
A supply chain attack is believed to have been responsible for surreptitiously inserting a backdoor into widely used server management software.
In July 2017, a financial institution detected suspicious DNS requests related to the processing of financial transactions. The organization subsequently contacted Kaspersky Lab, whose researchers launched an investigation into the matter. Those experts traced the requests to a sever management software package developed by NetSarang.
Headquartered in the United States and South Korea, NetSarang Computer Inc. specializes in server management tools designed for large corporate networks. Analysis shows that someone added a fragment of code to nssock2.dll in some of NetSarang’s products around 13 July. That code collects basic information about the computer until an attacker activates it by sending a special package to a first-tier command-and-control (C&C) server.
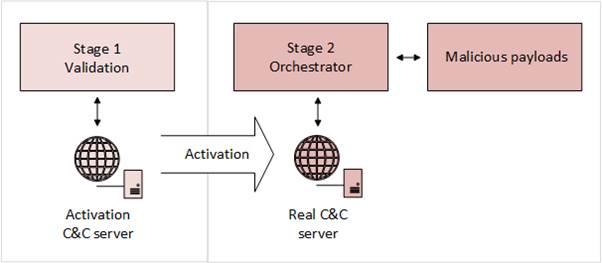
At that point, the backdoor runs and gets to work. Kaspersky Lab’s Global Research and Analysis Team explains what the malicious component, dubbed Backdoor.Win32.Shadowpad.a or “ShadowPad” for short, can do:
“Our analysis indicates the embedded code acts as a modular backdoor platform. It can download and execute arbitrary code provided from the C&C server, as well as maintain a virtual file system (VFS) inside the registry. The VFS, and any additional files created by the code, are encrypted and stored in a location unique to each victim. The remote access capability includes a domain generation algorithm (DGA) for C&C servers which changes every month. The attackers behind this malware have already registered the domains covering July to December 2017, which indirectly confirms alleged start date of the attack as around mid July 2017.”
The security research team has successfully confirmed one activated payload in Hong Kong.
Following its analysis, Kaspersky Lab notified NetSarang of the attack. The server management software vendor responded by issuing a statement about the backdoor and urging customers to update their software to newer, clean versions.

Since the malicious code was signed by a NetSarang certificate and added to all software packages, a supply chain attack was most likely responsible for this infection.
Supply chain threats plague anyone and everyone in the hardware and software biz. (Even mobile device vendors.)
With that said, it’s up to organizations to review their supply chains and make sure every partner with which it works has strong security measures in place that in part deter malicious insiders. Organizations should also consider conducting audits on a semi-regular basis to determine whether their partners are compliant with their security expectations.


