Things could have been so much worse.
Just before midnight UK time, the notorious Syrian Electronic Army (SEA) hacking group posted a message and screenshots which suggested they had hijacked Facebook’s domain name registration information, providing evidence of their achievement by tweeting a screenshot.

Happy Birthday Mark! Facebook.com owned by #SEA
And, it does appear that the hackers managed to change Facebook.com’s registrant contacts with ones pointing to Damascus, and a Gmail address under their control.
 However, one thing the pro-Assad hacking group undoubtedly would have liked to have happened wasn’t achieved. It doesn’t appear that the SEA managed to change Facebook’s DNS entries in such a way as to redirect them to a third-party site.
However, one thing the pro-Assad hacking group undoubtedly would have liked to have happened wasn’t achieved. It doesn’t appear that the SEA managed to change Facebook’s DNS entries in such a way as to redirect them to a third-party site.
That’s what the Syrian hackers *did* manage to do recently with PayPal UK and eBay UK, both of which suddenly started to display an offensive anti-American message and a binary depiction of the Syrian flag recently.
And, if the SEA had managed to hijack Facebook’s DNS settings in that way they could have potentially pointed millions of Facebook users towards a website which could have infected them with malware, stolen their login information, or (at best) displayed an offensive or mischievous message.
Fortunately, that didn’t happen.
One assumes that Facebook was fortunate enough to have its DNS records sufficiently protected that further authentication was required before anyone could change that crucial information.
But how was information still changed in Facebook’s WHOIS information (albeit only briefly)?
Well, a clue comes from the Syrian Electronic Army themselves who tweeted a screenshot of what appears to be a MarkMonitor administration panel, showing Facebook in a list of websites.

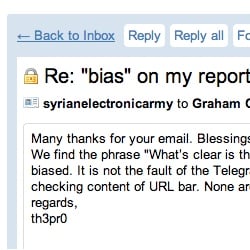
MarkMonitor is responsible for maintaining Facebook’s internet domain registration. And it looks like the SEA hackers have managed to burrow their way into MarkMonitor’s systems.
Fortunately, MarkMonitor quickly regained control, restored Facebook’s domain registrant information to the correct contacts, and closed down the offending admin panel preventing (at least for now) further exploitation.

All in all – a lucky escape for Facebook, which is celebrating its tenth birthday this week.
Even though MarkMonitor appears to have responded rapidly, and a potential online disaster was averted, serious questions will need to be asked about how well the company has been securing access to its admin panel.
One imagines that MarkMonitor will be having a difficult call with Facebook’s IT team later today.
After all, the Syrian Electronic Army’s hack of MarkMonitor put them within a hair’s breadth of hijacking Facebook’s domain.
If you are on Facebook, and want to be kept updated with news about security and privacy risks, and tips on how to protect yourself online, join the Graham Cluley Security News Facebook page.
See also: When Syrian hackers attacked, Facebook’s bacon was saved by security measures