
Researchers have uncovered a cybercrime operation that spent close to a decade infecting targets with dozens of previously unknown malware variants.
Tomer Bar and Simon Conant of Palo Alto Networks explain in a blog post that they originally came across two emails containing malicious Microsoft Office documents back in May 2015.
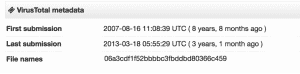
Since then, they have collected other emails containing hashes identical to those they identified in the emails they received last spring:
“Based on various attributes of these files and the functionality of the malware they install, we have identified and collected over 40 variants of a previously unpublished malware family we call Infy, which has been involved in attacks stretching back to 2007. Attacks using this tool were still active as of April 2016.”
Each Infy attack usually begins with a spear-phishing campaign containing malicious Word or PowerPoint documents.
In the case of the latter, the document opens in what appears to be a paused movie in “PowerPoint Show” mode. A dialog box then displays and asks the user if they would like to run the content. Clicking “Run” allows a multi-layer Self-Extracting Executable Archive (SFX) embedded in the document to execute.

Infy then loads up a DLL, writes to the autorun registry key, and waits to activate and connect to one of its command and control (C&C) servers after a reboot. At that time, it checks for antivirus before initializing a keylogger, stealing browser data, and sending all information to the C&C.
Following their initial analysis of Infy, Bar and Conant found that certain aspects of Infy, including parts of is C&C infrastructure, a tendency towards specific geographic targeting, and a single key used to encode strings, have been found across additional malware and attack campaigns.
Their findings have led them to believe that this particular malware family has been around for quite some time:
“Based on this specific encoding technique and key, we have identified related Infy samples from as early as mid 2007, although more frequent related activity is observed after 2011. Historic registration of the C2 domain associated with the oldest sample that we found, fastupdate[.]net, suggests that it may have been associated with malicious activity as far back as December 2004.”
Each of the malicious emails were sent from a Gmail account belonging to an Israeli victim. Analysis of C&C domains known to be associated with that email and similar accounts suggests that the malware might be originating from a source in Iran. The duo has reason to believe that Iran is using Infy to conduct a espionage campaign by which it is targeting governments and their citizens around the world.
Currently, the malicious Microsoft Office documents associated with Infy are flagged by 21/55 anti-virus providers on VirusTotal.
With that in mind, users can use the same-old common sense measures to protect themselves against this campaign. Don’t click on suspicious links or email attachments, and maintain an up-to-date anti-virus solution on your computers.



And yet we are told to use the security features in Windows to protect us. If they can't even protect their own code, how do we really believe that their security program is any better. Just another swinging door.
One of the issues with these pop-up boxes is that they can happen when you are typing something else (e.g. you switch to email while you are waiting for a page to load but the page loads a pop-up box requiring an answer while you are writing an email). In this situation you can inadvertently press OK to something because you expected to be typing into a different application at the time. Operating systems should be capable of locking down applications like web browsers to prevent them coming to the foreground if another application is already in the foreground.
lol @ security features in Win10?
Like, fully transparent desktop forwarding? sampling from input devices streamed offsite – including keyboard, mouse, joystick, microphone, webcam etc? – read/write access to the entire FilingSystem offered to third parties on demand? – ability to remotely adjust the system settings regardless of the user's intent? Sounds like the core of a good secure system to me.
If that's the malware they advertise, you really should be thinking about what they are hiding. Still yet to see someone publish the results of a firmware hash check of every component before and after install.
There is ability to hold windows in the foreground consistently above other windows – IF not, you really need a better window manager. Unfortunately, this "pop-up" behaviour is desired for a variety of applications.
Better solution is to prevent the browser opening "pop-ups". It can go in another tab or you don't really need it. Most of it isn't really needed. Ultimately, just stop navigating towards shady sites and you should never feature a single issue.
Even if you press "OK" it shouldn't be any significant issue as the broswer ideally shouldn't be able to gain sufficient priviliges to effect things outside of it's own scope. But that does kind of prequisite having a half sensible system to begin with. Preferably the browser would be containered. Worst case, restore from backup.
These type of attacks – like a disturbing % of successfull attacks – rely on two critical points;
– Someone is trusting(read: stupid) enough to download and execute the malware
– They are intentionally running software that is known exploitable – for some cases for the last decade plus
Those are two points that are easy to solve, too.