
Researchers have recently observed the Tinba v3 ‘Tiny Banker’ Trojan horse targeting banks located in Singapore.
Limor Kessem, a cybersecurity evangelist with IBM, provides more detail in a post on the Security Intelligence blog:
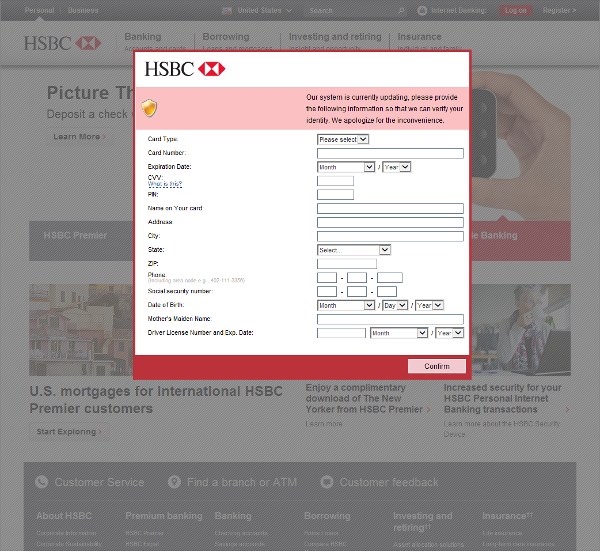
“IBM X-Force malware researchers have uncovered an aggressive malware campaign targeting banks in Asi. The campaign, which uses the Tinba v3 banking Trojan to infect potential victims, has its sights set on business and corporate accounts held with nine major bank brands in Singapore.”
Other countries, including Germany, Poland, and the United States, are also in the campaign’s crosshairs. However, Singapore accounts for more than one-third (36 percent) of the banks being targeted.

Tinba, also known as “Tiny Banker” on account of originally only being 20KB in size, was first discovered in the wild in mid-2012, notes Kessem in an earlier blog post.
At first, Tinba functioned as a classic banking trojan. David Fiser of security firm Avast describes how the malware would load onto a victim’s system via the Rig exploit kit. Tinba would then wait for the victim to visit a banking site, at which point in time it would relay the victim’s credit card information, address, Social Security Number, and even mother’s maiden name (if available) to the attackers.
But things changed in mid-2014 when the malware’s source code was leaked. This helped spawn at least two variations, Tinba v2 and Tinba v3, that function as fully independent trojans.
Since then, Tinba v3 has incorporated evasion and resilience techniques, including public key signing and a machine-dependent encryption layer, to prevent analysis, takedowns, and hijacking of the malware.
Armed with these new protective mechanisms, Tinba was observed by researchers earlier this year to be targeting Romania and Russia – two of the greatest computer crime centers in the world.
 “We do see other botnets target Russian [users], but [computer criminals] usually stay away from Russia [attacks] because the Russian government cracked down on people targeting their own citizens”, says Brett Stone-Gross, senior security researcher with Dell SecureWorks told Dark Reading.
“We do see other botnets target Russian [users], but [computer criminals] usually stay away from Russia [attacks] because the Russian government cracked down on people targeting their own citizens”, says Brett Stone-Gross, senior security researcher with Dell SecureWorks told Dark Reading.
Stone-Gross goes on to note that this might no longer be the case because of the Russia-Ukraine crisis, as reported by SC Magazine.
The IBM X-Force research team notes that Tinba is targeting the URLs of Singaporean trading sites, personal account credentials, and the credentials used to access Singapore’s principal credit bureau. What’s more, these attacks are only expected to expand across Southeast Asia.
To protect against Tinba and other trojans like it, users are urged to keep their browsers and plugins up-to-date, install a reputable ad-blocker, and disable extensions that are not frequently used. With these measures in place, hopefully users will go untouched by Tinba this holiday season.


