
Splunk, a utility that allows IT administrators to search and analyse their organisation’s log files, has issued a warning to some of its users that their passwords were exposed by accident.
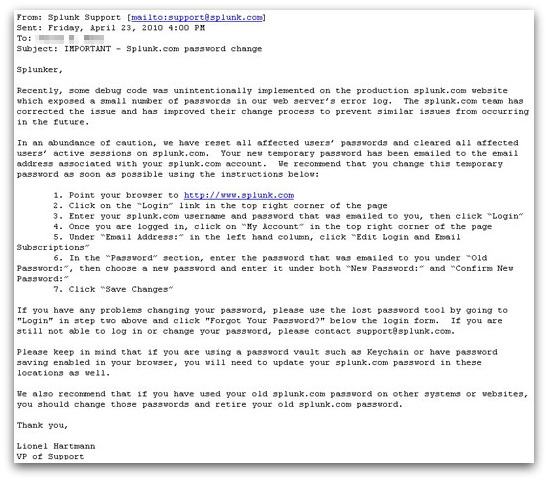
I wasn’t able to find mention of the incident on Splunk’s website, but a few affected users have Twittered about it, and a Clu-blog reader forwarded me an email from Splunk that tells more of the story:
Recently, some debug code was unintentionally implemented on the production splunk.com website which exposed a small number of passwords in our web server's error log. The splunk.com team has corrected the issue and has improved their change process to prevent similar issues from occurring in the future.
In an abundance of caution, we have reset all affected users' passwords and cleared all affected users' active sessions on splunk.com. Your new temporary password has been emailed to the email address associated with your splunk.com account. We recommend that you change this temporary password as soon as possible using the instructions below.
It’s not clear from the warning sent out by Splunk how long passwords were exposed for, but there’s obviously a concern that if hackers had managed to stumble across the login details they could have tried to use them on other wesbites where users might use the same password.
In this case that could have been particular bad for enterprises, as Splunk’s typical users have key roles inside an organisation’s IT infrastructure and may have access to a number of critical systems and sensitive data.
Of course, it’s bad practice to use the same password on different websites – but that doesn’t stop far too many people from doing it.
Splunk’s action of changing affected users’ passwords was probably the right one – rather than waiting for users to do it themselves.
Update: Splunk’s blog has been updated to include information about the security incident. Splunk claims that it is demonstrating an “abundance of caution” by resetting its users’ passwords.


