There is a simply fascinating report in today’s New York Times describing how the Stuxnet virus was created by the USA to target an Iranian nuclear facility, but accidentally escaped into the wider world.

The report comes from David E. Sanger, the Chief Washington correspondent at The New York Times and author of the upcoming book “Confront and Conceal: Obama’s Secret Wars and Surprising Use of American Power”.
Here is a quick summary of the claims made in the report:
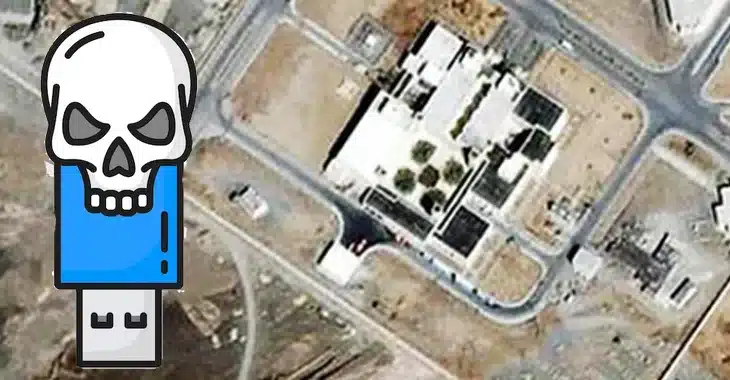
- Feeling threatened by the possibility that Iran would enrich uranium at a nuclear facility at Natanz that could be used to create weapons of mass destruction, US President George W Bush initiated a plan to seize control of computer systems at the plant.
- The first part of the plan (dubbed “Olympic Games”) was to embed spying code that would send back information about the computer systems’ operations and draw up a blueprint of how the computers controlled centrifuges at the plant.
- After months of waiting for the information to be relayed, the National Security (NSA) and Israeli computer experts created a worm (Stuxnet) that would allow them to attack from within the plant.
- According to the report, the USA felt compelled to involve Israel in the plan to prevent the country launching a pre-emptive military strike of their own against the nuclear facility.
- The USA secretly built a replica of Natanz’s computer systems, including centrifuges handed over by Libyan leader Colonel Gaddafi in 2003, to test their malware.
- Tests were successful, and the worm’s orders to slow down and speed up the centrifuge’s delicate parts caused them to suffer damage. At one point, it’s said that debris from a damaged centrifuge was laid across the conference table at the White House’s Situation Room to demonstrate the malware’s potential power.
- With the malware deemed ready, it was introduced into the Natanz plant via infected USB memory sticks by spies and unwitting workers with physical access to computer systems.
- As centrifuges failed, Iranian workers would close down the systems looking for signs of sabotage – not realising that their computer systems were compromised.
- Days before Barack Obama was inaugurated as US President, George Bush successfully urged him to continue the classified “Olympic Games” program.
- The attacks on the nuclear plant’s systems continued, but potential disaster struck in mid-2010, when it became clear that “an error in the code” had allowed Stuxnet to spread beyond Natanz’s systems and infect computers in the outside world.
David Sanger says his account of the American and Israeli attempt to undermine Iran’s nuclear program with malware is based upon interviews with current and former officials who were involved in the operation. None of them have allowed their names to be published.
 We’ve reported before on how US defence chiefs have squirmed when quizzed about whether America was responsible for writing Stuxnet, and according to Sanger the operation remains highly classified.
We’ve reported before on how US defence chiefs have squirmed when quizzed about whether America was responsible for writing Stuxnet, and according to Sanger the operation remains highly classified.
One thing seems certain. Stuxnet is old news. Even the recently discovered (and much hyped) Flame malware isn’t an effective weapon today. There seems little doubt that state-sponsored cyberweapons (if that is indeed what Stuxnet was) continue to be developed – and chances are that it’s not just the USA and Israel who are developing them but other developed countries.
Read the full story on the New York Times website. It certainly makes for fascinating reading.