CAROLE THERIAULT
Do people put their phones in bags if they're going up in a balloon?
CAROLE THERIAULT
That's full of helium, isn't it?
MARK STOCKLEY
Well, I think if you're up in a balloon and the helium's not staying in the balloon, then you're in bigger trouble than losing control of your iPhone.
CAROLE THERIAULT
Good, good point, Mark. Thanks.
Unknown
Smashing Security, episode 103: An Instagram Nightmare, Crazy iPhone Deaths, and Election Ransomware claims with Carole Theriault and Graham Cluley.
Hello, hello, and welcome to Smashing Security episode 103. My name is Graham Cluley.
CAROLE THERIAULT
I'm Carole Theriault.
GRAHAM CLULEY
Hello, Carole.
CAROLE THERIAULT
Hi. It sounded like your voice almost broke there.
MARK STOCKLEY
About time.
GRAHAM CLULEY
Puberty finally happened a while ago, Carole. We're joined, you may have just heard him, by a special guest. He's new to the show. It's Mark Stockley. Hello, Mark.
GRAHAM CLULEY
For people who don't know you, why are you here and who are you?
CAROLE THERIAULT
Wow, that's been hard.
GRAHAM CLULEY
Don't answer that.
CAROLE THERIAULT
I'll answer that.
MARK STOCKLEY
So this is the softball you promised me to start with, is it? What the fuck are you doing on my podcast? I don't know.
CAROLE THERIAULT
As you can tell, Graham and I have known Mark for a long, long time. Mark is a writer for Naked Security. He's also pretty au fait with all things internet and technical.
GRAHAM CLULEY
He's Naked Security's backend guru, I think you could say as well, couldn't you, Mark?
MARK STOCKLEY
Well, but mostly it's nepotism, right?
GRAHAM CLULEY
Yeah, mostly that's why you're here.
GRAHAM CLULEY
And just to put the show in context, we are coming to you from the past. We recorded this on election day. By the time you hear this, the election will all be over.
Everything will be marvellous. Whatever the result, everyone's going to be happy with it, I'm sure.
CAROLE THERIAULT
Now, which of you have set your VPN to USA so you can sniff out the real election news and vibe?
MARK STOCKLEY
Well, I'll just be going straight to Alex Jones on tour. Just go straight to the truth, just Google it, Carole. The truth's out there, you've just got to Google it.
GRAHAM CLULEY
Smashing Security is this week sponsored by the marvellous folks at LastPass.
LastPass allows you to protect all of your passwords across all of your devices, whether they be laptops, desktops, or smartphones.
And if you're an enterprise, you should really run a password manager as well, because you can defend your employees and put in place password best practices.
Make sure to give them a try. Visit lastpass.com/smashing, and thanks to LastPass for supporting the show.
CAROLE THERIAULT
Okay, quiz time, quiz time. All right. What percentage of data breaches originate from email?
GRAHAM CLULEY
Ooh, 7 out of 10.
CAROLE THERIAULT
Ha! It's a pretty good guess, but you're way wrong. 96%. Oh, blimey.
And one of the big things that companies have to worry about is phishing scams, because that's the kind of way that hackers and other baddies break into your company.
GRAHAM CLULEY
Because that's how they get your passwords.
CAROLE THERIAULT
That's how they get your passwords. So MetaCompliance make it easier to train and prepare your whole environment to stop these kind of attacks.
They have information on phishing and cybersecurity and policy and privacy and incident management. There's all kinds of training out there.
Smashing Security listeners, you guys can get 10% off by visiting smashingsecurity.com/metacompliance. That's smashingsecurity.com/metacompliance.
GRAHAM CLULEY
And on with the show. Now, you chaps, are you familiar with Kylie Jenner?
CAROLE THERIAULT
Familiar? Define familiar.
GRAHAM CLULEY
Have you heard of her? Do you know who she is?
MARK STOCKLEY
Is she a Kardashian?
GRAHAM CLULEY
Oh, well, she's somehow related to the Kardashian family.
She is, according to Wikipedia, because I've been looking up all about her, a 21-year-old American model, entrepreneur, socialite, and social media personality.
CAROLE THERIAULT
Okay, that means that she grew up rich.
GRAHAM CLULEY
Well, I think—
MARK STOCKLEY
Carole, she's a socialite.
CAROLE THERIAULT
Exactly.
MARK STOCKLEY
Nothing says fame earned like socialite.
GRAHAM CLULEY
She may still be quite young, but she's squeezed a lot into her life. She's been on a hit reality TV show, Keeping Up with the Kardashians, since she was about 10 years old.
She's launched her own line of clothing and cosmetics, and she's co-authored a dystopian science fiction novel about two twin girls who live in a biosphere.
CAROLE THERIAULT
Have you read it?
GRAHAM CLULEY
I have not. No, she's not. There's a lot of books I have to read, Carole, and I haven't got to that one.
CAROLE THERIAULT
You haven't got to Kylie Jenner's twin girls who live in a biosphere?
MARK STOCKLEY
Where have you got to yet?
GRAHAM CLULEY
I've got sort of to Kipper and Chip, the Red Book one.
Now, in the August 2018 issue of Forbes magazine, Kylie Jenner was predicted to become the youngest self-made billionaire ever.
Clearly they're using some definition of the words self-made that I was previously unaware of.
MARK STOCKLEY
It's not very well known that she produced and directed Keeping Up with the Kardashians when she was 10. Oh, so well earned, I think.
GRAHAM CLULEY
But what she has done is she has earned herself 118.6 million followers on Instagram, and there are brands out there who will pay her as much as $1 million to post something about their products on Instagram.
GRAHAM CLULEY
It's a lot of money, isn't it? It's quite a great deal.
CAROLE THERIAULT
That must really screw up your whole sense of life if basically someone's willing to give you a million quid for you to just say, hey, like these crisps.
GRAHAM CLULEY
If that's screwing up your sense of life, Carole, please screw me. Because that's—
CAROLE THERIAULT
Whoa, whoa, whoa. It's not that type of show.
GRAHAM CLULEY
It sounds pretty fantastic to me.
MARK STOCKLEY
I'm not promising anything.
GRAHAM CLULEY
If Snapchat wants to take a photograph of me wearing their daft goggles.
CAROLE THERIAULT
You don't think you'd become really cynical and you'd start throwing your weight around going, well, why would I talk about that? I don't love that.
I don't know what we're gonna do for me.
GRAHAM CLULEY
Well, you can, no, it's a deal, right? You can post up vacuous photographs of yourself pouting on some beach somewhere.
And occasionally, if you need a bit of cash to buy some ice creams or a hot dog, you do something for an ad. Why not? It sounds terrific.
If people are prepared to pay for it, if you've amassed that following with your snaps, sounds wonderful to me.
And I think there's many people, other people see this going on and they're tempted to see if they can make a ton of cash as well doing something else, which appears to be so bloody easy, right?
CAROLE THERIAULT
Well, I think it's gross, but okay, carry on.
GRAHAM CLULEY
Anyway, like I said, other people want to do this. They'd love to post a couple of times a day on Instagram, make themselves a fortune.
CAROLE THERIAULT
People like you. I would. Well, I'm just thinking she's setting herself up for Nicole McCauley. What's his name? Macaulay Culkin. Macauley. Macauley. Macauley.
MARK STOCKLEY
Yeah, no, that's his name now. That's his name now.
GRAHAM CLULEY
McLearn Culkin.
MARK STOCKLEY
Macaulay Culkin.
CAROLE THERIAULT
What? I know nothing of celebrity world.
GRAHAM CLULEY
Crow, not only do you know nothing about celebrity world, you're referring to child actors from like 30 years ago. I mean, he's a grown man, Macaulay Culkin.
CAROLE THERIAULT
Yeah, but that came out after, like it wasn't a movie that was I'm sure I've seen it, but anyway.
GRAHAM CLULEY
Can I get to the security aspect of this story?
MARK STOCKLEY
Is this even about Kylie Jenner? What's she done?
GRAHAM CLULEY
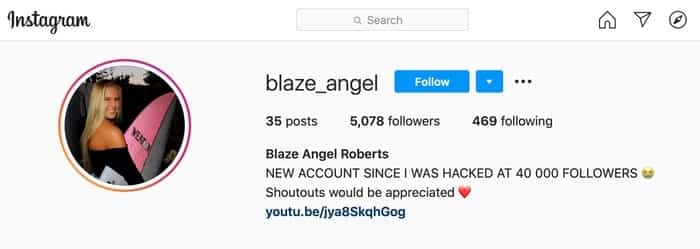
So lots of people are impressed by the likes of Kylie making themselves a fortune on Instagram, including an Abu Dhabi-based travel blogger called Maria Da Costa.
GRAHAM CLULEY
And she lives in the capital city of the United Arab Emirates with her husband Jackson, and they spend their free time traveling around the place, blogging about their adventures, and they claim to have visited 42 countries and over 127 cities in 6 continents.
CAROLE THERIAULT
6 continents?
GRAHAM CLULEY
That's what they say.
GRAHAM CLULEY
Over several years, they've amassed 105,000 followers, which—
CAROLE THERIAULT
That's not bad.
GRAHAM CLULEY
It's not bad.
MARK STOCKLEY
It's almost—
CAROLE THERIAULT
It's the same ballpark.
GRAHAM CLULEY
It's, well, not really, but—
CAROLE THERIAULT
118 million versus 105,000.
MARK STOCKLEY
Well, come on. Where do we sit in terms of judgment on this? Because, you know, we were all pretty scathing about Kylie Jenner for her not working very hard for her Instagram fame.
So what do we actually— you guys, you know, professional podcasters, where's the food chain here? Are we okay with travel bloggers?
GRAHAM CLULEY
Well, I've only created an Instagram account for myself this morning in order to research this story.
CAROLE THERIAULT
I've never had one. I know nothing.
GRAHAM CLULEY
Anyway, listen, I'm not criticizing Delaine and her husband Jackson for being on Instagram, or even Kylie Jenner. Why shouldn't she?
MARK STOCKLEY
Yeah, no, that's good. 'Cause it sounded like that.
GRAHAM CLULEY
Okay. But 105,000 followers potentially made them a bit of a target.
Delaine received out of the blue an email claiming to come from someone called Angelina Reshetnikova, who said that they were representing an online store called Vince.
And they wanted Delaine to be the new face of Vince. And they said, if you give us a slight reduction on a promotional post, you can choose one of our outfits.
CAROLE THERIAULT
So they basically Kylie Jenner'd her by basically treating her like a celebrity.
GRAHAM CLULEY
105,000 followers.
CAROLE THERIAULT
Is that significant?
GRAHAM CLULEY
It's not bad, is it? You might want to—
CAROLE THERIAULT
I don't know what's bad.
GRAHAM CLULEY
So I'm sure there are brands and hotels who have offered her maybe cheaper stays or free trips in order to promote them to her followers.
CAROLE THERIAULT
Right. So she's probably getting these kind of things. And this was just one another invite in her inbox.
MARK STOCKLEY
Yeah. So she received an unsolicited email from a Russian-sounding woman.
GRAHAM CLULEY
There's nothing wrong with Russian-sounding women, personally.
MARK STOCKLEY
I just want to clarify the details.
CAROLE THERIAULT
Yeah, Mark.
MARK STOCKLEY
You know, it's a Russian— she got an email from a Russian-sounding woman. This all sounds fine. Everything's going to work out.
GRAHAM CLULEY
Representing—
GRAHAM CLULEY
Representing an online store called Vince. And they were making an inquiry saying, what's the cost to advertise on your page? And what discounts can you offer us?
And can we offer you one of our items of clothing from our new collection as a gift? And please click on the link. And the link appeared to go to Instagram.
And so, of course, Delaine, our blogger, clicked on the link.
CAROLE THERIAULT
And she's au fait with Instagram, having a number of followers there.
GRAHAM CLULEY
And she was taken to a page which asked her for a username and password, and dun dun dun! You can probably guess what happened next.
It was, of course, a phishing link, and she had just given her password to this hacker.
And she received an email from the bad guys who are posting to her from an anonymous webmail account at tutanota@ saying, "We've hacked your Instagram account and we are going to start deleting your posts and your images." That, you know, basically we've set a countdown and you've only got 1 hour before your account is going to be deleted and you're going to lose all your photos.
And they asked for $400 worth of bitcoin.
CAROLE THERIAULT
So they sent her a link. She went to a fake Instagram site. She entered her username and passwords.
Bad guys grabbed it and then changed it and said, "Aha, we have all your pictures and we're going to delete them unless you give us some money." Right.
GRAHAM CLULEY
And so Delaine Costa got into a conversation with these guys. "Oh, I wanted my account back, you know, can we talk about this?" And all the rest of it.
And there was a bit of toing and froing and delay. And he says, "Oh, I couldn't sleep that night and I was crying." And Jackson, her husband, he sounds like a wonderful guy.
He agreed to pay the following day.
And so they started up a conversation, said, "Look, we can't do $400." And the bad guy said, "Well, how about $200 instead?" And so Jackson tried to send the money.
GRAHAM CLULEY
But the money didn't go through. Oh, it failed. Something went wrong. Maybe she wasn't able to handle the whole bitcoin thing. Didn't happen. And that made the hacker furious.
CAROLE THERIAULT
They were tasting the riches at the tip of their tongue and it was snatched away.
GRAHAM CLULEY
And they kept on messaging, asking, you know, when are you gonna pay? When are you gonna pay? And after 3 days, they'd finally had enough.
They said, right, that's it, we're gonna delete your account and goodbye. And that was the last conversation they had and the account was wiped, zapped.
Now, at this point, Delaine got really, really frustrated. How does she report this to Instagram?
There is a method of reporting hacks to Instagram, but you have to be logged into an account to report that an account has been—
CAROLE THERIAULT
Yeah, why is it these sites don't have 1-800 numbers? I mean, you'd think big sites like this would.
MARK STOCKLEY
Well, you know what the answer to that is.
CAROLE THERIAULT
Yes, I know, but they should.
MARK STOCKLEY
People would phone the number.
GRAHAM CLULEY
That's why. That would be disastrous.
I mean, I receive emails every day from people who claim to have been locked out of a Facebook account or need help hacking into their loved one's account because he's gone missing, or find out what my girlfriend's up to, and these sort of things.
So if people are contacting me, people must be trying to contact Facebook with these sort of scam messages all the time as well.
So how on earth would they wade their way through them?
Well, there is a helpline number for Instagram which Delaine managed to find, and she rang them up and they said, no, no, no, no, no, you have to contact us through the app.
And she felt frustrated because her username and phone number and email ID didn't exist on Instagram anymore via any particular service.
CAROLE THERIAULT
But surely someone could look at a log and go, oh, I see what's happened. Oh, interesting. Everything you say checks out.
GRAHAM CLULEY
What's in it for Instagram to provide that kind of service from there?
CAROLE THERIAULT
Yeah, why should they have support? Absolutely.
CAROLE THERIAULT
They shouldn't even bother with customer service.
GRAHAM CLULEY
Why should they?
CAROLE THERIAULT
Fuck the users.
GRAHAM CLULEY
Right, right. Yeah. If you love Instagram that much, just create another account and off you go.
MARK STOCKLEY
It is just, it is, if you think about the number of users involved, it is terrifying when you think about how many users you could royally piss off if you were Instagram and just write it off, or whether you're Facebook or Apple or anybody like that.
You know, you can probably afford to make hundreds of thousands of users absolutely hate you. And actually it's kind of a rounding error.
GRAHAM CLULEY
So Delaine is saying the hack reporting option is fundamentally flawed because it doesn't help anyone who's actually lost complete access to their account.
And eventually Instagram sent her an email saying, look, what you need to do is submit a photograph of yourself carrying a placard with your name on it and a code number and a shoe on your head or something like that.
CAROLE THERIAULT
How weird.
MARK STOCKLEY
We want you to stand on one leg holding an ironing board. Smoking a cigarette.
GRAHAM CLULEY
And she sent them this and apparently this kept on going on for days and they kept on saying, well, what device did you use to register your account?
And she's like, I don't remember. It was freaking 2012. I don't remember what phone I had or what my number was or what the code. And she just said it was absolutely no use at all.
Eventually she says that she found a savior and she says she's not in a position to name them.
Someone helped her, whether that was inside Instagram or not, I don't know, but her account got restored.
CAROLE THERIAULT
Oh, interesting.
MARK STOCKLEY
I've heard that kind of story before.
We published a story last year or the year before about Twitter where somebody was being really awfully harassed on Twitter and they couldn't make any headway.
And it's only at the point that they managed to contact somebody who works for Twitter, they contacted them outside the normal methods, that they actually managed to make some progress.
And that's not an unfamiliar turn of events.
GRAHAM CLULEY
It's not at all.
In my own experience, I found sometimes it's been impossible to get some of these social media sites to respond to you unless you approach their PR department or unless you actually kick up a stink in the press.
I had a situation once where I was being harassed online and unpleasant things were being threatened against me, and I went to The Register and The Register wrote it up and suddenly Facebook took action.
But prior to that, it was impossible to get any response from them.
So if you can't find someone or if you're not— I imagine that Kylie Jenner wouldn't have any difficulty because she's a celebrity.
CAROLE THERIAULT
Oh, that's— I was just gonna ask, what the heck does any of this have to do with Kylie Jenner?
And your link, your tangential link, is she wouldn't have any trouble because she's famous.
GRAHAM CLULEY
And she's on Instagram. No, I'm just saying.
CAROLE THERIAULT
And you get to lead with the story. So have you heard of clickjacking? Podjacking? Have you heard of that?
MARK STOCKLEY
I think what Graham's trying to say, Carole, is that Kylie Jenner is like Graham.
CAROLE THERIAULT
Exactly. This is the message.
MARK STOCKLEY
She's famous like Graham. She has resources at her disposal to deal with these sorts of issues.
CAROLE THERIAULT
Mere mortals like you and I.
MARK STOCKLEY
Normal people like travel bloggers and people like that.
GRAHAM CLULEY
And I would like to take this opportunity to promote my new line of nail varnish, which I am—
CAROLE THERIAULT
Porcine Pink?
MARK STOCKLEY
That's an interesting choice for a podcaster.
GRAHAM CLULEY
Now, obviously, keep backups of your pictures. Don't just trust them to Instagram. In this case, there was a happy ending, but in many cases, that doesn't happen.
We've seen many higher profile and celebrity accounts on Instagram being hacked.
And I think one of the challenges is that Instagram was rather late embracing two-factor authentication. They brought it in for the first time last year in 2017.
It took until August this year for them to finally add support for third-party two-factor authentication.
MARK STOCKLEY
Do you really think that would have helped here?
GRAHAM CLULEY
I actually think it probably would have done. I think—
GRAHAM CLULEY
Yeah, I do.
MARK STOCKLEY
Because I hear this story and I hear password manager. I don't hear 2FA.
Look, I know about web development and stuff like that, but if I was going to set up a phishing site, I would just have a little field for you to type in your two-factor code, and then I would immediately pipe all the information that you've put in straight into Instagram.
GRAHAM CLULEY
Well, you can do that.
MARK STOCKLEY
And I would log in as you and I would change the information because two-factor, you normally get a sort of 30-second to a minute.
GRAHAM CLULEY
Well, you can do that, Mark. You're right. But remember, you are a nerdy backend guru, right? Who knows how to create web pages and things like that.
CAROLE THERIAULT
I'm sorry, Mark. I thought this was a good idea.
MARK STOCKLEY
A naked security backend guru.
GRAHAM CLULEY
Any kind of additional authentication will cut out an awful lot of the phishing going on.
I have to say though, when I was writing up this story, I had to create an Instagram account and I can't get two-factor authentication enabled and I'm not a complete newbie.
CAROLE THERIAULT
Maybe you should ask Mark. He's a geek. He's on Instagram.
MARK STOCKLEY
So can I just make a plug for password managers here? 'Cause you, I agree with you. 2FA is undoubtedly a good thing and there's lots of reasons why it's a great idea.
In this case, maybe it would have helped, but there are ways that the phishing could have been set up so that it didn't.
But if you had a password manager that automatically enters your password for you, when you go to a website, if you go to the wrong website, no matter how good the replica is, if it's not the right website, the password manager isn't going to autofill your password.
And for someone like me who lets the password manager pick the password, that essentially means you can't get in.
GRAHAM CLULEY
Yes, a great additional reason why everyone should be running a password manager.
CAROLE THERIAULT
So now that you have an Instagram account, Graham, what are you doing with it?
GRAHAM CLULEY
Well, I've only got—
MARK STOCKLEY
Are you selling nail varnishes?
CAROLE THERIAULT
Oh yeah.
GRAHAM CLULEY
Mark, what story have you got for us this week?
MARK STOCKLEY
So my story is a mystery. So I want you to get into character.
GRAHAM CLULEY
Can I be Columbo?
MARK STOCKLEY
I want you to forget that you're Graham and Carole for a second. You are Agents Fox Cluley and Dana Theriault of The X-Files.
And if Fox Cluley sounds a bit like Columbo, then that's just a cross we're all gonna have to bear.
GRAHAM CLULEY
Okay, I like it.
MARK STOCKLEY
So listen in as I tell you the mysterious tale of the hospital. Where all the iPhones died.
So the incident in question is said to have occurred about a month ago in a multi-practice facility of Morris Hospital, which is near Chicago.
MARK STOCKLEY
So towards the end of an otherwise normal day, the IT department gets a call from a facility saying that all of its mobile phones have died.
MARK STOCKLEY
And so they dispatch a team out there to investigate.
So when they get to the facility, the team discover that the call hadn't been quite correct, which is not uncommon with IT support calls.
GRAHAM CLULEY
Did they try turning it on and off again? That's normally the fix.
MARK STOCKLEY
I'm glad you enjoyed the story. So it turns out it wasn't all of the mobiles that were down. It was only the iDevices.
GRAHAM CLULEY
iPhones and iPads.
CAROLE THERIAULT
It seemed an Apple shoe.
MARK STOCKLEY
Before you said, I didn't want an Apple shoe until you said Apple shoe. And now I really want an Apple shoe.
So most of the iPhones and the Apple Watches belonging to about 40 users on multiple floors in this facility had died stone dead.
MARK STOCKLEY
Those that were alive were experiencing problems with their cell radios, so they couldn't connect to the cellular network, or mobile network for us UKers.
So they couldn't connect to the mobile network, but they couldn't connect to Wi-Fi. But most of them were just dead.
MARK STOCKLEY
And everything else was fine. So the Androids and the computer systems in the rest of the facility were all fine.
GRAHAM CLULEY
This is some kind of targeted denial of service attack by some rabid Android fan.
MARK STOCKLEY
Graham's already decided who the culprit is.
CAROLE THERIAULT
Yeah, he normally speculates very early.
MARK STOCKLEY
This is how police work works, isn't it? I think I know who did it.
GRAHAM CLULEY
Wait, that's what happens in Columbo. You find out who the baddie is at the beginning, and then you just keep on chatting to them, and eventually you're out with them.
See, it wasn't raining that night, was it?
CAROLE THERIAULT
Why do you have water on your jacket then? I just don't understand.
MARK STOCKLEY
You've got water on your eyeshoe.
GRAHAM CLULEY
You took your jacket with you, but it was 10 past 10. So you're an identical twin?
CAROLE THERIAULT
My wife!
GRAHAM CLULEY
Love Columbo. Bless him.
CAROLE THERIAULT
How can you not? Yeah. Okay. But we digress.
GRAHAM CLULEY
Do we? Can we not carry on talking about Columbo?
CAROLE THERIAULT
No, I want to know what happens. I'm interested.
MARK STOCKLEY
Okay. So returning to our theme of the IT help desk, as any IT help desk person will tell you, the first question you need to ask is what changed today?
Well, what had changed was that they were having a new MRI machine installed. Okay. So case solved, right? MRI, it's a giant superconducting electromagnet.
CAROLE THERIAULT
Exactly. That's what I'm thinking.
MARK STOCKLEY
Magnets and electronics don't play very well together. And so it seems pretty obvious what the answer would be.
GRAHAM CLULEY
And when you get an MRI, the first thing you want to do is go on, let me have a go in the MRI. Everyone lines up and they—
CAROLE THERIAULT
Oh yeah, because it's so fun. I've had the joy of having a number of MRIs in my life and they are fun times.
GRAHAM CLULEY
They forget to take the phone out of their pocket or whatever and it got zapped.
MARK STOCKLEY
So do you think 40 people all lined up and went through the MRI for fun?
And then when the IT guy gets there, he's going, "Has anybody been playing in the new MRI?" And 40 people all looked at each other and went, "Eh, no, no." I think that's probably what happened.
GRAHAM CLULEY
It's probably more plausible than whatever you're going to tell us.
MARK STOCKLEY
So, case solved, right? It's an MRI, great big superconducting electromagnet, magnets and electronics don't play well together.
So it seems pretty obvious what the answer would be, but remember, this only affected the iPhones. It didn't affect any of the other computer systems or Android devices.
CAROLE THERIAULT
Yes, I forgot that. Okay.
GRAHAM CLULEY
Now, the Android users were too busy trying to get their carrier to deliver a security update and on the phone to Samsung or Huawei trying to sort that out, whereas the Apple users had loads of free time.
They're oh yeah, let's go check out the MRI. Okay, carry on. Tell us what happened, Mark.
MARK STOCKLEY
You're a Columbo fan and you're hurry up, why is this moving so slowly?
CAROLE THERIAULT
He doesn't shut up and then yells at you for hurrying up. I know. He got bored with himself.
MARK STOCKLEY
What are you when you're watching Columbo? Okay, I'm going to return. I'm going to return to the story. So not so fast.
As any physicist can tell you, magnetism is rare in the natural world in that it doesn't have a strong preference for Apple products.
So nobody actually knows what the answer to this is. The devices that were—
GRAHAM CLULEY
Satisfying story.
CAROLE THERIAULT
Are you serious? Seriously, we don't have a reason?
MARK STOCKLEY
I'm just— my word. Are you a Columbo fan as well? Right. So nobody knows what the answer is. The devices that were bricked were private.
So the technician got to look at them briefly, but hasn't been able to take them apart. But everybody's best guess is that this is all about helium.
So it transpires that during the installation of the MRI, It sprung a leak, and about 120 litres of liquid helium evaporated into the air.
CAROLE THERIAULT
Everyone's talking this! My phone doesn't work! My phone doesn't work!
MARK STOCKLEY
We've no idea what's going on.
GRAHAM CLULEY
Did you know Maria was on the show this week?
CAROLE THERIAULT
Is that what happens if there's a huge leak of helium? What's going on? Why are you sounding funny?
MARK STOCKLEY
When they got there and they say, has anybody been playing with the MRI? Everybody looked at Maria and went—
MARK STOCKLEY
So, right, so we've got the means and the opportunity, but what's the motive? What's helium got against Apple?
CAROLE THERIAULT
Ooh. No idea. Could I call a physicist?
GRAHAM CLULEY
Can helium get into the devices more easily?
CAROLE THERIAULT
Oh. Small, yes, small molecules?
GRAHAM CLULEY
Through the headphone jack?
MARK STOCKLEY
So it seems so. You're actually both barking up the right tree, it seems so. It seems that helium can induce the electronic equivalent of a heart attack in an iPhone.
So in the heart of every computer, there's a very, very, very, very, very tiny clock that keeps a kind of heartbeat going.
So you've probably heard about quartz clocks, quartz oscillators, things that. Well, iPhones don't use quartz. They use something called a MEMS oscillator.
And a MEMS oscillator is a really tiny machine etched out of silicon a silicon chip. But instead of electronics, it's mechanics. Okay?
And the oscillators used in iPhones are billed as the world's smallest, lowest-power 32 kHz oscillator.
MARK STOCKLEY
And in the world of phones, small is beautiful unless there's helium around.
Because as you were saying, Carole, helium is very difficult to keep out, and the molecules are small enough that they can actually gum up the parts of a MEMS oscillator.
CAROLE THERIAULT
Interesting.
MARK STOCKLEY
There is one final important fact that I need to tell you about this story. And that is that it originally appeared on Reddit.
So there is a non-zero chance that this is actually all complete horseshit.
CAROLE THERIAULT
No, it didn't originate on Reddit. Originated on Reddit?
MARK STOCKLEY
No, the story was reported on /r/sysadmin.
GRAHAM CLULEY
So someone went onto Reddit and said, this happened to us the other day.
MARK STOCKLEY
I have read the iPhone user guide and it says helium's bad for iPhones.
CAROLE THERIAULT
I believe everything I read on Reddit. Everything.
MARK STOCKLEY
I think the big question mark is around the concentration of helium, because 120 litres of liquid helium expands about 750 times.
CAROLE THERIAULT
Someone did their research.
GRAHAM CLULEY
Yeah, this is general knowledge, Carole.
MARK STOCKLEY
And then you disperse that through the atmosphere in the hospital.
You know, in response to this Reddit post, people have been doing tests with iPhones, putting iPhones in sealed bags of helium and things like this to see if it really does happen.
And yes, I mean, if you put an iPhone in an environment rich in helium, then it dies.
But the question is, in terms of the story, the plausibility of the story is what concentration of helium would actually damage an iPhone?
CAROLE THERIAULT
I just wonder. I think if I worked there, I'd be really pissed off and I would want a replacement for my personal phone.
MARK STOCKLEY
Yeah, they're all getting replacements from the company. Yeah, it's my understanding.
CAROLE THERIAULT
But, you know, interesting. Anyone who works with helium. So clowns, right?
CAROLE THERIAULT
Right. MRI machines. What else? Who else works with helium?
MARK STOCKLEY
Richard Branson.
CAROLE THERIAULT
Yes. Do people put their phones in bags if they're going up in a balloon?
CAROLE THERIAULT
That's full of helium, isn't it?
MARK STOCKLEY
Well, I think if you're up in a balloon and the helium's not staying in the balloon, then you're in bigger trouble than losing control of your iPhone.
CAROLE THERIAULT
Good. Good point, Mark. Thanks.
GRAHAM CLULEY
I don't think hot air balloons have helium in them, just to be—
CAROLE THERIAULT
They just have hot air.
GRAHAM CLULEY
Yeah, it's just heat. It's just a heater, isn't it?
CAROLE THERIAULT
Maybe what it might— a zeppelin then.
GRAHAM CLULEY
Yeah, a zeppelin or Branson, one of Branson's kind of things.
CAROLE THERIAULT
That's true. That's true. That's true.
GRAHAM CLULEY
Sorry to be slightly—
CAROLE THERIAULT
No, no, no, I think it's fair. It's my own happiness. Yeah.
GRAHAM CLULEY
Carole, what's your story for us this week?
CAROLE THERIAULT
We have to hand it to Trump. In all the political craziness in the last few years, there is one thing he's done that's been pretty amazing. Can you guess what it is?
GRAHAM CLULEY
No, I'm struggling.
CAROLE THERIAULT
Really? Well, don't you think he was able to get a zillion people to care about politics, motivating the political spirit? OK, get this.
MARK STOCKLEY
As of last night, I've run over your dog. I've proved you love your dog. See, I've done you a favour.
CAROLE THERIAULT
No, but 9 million more people voted this year. And I think that's a good thing. Lots of good people have tried to do this over the years and have failed.
So, you know, I'm just hat tipping.
GRAHAM CLULEY
He set the template now, hasn't he? I think everyone should go and try it.
CAROLE THERIAULT
No, you don't. You don't think that.
GRAHAM CLULEY
No, I'm going by your logic.
CAROLE THERIAULT
Now, as you said earlier, today is Election Day. And there has been a spate of related technical snafus that have been going on in the media. One of them was about racist robocalls.
CAROLE THERIAULT
There was a voter machine owner manual snafu where the password protection advice, and it was really bad, they were asking to keep the passwords really simple.
And there was this hacking fiasco in Georgia. So for those outside the loop, you should know that Georgia State is making a ton of political headlines.
And this is mainly because the fight between Democrats and Republicans for control of the governor's seat in this state is hotly contested.
Even head honchos like Obama and Trump both recently visited the state in support of their respective parties.
So in Georgia, the Secretary of State is an elected official who's responsible for supervising elections. Okay, so put that in your back pocket.
GRAHAM CLULEY
Okay, well, it's good to have someone in charge of the election to make sure there's fair play and, you know, everything is done by the book.
CAROLE THERIAULT
That sounds sensible. Now, earlier this year, Brian Kemp, said Secretary of State in Georgia, decided to run for the governor's seat.
Now, he wanted to do this without stepping down as Secretary of State.
MARK STOCKLEY
I bet he did.
CAROLE THERIAULT
But despite a number of strong requests—
MARK STOCKLEY
I've had an idea, guys. I've had an idea. I'm going to run, but I'm going to stay doing this job now.
GRAHAM CLULEY
Well, it will save the state money, right? Rehire a new Secretary of State to invigilate the election.
MARK STOCKLEY
Presumably there are some sort of ethics rules or laws, or is the ethics guy an elected official as well? Is that also Brian Kemp? He's also in charge of electoral ethics.
CAROLE THERIAULT
So as you guys are insinuating, many are questioning the conflict of interest here.
MARK STOCKLEY
I think it sounds fine.
GRAHAM CLULEY
It's perfect.
MARK STOCKLEY
Very sensible, very efficient government.
CAROLE THERIAULT
Now, you may know also that Brian Kemp has also been mentioned in many stories recently, not all favorable. Some are doing with stalling voter registrations in the state.
Recently, in fact, a federal judge told them to calm down on the voter registration requirements, potentially giving thousands more people who live in Georgia the right to vote.
MARK STOCKLEY
Oh, this is the guy who was— he was demanding— oh, I can't remember what it was now. He was demanding some sort of ID, wasn't he?
So he's projecting confidence is what you're saying.
CAROLE THERIAULT
Now, things are hot. Remember, the race is tight.
CAROLE THERIAULT
And it's Saturday evening.
GRAHAM CLULEY
The race is what?
CAROLE THERIAULT
Really? Wow.
GRAHAM CLULEY
So I misheard. Carry on.
CAROLE THERIAULT
The race is tight. Oh, Graham. Now, on Saturday evening, Brian Kemp, Secretary of State, the office that supervises Georgia elections, issues this statement. Okay.
And this was on the home page of the official Secretary of State website.
MARK STOCKLEY
Was it that Brian Kemp had already won?
CAROLE THERIAULT
"After a failed attempt to hack the state's voter registration system, the Secretary of State's office opened an investigation into the Democratic Party of Georgia.
Federal partners, including the Department of Homeland Security and Federal Bureau of Investigation, were immediately alerted.
While we cannot comment on the specifics of an ongoing investigation, we can confirm that the Democratic Party of Georgia is under investigation for possible cybercrimes."
MARK STOCKLEY
Now, this immediately makes me suspicious because nothing screams computer competence like the Democratic Party.
Noted for their expertise in securing important documents like emails.
GRAHAM CLULEY
Hillary's got a lot of time on her hands these days. Maybe she's been swatting up on how to do SQL injection attacks. You never know.
CAROLE THERIAULT
She's getting back at them. Of course, many are pointing out that the timing here is a tiny bit convenient with only two days before the election was going to take place. The voting.
So the Democrats, of course, are denying any involvement or wrongdoing, and of course they would. So think about it, if they had nothing to do with it, of course they would deny it.
But if they had something to do with it, deliberately or inadvertently, of course they would deny it two days before the election.
So it's really an irritating argument that this has come forward without any real evidence, and that's one of the big problems here.
There seems to be a distinct lack of evidence in the public sphere a Democratic Party is involved in any way in this quote unquote hack.
GRAHAM CLULEY
Well, it's just him who's saying it's a hack as well, isn't it?
CAROLE THERIAULT
Well, listen, yeah, I did a little digging.
In the Washington Post, a reporter said a spokesperson for the Secretary of State office said to her that Kemp's decision to investigate the potential cyber breach was proper because she said an email from Democratic Party officials contained software capable of trying to hack into the state's election system.
I think there's been someone who crafted this very carefully. Using such software is a crime, she said.
GRAHAM CLULEY
So I've heard a bit more of the Democrats' argument regarding this.
And what they've been saying is that someone who wasn't connected with the party had found a vulnerability on this voter registration page, not a hack.
They'd found a vulnerability as they found vulnerabilities in the past.
And they had emailed the Democrats to say, "I think you should know, on the state's vote registration system, there's a vulnerability here," which obviously is a bit of a worry.
And apparently, whoever found this vulnerability also informed the news media.
And the news media, because there have been a number of occasions when other vulnerabilities have been found on this particular website, which hasn't necessarily reflected terribly well on Brian Kemp, who is, of course, Secretary of State as well as running Smashing Security.
MARK STOCKLEY
So he's in charge of this website.
GRAHAM CLULEY
So he's in charge of this website. So it looks slightly embarrassing if there is a vulnerability.
And so if they are saying that the Democrats emailed them with software code or whatever, which could have exploited the web page, that may simply be vulnerability disclosure.
Right, it may simply be telling them, hey guys, there's a problem with this kind of code. You could access information on this website or exploit a vulnerability.
CAROLE THERIAULT
You know what, were that the case, Yes, I did read that, but were that the case, surely the Democratic Party would be coming really being loud about this and saying, here's the email we sent them.
GRAHAM CLULEY
Well, I don't know if it was just them communicating. I think there were other third parties as well who were in contact.
So I don't know exactly what was said where, and who might have said it. But certainly that's the argument which I'm hearing is, this wasn't a hack, no data was taken.
This is the counterargument. No data has been taken, so there's been no evidence of that. And maybe what this simply was, was a vulnerability.
And there was a story, I think it was in Politico, where they said silently the website got fixed for some of the vulnerabilities.
They actually tried it out themselves to see if they were able to access some of the information.
CAROLE THERIAULT
On one side, you could say, okay, it's a failed hack.
There's a little bit of hanky-panky going on between them, but there is a serious problem here because many US voters apparently visit the Secretary of State website for voting-related information.
Like, where do I vote? What hours are the polling stations open?
So that means that between Sunday and Tuesday night this week, Georgia voters who went to the Secretary of State website actually saw this cyberhacking message that I read earlier.
CAROLE THERIAULT
And it basically plainly says that Brian Kemp's opponent, Stacey Abrams, her party is being accused of cyberhacking. And how may that impact the vote across the state?
Interestingly, I didn't see any mention of this accusation on Brian Kemp's for governor website. Of course, he has a precedent of getting cyber attacks wrong.
In 2016, it was Brian Kemp who accused the Obama administration of raising unwarranted fears of election cyber attacks.
Then months later, he accused that same administration of a failed attempt to break through the firewall that secured voter registration information. So déjà vu, anyone?
The charge was completely debunked 6 months later. And in fact, actually, in November 2016, he actually turned down federal help to help secure his systems against cyber threats.
So there you go.
GRAHAM CLULEY
Well, by the time people hear this, it'll all be over, won't it? Either—
MARK STOCKLEY
Well, it may just be beginning.
GRAHAM CLULEY
Oh, really?
MARK STOCKLEY
Because if it's a narrow race and the Republicans win, I mean, that's quite a strong accusation to make against the Democrats.
Although the thing I struggle with, it's very easy to paint a picture where Brian Kemp looks like a shady character.
I mean, Brian Kemp sounds like he's doing a great job of painting himself to be a shady character.
But if you remove the Republican-Democrat labels from this and you just say, you know, one political party is accusing the other political party of trying to hack into a voter registration website.
Does that sound implausible? Frankly, no. You know, it's not a standard of behaviour that falls below where we've come to expect it.
So although it sounds from the story as if, you know, Brian Kemp is kind of a serial liar about these kind of hacks, it's not beyond the realms of possibility that one political party is trying to get one over on the other one with a bit of hacking.
CAROLE THERIAULT
No, I know.
And you know what, if you were in a race and two days before the vote you see something like this, is it your duty to tell your constituency, especially if it benefits you because you're in the race?
So this is the whole advantage of being a secretary of state and, you know, running for governor.
MARK STOCKLEY
I think I would probably have felt better about that announcement if it had come from the police.
GRAHAM CLULEY
Exactly right. Indeed.
CAROLE THERIAULT
It's very interesting because all our listeners already know what's happened, and we do not right now at all. So there's some weird time warping for you.
GRAHAM CLULEY
Many of us have worked in big companies, right? And we know that it only takes one person to make a boo boo to allow the hackers in.
Imagine running a company, hiring new staff and worrying that one of them might bring their bad password habits into the office. Horrendous nightmare.
That's one of the reasons why businesses small and large need a password management solution like LastPass Enterprise.
LastPass brings a vast array of features for enterprise users, including company-wide policies, reporting, user groups and roles, and new support for Microsoft Active Directory.
As an administrator, you can create highly secure passwords for your new starters right from the onset. Means no snafus.
Listeners can check it out for themselves by visiting lastpass.com/smashingsecurity. No more password snafus, no more boo-boos. Just LastPass.
CAROLE THERIAULT
Hey, Clue.
GRAHAM CLULEY
Hey, Carole.
CAROLE THERIAULT
Did you listen to my little bit about MetaCompliance and their e-learning?
GRAHAM CLULEY
Oh yeah, I heard that earlier in the show. Yeah, did you? Yeah, okay.
CAROLE THERIAULT
Well, have you signed up yet?
GRAHAM CLULEY
Well, no, I've been doing the podcast, Carole. I haven't had time to sign up for it, have I?
CAROLE THERIAULT
Well, women know how to multitask. Surely you can get a move on and sign up. We get 10% off. Just go to smashingsecurity.com.
You should know that website, /meta-compliance, and enter the code SMASHING with a G.
GRAHAM CLULEY
SmashingSecurity.com/meta-compliance, enter the code SMASHING. Terrific.
CAROLE THERIAULT
With a G. Cool.
GRAHAM CLULEY
And welcome back. And you join us at our favorite time of the show, the part of the show that we like to call Pick of the Week.
CAROLE THERIAULT
Pick of the Week. Pick of the Week.
GRAHAM CLULEY
Pick of the Week is the part of the show where everyone chooses something they like.
It could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website or an app, whatever they like.
Doesn't have to be security related necessarily.
CAROLE THERIAULT
Better not be.
GRAHAM CLULEY
And my pick of the week this week is not security related.
MARK STOCKLEY
Is it a book?
GRAHAM CLULEY
And it's not a book.
GRAHAM CLULEY
And it's not a TV show, a movie, a record, a podcast, a website.
MARK STOCKLEY
Is it Doctor Who?
GRAHAM CLULEY
No, it's not. It's definitely not Doctor Who.
CAROLE THERIAULT
Thank God.
GRAHAM CLULEY
I'm rather unimpressed with Doctor Who actually this year. We'll talk about that another time because my pick of the week is an erasable pen. I have a young son. He does homework.
He gets mad and crazy every time he makes a mistake and wants to rub it out. He doesn't always want to use a pencil.
MARK STOCKLEY
Give him a pencil.
GRAHAM CLULEY
No, I've given him a pen because he wants to color in with pen. He doesn't want to go over the lines.
GRAHAM CLULEY
Well, the kind of pen which I think he really likes are erasable pens. Have you come across erasable pens?
Graham, I hate to break this to you, oh, you're going to tell me these have been around for years?
CAROLE THERIAULT
Even way back in the '80s, we had erasable pens. I love that you just discovered them.
GRAHAM CLULEY
Do you know how erasable pens work, Carole?
MARK STOCKLEY
Has it got something to do with helium?
GRAHAM CLULEY
No, it has something to do with heat. The friction of rubbing out, as it were, heats up—
MARK STOCKLEY
Sets fire to the paper? No, no, no.
GRAHAM CLULEY
Heats up the ink to over 60 degrees and makes the ink disappear. This is with the Pilot FriXion, with an X, erasable pens. And you can make the ink reappear. Now you're impressed.
MARK STOCKLEY
With the pen?
GRAHAM CLULEY
If you put—
MARK STOCKLEY
You erase and then you write the thing back in?
GRAHAM CLULEY
No, no, no, no, no, no.
CAROLE THERIAULT
Fridge. Put it in the fridge.
GRAHAM CLULEY
Put it in the fridge. And if it goes below 10 degrees, it will reappear. This is also a spy communication device.
CAROLE THERIAULT
Yes, I love that.
GRAHAM CLULEY
Now you're interested.
CAROLE THERIAULT
Now I'm interested.
GRAHAM CLULEY
So you don't need Tipp-Ex to white out your mistakes.
MARK STOCKLEY
Did you say below 10 degrees?
MARK STOCKLEY
So the UK, basically. This is a fantastic device for—
GRAHAM CLULEY
Maybe it's minus 10.
MARK STOCKLEY
Reasonably hot countries.
GRAHAM CLULEY
Maybe it's minus 10. Hang on, because I'm getting upset with you now.
GRAHAM CLULEY
Maybe it's minus 10. I'm going to look.
CAROLE THERIAULT
No, because the fridge doesn't go to minus 10.
GRAHAM CLULEY
No, I've just Googled, or used an alternative to Google actually called Startpage. The ink reappears at temperatures of under minus 10 degrees centigrade. I made a mistake.
CAROLE THERIAULT
Oh, so it can't be the fridge, it's the freezer.
GRAHAM CLULEY
Well, all right, the freezer.
CAROLE THERIAULT
So you actually haven't played this game at all.
GRAHAM CLULEY
Someone rubbed out the minus sign in my notes, and that's why it said 10 degrees rather than minus 10. Anyway, I think this is very cool. It doesn't matter if they're new or not.
Just as I've recommended Beatles albums in the past, I can make my pick of the week anything from the history of creation if I wish.
CAROLE THERIAULT
Okay, listeners, you understand that after 100 episodes, Graham has got nothing else to pick. So if he writes on his skin, do you have to put him in the freezer for a bit?
GRAHAM CLULEY
No, I have not put my child in the freezer, Carole.
CAROLE THERIAULT
Good, good, good. Excellent parenting there.
GRAHAM CLULEY
Thank you very much. Pilot FriXion erasable pens. Some people love them, some people hate them. Some people say they had them when they were at school 30 years ago.
That is my pick of the week.
MARK STOCKLEY
Well done for battling through that, Graham.
CAROLE THERIAULT
I don't know why he's getting all angry.
MARK STOCKLEY
Well, I think it's because we just—
CAROLE THERIAULT
Did what he does all the time.
GRAHAM CLULEY
No, Carole, this is actually what you did last week as well on pick of the week.
I had a pick of the week and you criticised the pick of the week and you usurped it with your superior pick of the week.
You didn't like my 10 years, which had actually been recommended by a listener. Someone from Brazil had written in with his pick of the week.
CAROLE THERIAULT
Why are you flogging a dead horse? We did all this already.
GRAHAM CLULEY
I'm just saying, well, I'm just saying, yet again, you'll criticise my pick of the week. Get better, Mark.
MARK STOCKLEY
You better pick of the week.
GRAHAM CLULEY
Mark, good luck with your pick of the week.
MARK STOCKLEY
Okay, so I was going to recommend the first half of Yuval Noah Harari's Sapiens: A Brief History of Humankind, but something happened this morning.
There is a tips line for Naked Security.
People email things into Naked Security stories, and we received one this morning, which is PR press release, which I thought was very pertinent.
So today is midterm elections in the USA.
CAROLE THERIAULT
Obviously. Did you not hear my section?
MARK STOCKLEY
Elections can be boring. What? Okay, but there's good news. If you're not very excited about the election, somebody has emailed Naked Security's tips line with a way to liven them up.
MARK STOCKLEY
So for a bit of electoral excitement, there's— it seems that a popular adult webcam platform has come up with a new technology for the elections called Pollcast.
That's with a P-O-double-L, which is a platform that allows people with connected male and female sex toys—
CAROLE THERIAULT
Say no more.
GRAHAM CLULEY
No, I want to hear how it ties in with erections. I mean, the election.
MARK STOCKLEY
It seems— where shall I start?
Okay, it's a platform that allows people with connected male and female sex toys to sync them to the frequency of the vibrations coming from the results of today's elections.
CAROLE THERIAULT
Okay, I'm tuning out.
MARK STOCKLEY
So if your political party is winning, the vibrations get stronger, and if they're losing, the vibrations die down. So if you find elections dull, well, this is for you.
And apparently, apparently this comes hot on the heels of something else which was called BitCast, which was a similar technology that allowed you to enjoy your cryptocurrency investments in an entirely new way.
GRAHAM CLULEY
Unfortunately, they've been going down for a while, haven't they?
CAROLE THERIAULT
Mark, are you sure this was a tip? Do you have investments in this firm? It just sounded a bit like an ad. It sounded a bit—
MARK STOCKLEY
You too can enjoy the midterm elections.
CAROLE THERIAULT
Enjoy the elections like you never have before.
GRAHAM CLULEY
What worries me is the election TV shows, they tend to go on for about 8 hours, don't they?
CAROLE THERIAULT
What if, yeah, what if you feel those great heights again and again? Those desperate lows?
MARK STOCKLEY
It's a pretty low pace of election, isn't it?
CAROLE THERIAULT
Okay. I'm going to pass on that one, but thanks for the recommendation.
GRAHAM CLULEY
It's your first time on the show, isn't it, Mark?
MARK STOCKLEY
It's been fun.
GRAHAM CLULEY
Kroll, what's your pick of the week?
CAROLE THERIAULT
Mine's a great pick of the week, so beat this, Graham. Beat this. Isle of Dogs by the great Wes Anderson, director of Life Aquatic of Steve Zissou, an excellent film.
The Royal Tenenbaums, excellent film. Fantastic Mr. Fox, excellent film.
And now the even better Isle of Dogs came out earlier this year, and it's only now making our way to home cinemas. So of course I didn't leave the house to see.
Now it's set in Japan where dogs have been banned from the city by a bunch of cat-loving government types, and the story is about Atari Kobayashi, a 12-year-old Japanese boy who undertakes the dangerous journey to find his lost/stolen dog on the Isle of Dogs, also known as Trash Island.
Now, things I loved about this— all Wes Anderson films, incredible attention to detail, lovely, lovely, lovely. Characters are well thought through and they're imperfect.
Graham, it's you. I love them I love you. You know, imperfect and thought through.
Now what's really cool about it is the dogs speak in English, but the human, because it's set in Japan, the humans speak Japanese, but they don't conventionally translate the Japanese to English.
So as the viewer, you're kind of put in the position of the dog of only getting a few commands or a few phrases because you don't understand, you don't speak Japanese.
CAROLE THERIAULT
Yeah, but they— there's unconventional ways to get meaning, so they're using all the visual help they can to get the meaning across. It's very cleverly done.
There's a lot of thought in it.
GRAHAM CLULEY
Presumably in the Japanese version of the movie they've switched it round.
MARK STOCKLEY
So what you're saying is in the Japanese version, the Japanese people can't understand what their dogs are saying?
CAROLE THERIAULT
Yeah, Graham, they wouldn't have changed it. Exactly.
MARK STOCKLEY
That's an incredibly radical way of looking at the world, so that the humans don't understand what the dogs are saying. The dogs are speaking a different language from the humans.
CAROLE THERIAULT
In Japan, they can— they relate to the people.
GRAHAM CLULEY
What? No. To have the same film experience in Japan, if you were Japanese watching this movie, they would have to change— they would have to redub it.
GRAHAM CLULEY
Because otherwise you'd just hear the humans speaking. You wouldn't hear what the dogs were saying.
CAROLE THERIAULT
Yes. Well, you can hear it.
GRAHAM CLULEY
You can hear it, but that's not the movie.
MARK STOCKLEY
Graham, is there something you want to— can you speak to dogs?
GRAHAM CLULEY
That's a different movie.
CAROLE THERIAULT
Yes, okay, I have a suggestion. Go flipping watch it.
GRAHAM CLULEY
I should have done it in Welsh.
CAROLE THERIAULT
Shut up, shut up, shut up. You're trying to hack away at my idea. Just— you can't.
Go watch it, and you're gonna— next week you're gonna say, okay, Carole, you know what, you were right. It was really amazing, and I loved it.
GRAHAM CLULEY
Your husband— your husband speaks Japanese.
CAROLE THERIAULT
Yes, we watched it together.
GRAHAM CLULEY
Oh, so what was his experience like?
CAROLE THERIAULT
Oh, probably different than mine.
GRAHAM CLULEY
Well, I'm very interested.
CAROLE THERIAULT
Probably got a few more expressions. Yeah, why don't you watch it if you're interested?
GRAHAM CLULEY
Well, I don't speak Japanese.
MARK STOCKLEY
Oh, just ask John.
CAROLE THERIAULT
Did you see Fantastic Mr. Fox?
GRAHAM CLULEY
Yes, I did.
CAROLE THERIAULT
Was it fantastic?
GRAHAM CLULEY
It was good. Yeah.
CAROLE THERIAULT
You just thought it was good?
MARK STOCKLEY
The title is the review.
GRAHAM CLULEY
It was wonderful, but it wasn't called The Wonderful Mr. Fox. The wonderful Wiley folks. It was called the Fantastic— it was terrific. Superb.
CAROLE THERIAULT
Good. Well, I think you're going to like this even better.
GRAHAM CLULEY
Well, that just about wraps it up for this week. Mark, I'm sure lots of people having heard about your pick of the week would like to follow you online and connect with you.
What's the best way for folks to do that?
MARK STOCKLEY
You can follow me on Twitter. My Twitter handle is Mark Stockley.
GRAHAM CLULEY
Oh, brilliant. And you can follow us on Twitter as well at Smashing Security, no G.
Twitter wouldn't allow us to have a G, and that's a good idea because occasionally we tweet out little codes so you can save some money in our online store.
CAROLE THERIAULT
And funny things occasionally, sometimes funny.
GRAHAM CLULEY
Oh yes, some fun stuff as well. If you like the show, make sure to subscribe in Apple Podcasts, your favorite podcast app, so you don't miss any episodes in future.
Be sure to tell all of your friends as well. And if you're really keen, you can even rate and review us on Apple Podcasts.
CAROLE THERIAULT
Actually, you don't have to be that keen. I'm okay if you're medium keen. Just tell us you're keen.
GRAHAM CLULEY
Some people aren't keen at all and they leave us reviews on Apple Podcasts.
MARK STOCKLEY
Well, if we could just get those people to write it in erasable pen, we could just go along after them and rub it out.
GRAHAM CLULEY
Until next time, cheerio.
CAROLE THERIAULT
Bye. Bye.
GRAHAM CLULEY
I think that's a record.
CAROLE THERIAULT
Okay, well, allons-y with the editing, eh, Graham?
I hope tonight, tonight, while you're lying cozily in bed this evening, it might be 4 AM, or tomorrow, anytime before midnight tomorrow.
I want you to picture Graham and I feverishly trying to pull this together into something coherent. Oh gosh, I love you both.

 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.



