. Perhaps less swearing. But yeah, so I think that's definitely worth a listen to.
And Veronica Belmont is again very much of an internet citizen. And yeah, I think it's great. And I think you will think it's great too. IRLpodcast.org.
And it's also on Spotify as well.
I agree with you, David. Great choice.
They just took it out of public view and they've been secretly working on it, squirreling away, working with other companies to try a brand new market.
So instead of focusing on individuals and selling it to us consumer types, they're going after industry.
Now that's kind of cool because you can think, I can think healthcare, think production floors, logistics, retail.
There are so many huge advantages to being able to use it in a work environment, getting information when you're very busy, just right there through your voice and being able to see it immediately while you're carrying on doing a task.
So what they're doing is they're using third parties to optimize the Google Glass for specific tasks or industries, and then it'll be sold by specialist companies.
So effectively, Google partners to specific industries or specific companies. Forrester say by 2025, there's going to be like 14.4 million US workers wearing smart glasses.
And I suspect actually that's underplaying it. I think if Google launched this correctly, I think it could be way higher than that.
The other cool thing I about this, even though I actually am not a big fan of the whole Google Glass on the street thing at all, because I'm curmudgeonly, David.
I don't know what you're talking about, Carole. I the idea that it's being touted as a business tool, right?
So apparently in test environments, they've had companies, lots of big companies testing this DHL, and they've been working on it, but then they and leave it in the office at the end of the day.
Now, yes, I know right now it's still a prototype, so maybe they weren't even allowed to take it out of the office, but maybe it'll just be left in the office, you know, in the ways that actually none of our devices today are, right?
But you see, the difference in what you're now suggesting, the Google Glasses, is it's oh, I'm doing this for my job, or I'm a dentist and that's why I have to wear these special glasses.
Whereas if you wear them yourself socially, people are going to snigger behind your back or punch you on the nose.
There was a massive hype, massive buzz around it, and a lot of latent desire until they finally did release it to developers.
And then it was a case of right, well, what does it actually do? And there were very few apps released for it.
So yeah, I think it was good technology, but it was released at a time before I think societally we were, and culturally, we were able to cope with it.
However, look at what Snap Inc. has done with its Snapchat Spectacles. They are a fashion device. They do one thing and they do it really quite well.
And a new line over the last day or so is that Snap is now selling its Snapchat Spectacles on Amazon. So they're likely to go mainstream.
Now, at the moment, if you're walking down the street or at the pub with some friends or something and you see someone wearing some Snapchat Spectacles, actually they get a lot of positive interest.
And I've been in this situation myself, that they are a little bit cool. And when someone is recording with the little LEDs on the front sort of spin around.
So you can tell, but they look quite cool, but they aren't trying to do everything. They're not trying to replace the whole mobile phone experience.
So I think that we will start to see smart glasses reappear not only into the enterprise and business, but also into more consumer applications.
But it's going to be a little bit more slowly, slowly, baby steps.
The other thing I urge you to have a look at is a Bloomberg report that they put out only a couple of days ago, I think, on Meta, which is an augmented reality set of spectacles.
And it was an interview with its boss there. And also, it showed how basically no one in the office is allowed to use a computer screen anymore.
They all have to wear these glasses for their work, even for their desktop work, for doing their emails and for doing their word processing and whatever else.
They have to wear these glasses. It looks a bit foolish to me.
I think that actually keyboards and mice are a pretty reasonable user interface rather than waving your hands about in thin air with no tactile feedback.
But I'll send you a link, Graham.
I think it's really interesting to look at it about we're seeing these glasses as being some sort of nirvana, but actually I think we have a middle ground to find with them.
And it was where people had implants that recorded everything that they see and said. And it allowed you to play back situations. They were called redos, I think.
So you could actually replay a situation. And then of course, it was Black Mirror, so it just seems—
I think that's why memory is selectively— It selects what you should remember and what will actually destroy you in the end if you remember it all the time.
David, where can people find out more about you or listen to your podcast? We know you're going to be on the TV on Friday and people can catch up on iPlayer as well.
Is there anywhere else where they should follow you online?
And just do a Google or your favorite search engine, others are available, for Fraculous Podcast, and you'll find us in all of the places there.
If you like the show, what should people do, Carole, if they like the podcast?
Email us if you're too shy to leave a public review, telling us what you like and what you don't like, and maybe we'll have a feedback episode soon as well. That could be fun.
Until next time then, cheerio, bye-bye. Bye. Bye-bye.
Further reading: Myspace fixes account security hole – but delete your account anyway.



